Seems like only yesterday we announced Aqua CSP v1.1, but with customer requirements flowing in and our commitment to coming out with a new version every couple of months, Aqua 1.2 is out. This version is packed with dozens of new features and UI improvements, but I wanted to highlight the key new features.
Threat Mitigation Policy
We added a whole layer of threat mitigation capabilities that can be applied across a customer’s environment, regardless of specific container, host and application-based policies.
You can now benefit from advanced threat mitigation. Based on a cyber intelligence feed, we can detect and prevent containers from performing malicious activities that can be a sign of malware contamination, like actively scanning the network (port scanning, host scanning) or accessing IPs with a bad reputation that can be a sign for command and control or fraud attempts.
Also new: We’ve been providing default least-privilege security profiles for popular official images, to allow customers to run them in a more tightly controlled manner right out of the box. Now, you can select one of these as your default for all containers, which would provide better security for until you apply behavioral profiles or if you decide to run with defaults all the way. For example, you can set a default policy that prevents containers from running executables that are not part of the image. Then, you can create a specific security profile that further restricts running executables for a certain image to include only a subset of specific executables.
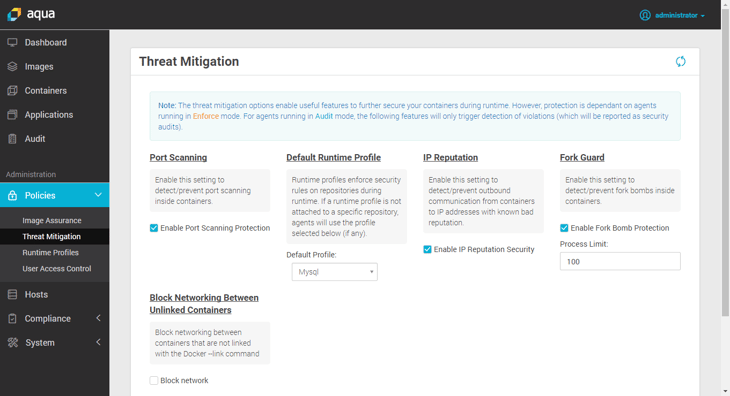
This is an area of the Aqua CSP that we expect to expand significantly in future releases, so watch this space...
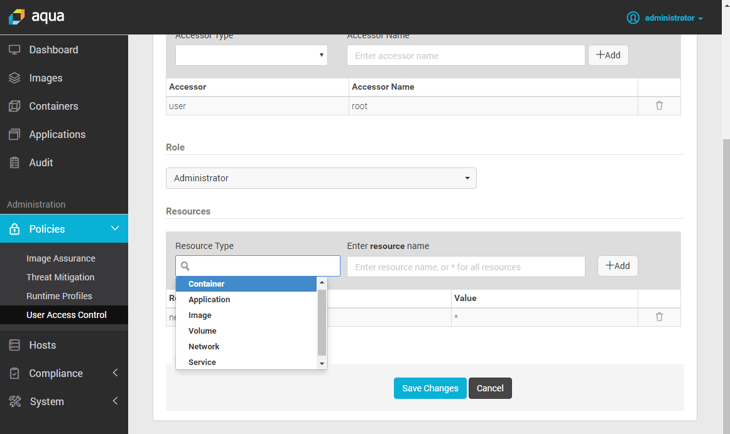
Tightening of User Access Control Policies
Aqua’s already granular user access control policy engine has been enhanced even further, now allowing to control which users and roles have access not only to specific containers, images and applications, but also to storage volumes and network devices.
This kind of control over user access is truly unprecedented, and is particularly important in multi-tenant environments or where regulatory compliance requires limiting access to specific resources.
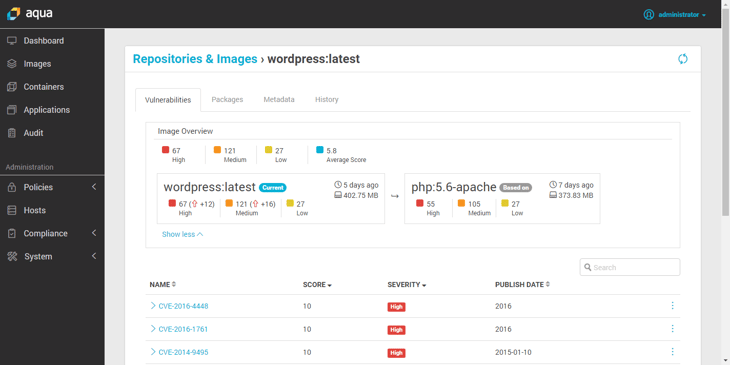
Improvements in Image Vulnerability Scanning
Many of our customers have users who store Docker images locally, on the host running Docker, and not in registries (either officially or for reasons of convenience). Aqua now discovers these “orphaned” images and scan them as part of its Continuous Image Assurance methodology. So even such distributed or “rogue” images will not evade proper scanning and policy enforcement.
We also improved the scan results reports that we provide, that are now more detailed and separately display CVEs that are found in the base image vs. the CVEs found in the application layer.