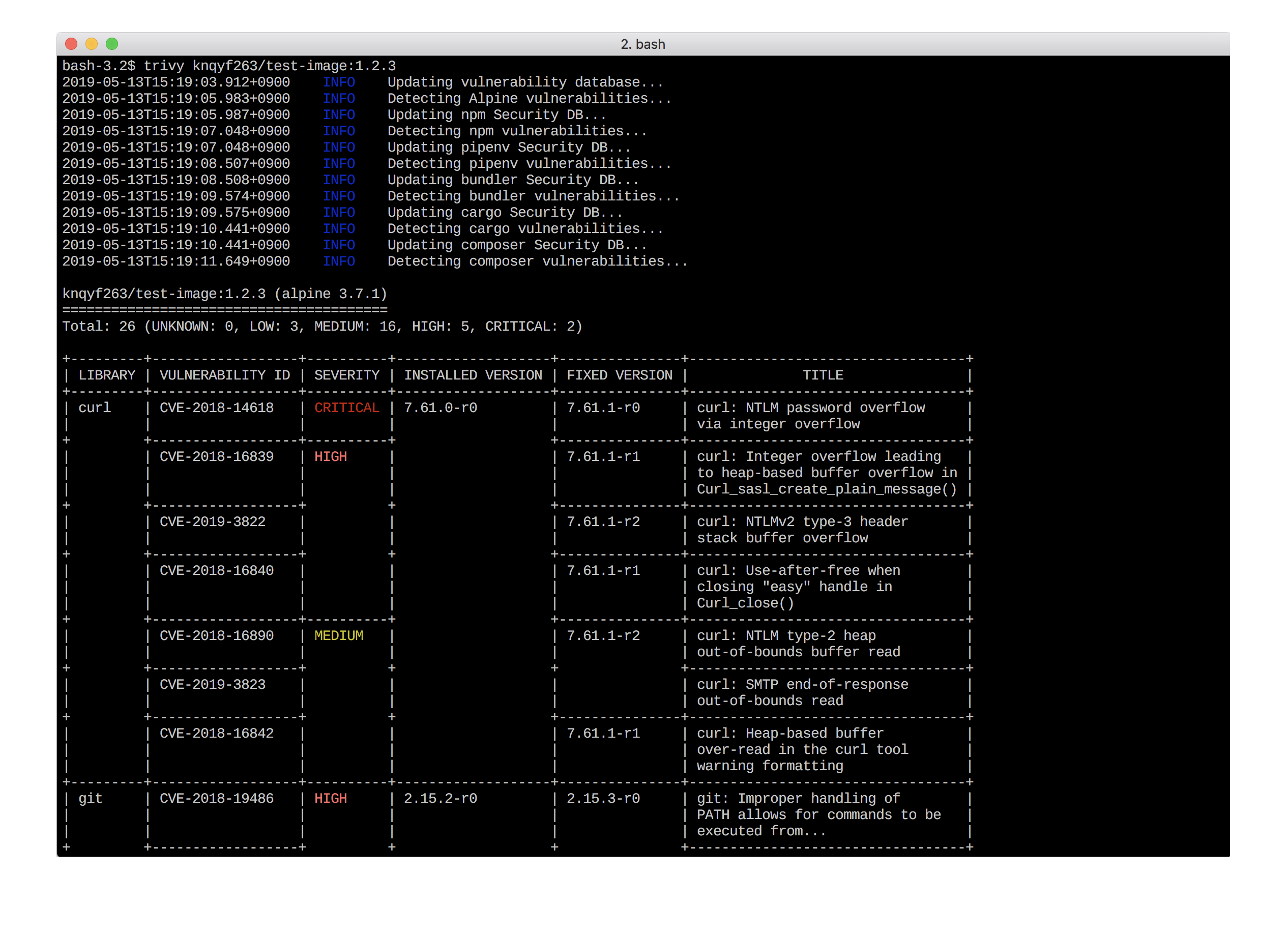
If you’re interested in container image vulnerability scanning, there’s a good chance that you have come across the Trivy open source scanning tool. This project has been receiving rave reviews for its ease-of-use, as well as its comprehensive vulnerability tracking across both OS packages and language-specific dependencies.
I’m absolutely delighted to welcome Teppei Fukuda, the developer behind Trivy, to the Aqua Security team. He’s bringing his expertise in vulnerabilities to our team, and the Trivy project is moving to the Aqua portfolio.
Will Trivy remain open source?
Absolutely! We brought Teppei on board because we believe that Trivy is, by a significant margin, the best open source vulnerability scanner out there. We want to support it and help it grow. Teppei will continue to work on Trivy as part of our growing open source engineering team.
For most existing Trivy users the move to Aqua Security should be transparent, but if you have previously installed Trivy onto a server, you may need to update your package manager and any scripts to refer to its new home. We have prepared some Migration notes to help.
But Aqua already has a great vulnerability scanner, right?
Yes! Aqua CSP includes an enterprise-grade image scanner, which is widely regarded as best-in-class, and we also offer a subset of its functionality in our free-to-use edition, Microscanner. Over the next few months we’ll be working to take the best parts from these and from Trivy, to offer the most comprehensive and easy-to-use solutions for both open source and commercial users.
What will happen to Aqua Microscanner?
The plan is to retire Microscanner eventually, in favour of Trivy, but there are a couple of enhancements that need to be applied to Trivy first, to maintain the experience for our existing Microscanner users.
The first is to support the ability to embed a Trivy scan in a Dockerfile. In Microscanner you trigger a scan by including it as part of the Dockerfile, and this approach has proven quite popular because it means an individual can introduce image scanning without having to modify the CI/CD pipeline.
Another advantage of both Microscanner and the commercial version of Aqua is that they query a remote vulnerability database, known as the Aqua CyberCenter. This approach saves downloading an entire copy to the local machine, which can be very time-consuming. We’ll add a way for Trivy to work in a remote mode like this.
Do Trivy and Microscanner show the same results?
Right now, you will find differences if you compare the output from Trivy and Microscanner for the same image. The reasons include the fact that they don’t use the exact same set of data sources, and they take varying approaches to things like whether a fix is available, or when the vendor has marked as an issue as won’t-fix. Over the next few months we will be clarifying this and taking the best of all worlds to ensure that the results are consistent.
What about Aqua’s enterprise scanner?
The Aqua Cloud Native Security Platform includes Aqua’s full-feature scanner, which will continue to offer the most comprehensive results. It includes extra functionality such as identifying sensitive data and malware built into an image, and uses additional threat intelligence for language packages coming from several sources, including our own research team. It’s easy to integrate into a variety of CI/CD pipeline tools, and to scale according to scanning demands, and it’s fully supported by our customer support team. When used within the Aqua Cloud Native Security Platform, scan results inform the broad and powerful policy enforcement that we offer our commercial customers – enabling them to verify the use of trusted images, profile and approve container behaviour, and so on.
How do I try Trivy?
See for yourself how easy Trivy is to use, by trying it out on your favourite container images.
It’s available now from https://github.com/aquasecurity/trivy.