For most of us developers, our container security protocol involves some sort of static image scan for vulnerabilities. Unfortunately, to do this usually involves jumping out of one type of software program, like a code editor, to open a completely separate tool to perform the scanning. Well, the open source team at Aqua recognized the potential advantages of seamlessly merging vulnerability scanning using Trivy (Aqua’s open source scanner) with an Integrated Development Environment (IDE). So, a project to build an extension to support this function was initiated. The project began by selecting a popular IDE that users already know and love for code editing (Visual Studio Code). The result provides users with a very useful and time saving extension.
This blog covers how to install the extension, running it to scan for vulnerabilities and then concludes with some technical highlights from the project.
The Players
Trivy vulnerability scanner is an open source tool that helps you discover vulnerabilities in your container images. With our new extension, now you can use Trivy to find vulnerabilities from within your Visual Studio Code software projects by scanning directories and git-based repositories. This is immensely helpful for those situations where you may need to quickly evaluate your existing projects and repositories for vulnerabilities in downstream dependencies. You can also scan third-party project repos for vulnerability dependencies to help assess whether they meet your needs.
Visual Studio Code, commonly known as VS Code, is a free code editor offered by Microsoft. It’s a popular choice among the open source community, and it offers a great extensions mechanism. In fact, many members of our team use it at Aqua! For these reasons and more, we decided to write an extension for VS Code that runs Trivy over a project from within the editor.
Here’s a five-second GIF demonstrating the Trivy VS Code extension in action.
Installation
If you haven’t already installed Trivy on your system, you’ll need to do so first. On macOS you can install Trivy using brew:
$ brew install aquasecurity/trivy/trivy
On other platforms, you can grab the appropriate version of Trivy along with the necessary instructions from this link: https://github.com/aquasecurity/trivy#installation
Once you have Trivy installed, the next step is to download the Trivy VS Code Extension. It’s available on the Microsoft Marketplace as a free download.
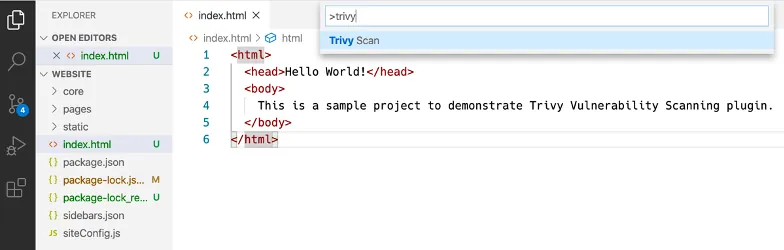
After clicking on the Install button, VS Code will automatically open and install the extension. Once it is installed, you can open an existing project and then open the command pallet by pressing Command+Shift+P on macOS (Control+Shift+P on Windows/Linux). The extension will install a new command as an action called Trivy Scan And that’s it!
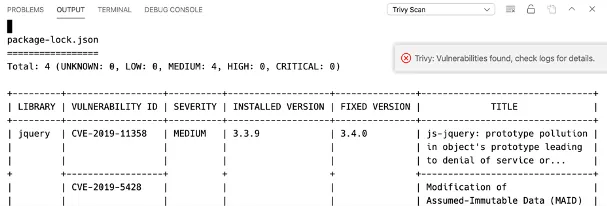
Once you press Enter, Trivy will scan your project and report on any vulnerabilities in the output window.
Technical Details
Microsoft has opened the ecosystem to allow developers to write their extensions in both TypeScript and native JavaScript. Trivy VS Code Extension is written in TypeScript.
The extension delegates all the heavy lifting to the actual Trivy CLI underneath the hood. We decided to go with this approach since it doesn’t require adding any extra business logic to the extension itself. The extension acts as a wrapper to the Trivy CLI by exposing a familiar interface to the user through VS Code.
Try it Out For Yourself
Building an extension that combines the benefits of a robust vulnerability scanner with a popular code editor was a no brainer. We think you’ll enjoy the advanced features found in Trivy even more when they’re baked right in as an extension for VS Code. The ability to scan discreet images or evaluate entire image repositories from inside the VS Code editor is an incredible time-saver, while also providing more image security.
You’re encouraged to take a look at Trivy extension for VS Code on GitHub, as the extension is freely available as open source. We would welcome any new feature ideas you may have, and we look forward to seeing you using Trivy scanning in action!
More from Aqua open source:
