Last month at DockerCon Europe we learned that container adoption is rising to a whole new level with 24 billion container downloads and 77K% growth in Docker job listings. This is when Docker also announced that it now supports Kubernetes. Combine this with the recent news from The Cloud Native Computing Foundation that 30 new members joined the foundation recently and it’s clear that containers are extremely popular.
Over the past few months, we conducted a survey in which we asked 512 IT enterprise professionals about their containers usage habits, their roles and the adoption level of containers, and aspects of security. We were looking to understand how all this affects security, and what approaches organizations are taking to handle security around their container deployments. What we found out is that people in different roles approach containers in different ways and focus on different areas when it comes to security. In some enterprises containers are only used in development stage, while in others they are already rolling containers in production. While in some enterprises DevOps teams are the ones in charge for implementing container security checks and controls, in others it’s the responsibility of the security team. In short, different companies use containers and their tools in a different way.
One of the primary objectives of this survey was to learn about what our respondents see as key focus areas for security – i.e., what are the first things that require attention. We asked about the use of trusted images, scanning for vulnerabilities, secrets management, isolation on the host, network segmentation for containers and runtime visibility. What we found out is that detecting vulnerabilities in images/code and managing secrets were the two main focus areas for most respondents.
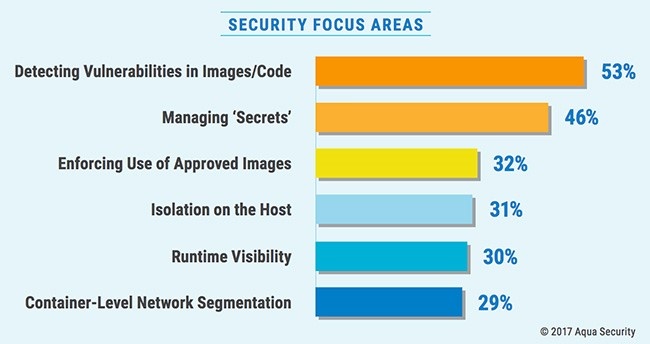
In overall 53% rank vulnerabilities in images and code as a top focus, changing to managing ‘secrets’ for those running multiple apps in production or those who are developers. Interestingly, looking specifically at the responses of security professionals: while they also rank vulnerabilities and secrets as their top two areas, they ranked network segmentation markedly higher than the average, at 40%.
Looking at container adoption level in the organization, what stands out is that among organizations with multiple containerized applications in production, secrets management was noted by a whopping 58% (higher than vulnerabilities) – presumably because it’s a more difficult challenge to manage secrets across multiple applications, requiring a more systemic approach.
Also, 34% of those with applications in productions noted runtime visibility as something they’re focusing on, contrasted with only 26% among those who have not yet deployed container apps.
This comes as no surprise and correlates to what we hear from our customers and see in the market today. At the recent Modern App Security Requires Containers expert panel at DockerCon Europe, one of the questions was “If I’m using the basic tools to run containers, what am I doing wrong?” The panelists mentioned image scanning as the first thing you need to do in order to secure containerized applications. Or looking for known vulnerabilities (CVEs), because having vulnerable code is leaving your applications open to unsophisticated attacks. Our very own Liz Rice then continued by talking about the need for managing the container’s secrets in a right manner, i.e. retrieve the secret only when the container runs and in a way that’s only accessible to the relevant container.
So the experts and the masses agree on this point, that the main two focus areas in container security today are scanning for vulnerabilities and secrets management. Once these rather basic areas will be more readily addressed by enterprises, we believe that the focus will move on to more complex focus areas such as container network segmentation and runtime protection.