This month, the KubeSec Enterprise vSummit brought together hundreds of DevOps and security practitioners to discuss the state of cloud native security and share best practices. As with previous events, the focus was on enterprise experiences in securing real-world deployments involving containers, Kubernetes, serverless functions, and more. The summit covered a wide range of topics, including supply chain security, the journey to a thriving DevSecOps function, and the expanding threat landscape.
What is KubeSec?
The KubeSec Enterprise Summit has become a key industry event taking place on Day Zero at KubeCon. Back in 2018, we launched KubeSec with the vision to help cloud native practitioners at all levels from across the community to learn, connect, and exchange perspectives around Kubernetes security. From the start, KubeSec has been extremely successful, with the number of participants in the physical events in Seattle, Barcelona, and San Diego (pre-pandemic) exceeding all our expectations.
This year, KubeSec ran as a full-day virtual event, with an excellent lineup of speakers from organizations including Microsoft, AWS, Enterprise Strategy Group (ESG), PNC Bank, and Accenture.
Here are some overarching themes from the event that we think are worth highlighting.
Has Kubernetes security evolved?
While in 2018 we were discussing the need for Kubernetes security, now we’ve moved into more advanced topics like securing mission-critical cloud native applications at scale. This underscores the speed with which Kubernetes has transformed enterprise environments.
Over the past few years, we've seen a dramatic evolution of both Kubernetes itself as well as the security offerings available around it.
Aqua co-founder and CTO Amir Jerbi shared his vision on where Kubernetes security is going next.
As attacks targeting cloud native environments are getting more sophisticated, security is getting deeper and more holistic. Today, it’s not enough to just scan container images for vulnerabilities or harden the environment, as it was in the early days of the container revolution. Organizations are realizing that runtime protection is essential and are actively defending Kubernetes workloads to detect and respond to attacks in progress.
And instead of using siloed tools for each phase of the application life cycle, the industry is starting to talk about integrated platforms, such as cloud native application protection platforms (CNAPPs) that combine all these security capabilities together.
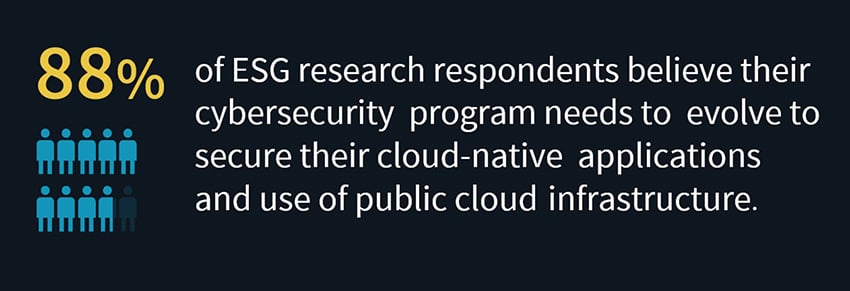
Doug Cahill, vice president and senior analyst at ESG, laid out the analyst perspective on the question, “Is cloud native security reaching a level of maturity?” The short answer is, “No”. Despite taking steps to address security risks of the new technology stack, most organizations are still facing organizational challenges and aren’t fully ramped up on security tooling for the cloud native world.
Complexity is intensifying
A big theme this year was also the growing diversity and complexity of cloud native environments. Organizations are increasingly using containers across multiple environments, so enterprise infrastructure today might include bare metal, legacy applications on VMs along with container- and serverless-based applications, deployed on-premises, in public clouds, or in a hybrid environment.
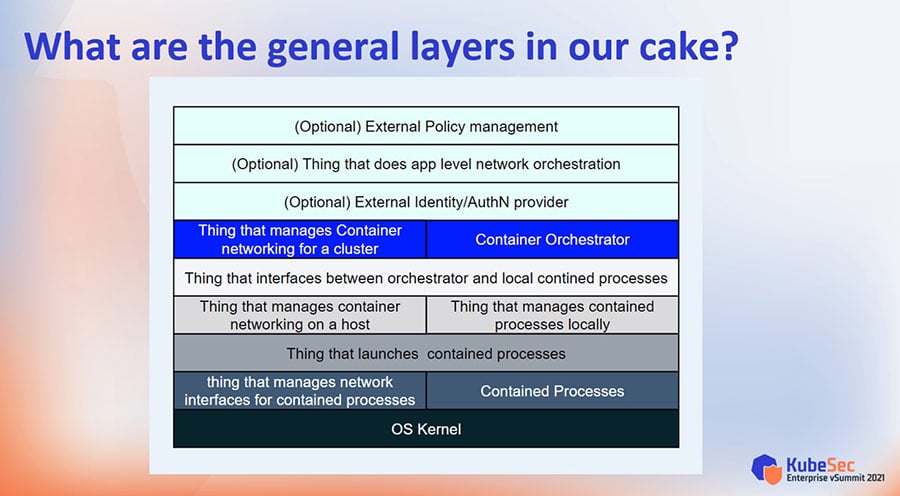
To visualize the cloud native complexity, the concept of a layer cake might come in handy, which was outlined in the talk by Rory McCune, Cloud Native Security Advocate at Aqua.
From a technical perspective, the cloud native stack is complex, multi-layered and highly dynamic. There are a lot of moving parts and different layers of abstractions on top of underlying systems, such as container processes, networking, orchestration, and external policy management. All these components can be (and usually are) managed by different commercial and open source solutions. As companies scale out their Kubernetes-based infrastructure, it’s important to pay attention to the edges where these layers meet and where the resulting security issues may emerge.
The Kubernetes project has taken a conscious decision not to fill all the security gaps themselves, so as time goes by, we'll see more external systems and tools emerging to support different aspects of security in Kubernetes.
During the panel with speakers from IBM Power, Accenture, and KPMG on moving legacy applications to cloud native, a few interesting trends came up:
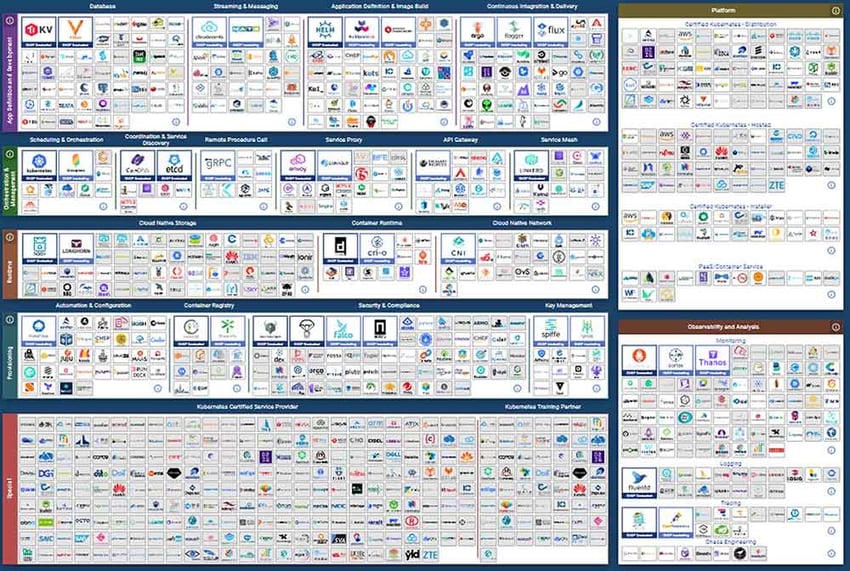
- The cloud native ecosystem is exploding. The sheer number of separate cloud native projects and tools can be daunting, especially to people new to cloud native computing. A large variety of tooling makes it hard for organizations to determine what is really required to secure their stacks. Focus should also be placed on people, processes, and technology.
CNCF landscape October 2021: 989 cards with a total of 2,850,984 stars, market cap of $15.8T and funding of $27.7B.
Source: CNCF Cloud Native Interactive Landscape
- “Everything-as-Code” revolution. In addition to infrastructure-as-code (IaC), organizations are adopting new concepts and methodologies, such as policy-as-code, security-as-code, and configuration-as-code. If you aren’t treating and defining everything as code, you’re lagging.
Kubernetes is evolving fast, with each release introducing new features and deprecating others. On that note, Norman Johnson, VP of DevOps at PNC Bank, gave a great breakdown of the tools that can be used to replace Pod Security Policies (PSP), deprecated in Kubernetes v.1.21. There are multiple powerful tools out there, such as Open Policy Agent (OPA), Kyverno, and Kubewarden, that can suit your policy enforcement needs in Kubernetes.
Another recurring theme was the Kubernetes security knowledge gap. Madhu Akula, Security Engineer at Miro, demonstrated his open source project Kubernetes Goat – an intentionally vulnerable cluster environment to learn and practice Kubernetes security. With tons of vulnerabilities taken from real-world attacks and covering dozens of scenarios, this playground is a useful tool for assessing and improving your cloud native security posture.
How are the attackers doing?
As always, a security event’s agenda wouldn’t be complete without a discussion on the ever-changing threat landscape. Assaf Morag, Lead Data Analyst at Aqua, shared the insights of Team Nautilus into the evolution of container attacks in the wild.
The threats targeting cloud native environments are rapidly accelerating and advancing. While in 2019 attacks were simple and straightforward, today attackers are using more sophisticated techniques to avoid detection and achieve persistency in the victim’s environment. For example, in a recent campaign detected and tracked by Team Nautilus, the threat actors deployed kernel space and user space rootkits to bypass defense measures and hide malicious processes.
This talk was a good reminder that attackers are constantly finding new ways to target and exploit cloud native technologies. In the attacks we're seeing, they’re uploading malicious binaries, running processes directly from memory, and using backdoors to increase their gain from the attack. More often than before, their goal is not just to mine cryptocurrency (which is still prevalent), but to cause more sinister damage.
See you next year!
This year’s KubeSec was full of valuable insights, best practices, and first-hand experience in deploying secure applications on Kubernetes. Sign up to the KubeSec community to get updates about future events.