The new Trivy release is out! As ever, there are tons of exciting updates and features, such as role-based access control (RBAC) and Helm chart scanning, support for custom extensions, a Trivy Operator Lens integration, and many more. Read on for feature highlights and try them out.
RBAC scanning
RBAC scanning has been a long-requested feature, and now it’s available in Trivy v0.29.0.
RBAC allows us to define user privileges and access rights such as who is allowed to access, use, modify, or delete a resource. For this, RBAC uses Kubernetes Roles and ClusterRoles. However, it can be hard to keep track of all the service accounts in your cluster and their respective access rights.
With Trivy RBAC, you can get a simple overview of the accounts and their respective privileges:
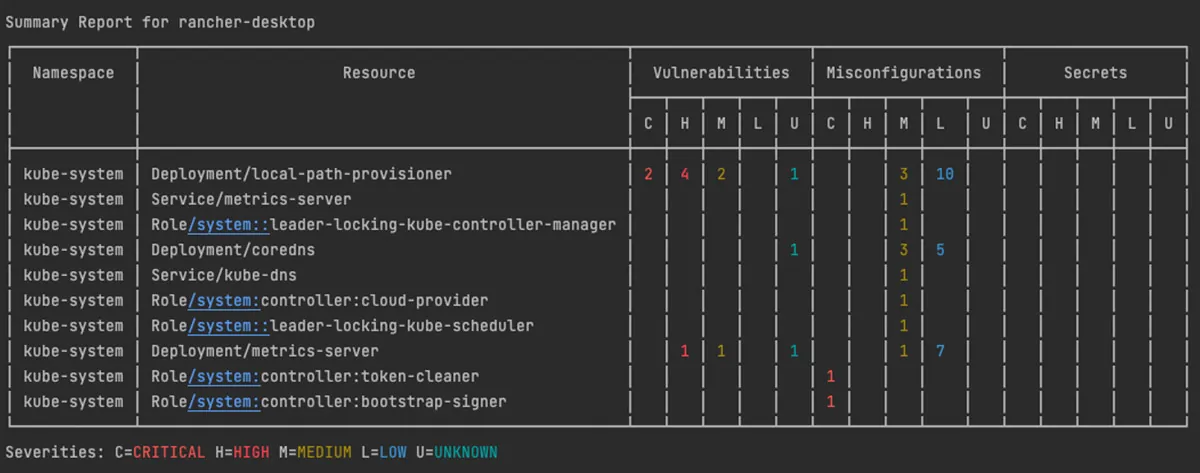
RBAC scan in Trivy
Trivy is now extensible
Vulnerability scanners with software composition analysis (SCA) assume that the existence of a package with a vulnerable version indicates that your application is vulnerable. However, in many cases, a vulnerability might not actually affect your application, depending on the runtime version you’re using, middleware configuration, or complex conditions. As a result, many vulnerability scanners can show a lot of false positives.
For example, an application with the Spring4Shell vulnerability (CVE-2022-22965) wouldn’t be affected with JAR packaging and an old Java 8 version, even though it uses a vulnerable version of Spring Framework.
To enable more flexible detection, Trivy supports WebAssembly modules, which can inject custom detection into scanning.
In the following example, a module for Spring4Shell detects the Tomcat and Java versions in addition to the version of Spring Framework. Then, the module decreases the severity because the vulnerability conditions aren’t met and this image isn’t affected by this vulnerability.
$ trivy module install ghcr.io/aquasecurity/trivy-module-spring4shell
$ trivy image ghcr.io/aquasecurity/trivy-test-images:spring4shell-jre8
2022-06-12T12:57:13.210+0300 INFO Loading ghcr.io/aquasecurity/trivy-module-spring4shell/spring4shell.wasm...
2022-06-12T12:57:13.596+0300 INFO Registering WASM module: spring4shell@v1
...
2022-06-12T12:57:14.865+0300 INFO Module spring4shell: Java Version: 8, Tomcat Version: 8.5.77
2022-06-12T12:57:14.865+0300 INFO Module spring4shell: change CVE-2022-22965 severity from CRITICAL to LOW
Support for GitHub dependency snapshot
GitHub just released GitHub snapshots, and Trivy already integrates with it. The GitHub snapshot model highlights all dependencies of a repository. You might already be familiar with Dependabot, a GitHub feature that enables automatic updates to repository dependencies.
With GitHub Snapshots and Trivy, you can automatically update dependencies based on the vulnerabilities discovered by Trivy. Learn more about it in the GitHub documentation.
Config scans for Helm charts
As you might already know, Trivy can scan infrastructure as code and other configuration files for misconfiguration issues. Helm is a popular Kubernetes packaging and templating tool that helps deploy Kubernetes manifests defined in Helm charts to a Kubernetes cluster.
With the newest Trivy release, you can now scan any Helm chart directly for misconfiguration issues before deploying those resources to your Kubernetes cluster.
Once you run the Trivy config command, the Helm charts are rendered into Kubernetes manifest files. The manifests can then be scanned for configuration issues.
trivy config <path to your Helm Chart>
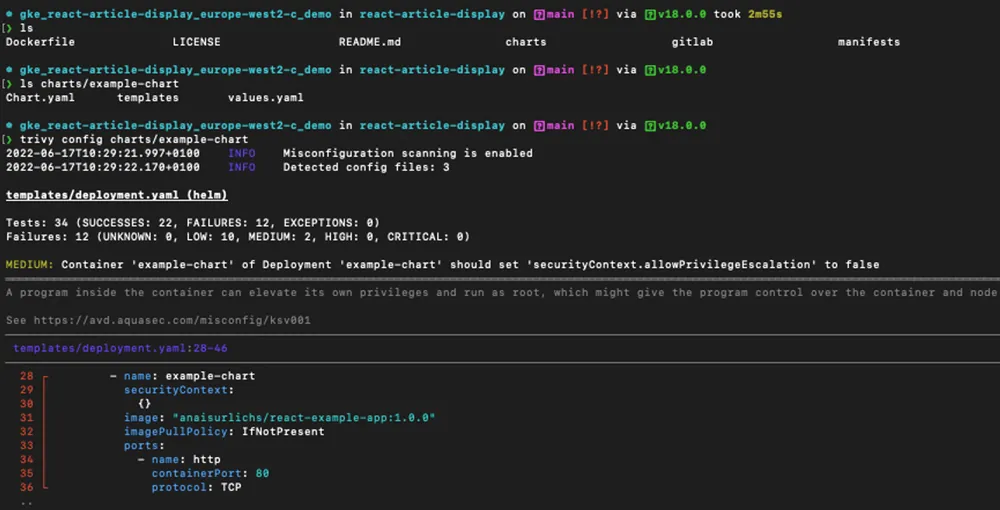
Trivy config command performed on Helm Chart
Trivy Operator Lens integration
To access vulnerability reports and other security scans, you need to query your cluster for the specific resource. The output is generally displayed as custom resource definitions (CRDs), which provide detailed information of the scan.
Lens is a popular integrated development environment (IDE) for Kubernetes, which many developers use to manage their Kubernetes clusters in a simple graphical user interface. Lens can be extended to show additional Kubernetes-related information right in the app.
We’ve now released the Trivy Operator extension for Lens. Once you’ve installed the integration into your Lens client, you can:
- Access security scans through the Lens dashboard in a more visual manner
- Receive report summaries
- Query security scans through Lens
For more details and installation, go to the Trivy Lens GitHub repository.
We’d like to thank the amazing member of our community Isla Nublar Security, who contributed a lot to this extension.
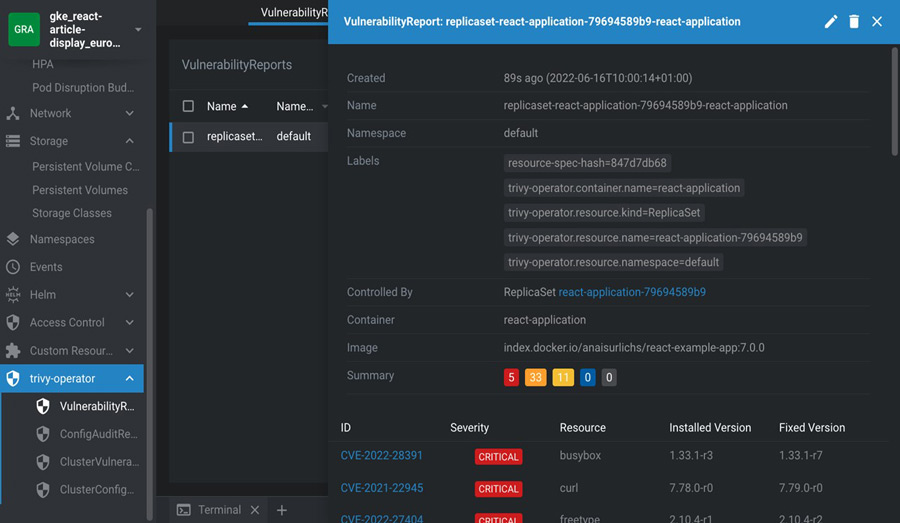
Trivy Operator security scans highlighted in Lens through the extension
But that’s not all. Here are more cool updates
- We’ve improved support for in-cluster secrets scanning.
- Trivy can now scan containers running in containerd
- We have added the “–context=other-cluster-context” flag to Trivy so you can scan a Kubernetes cluster that is part of your kubeconfig but that you’re not directly connected to.
- Trivy can now scan ephemeral containers — containers that have a short lifespan in a Kubernetes cluster and that are used to troubleshoot issues or to support additional processes of containers in the same pod.
Join the Trivy community
We have lots of exciting plans for Trivy. Become part of the journey by joining our Slack community and contributing on GitHub. Also, let us know if you have questions or if there are other features you’d like to see in Trivy.
And when you try the new Trivy features, share it on social media!
