Red Hat OpenShift container platform is one of the popular and mature platforms for developing and managing container deployments. While it has many built-in security features, Aqua provides an additional layer of security both in development as well as for protecting containerized applications in runtime.
Installing Aqua on OpenShift
Aqua can be natively deployed in an openshift environment by deploying pods, services and Daemonsets.
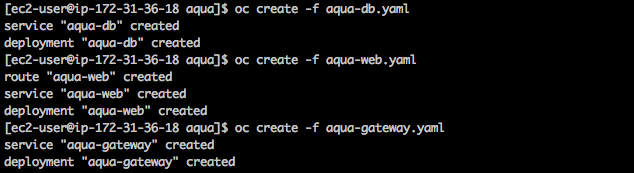
You start by deploying the Aqua Command Center components:
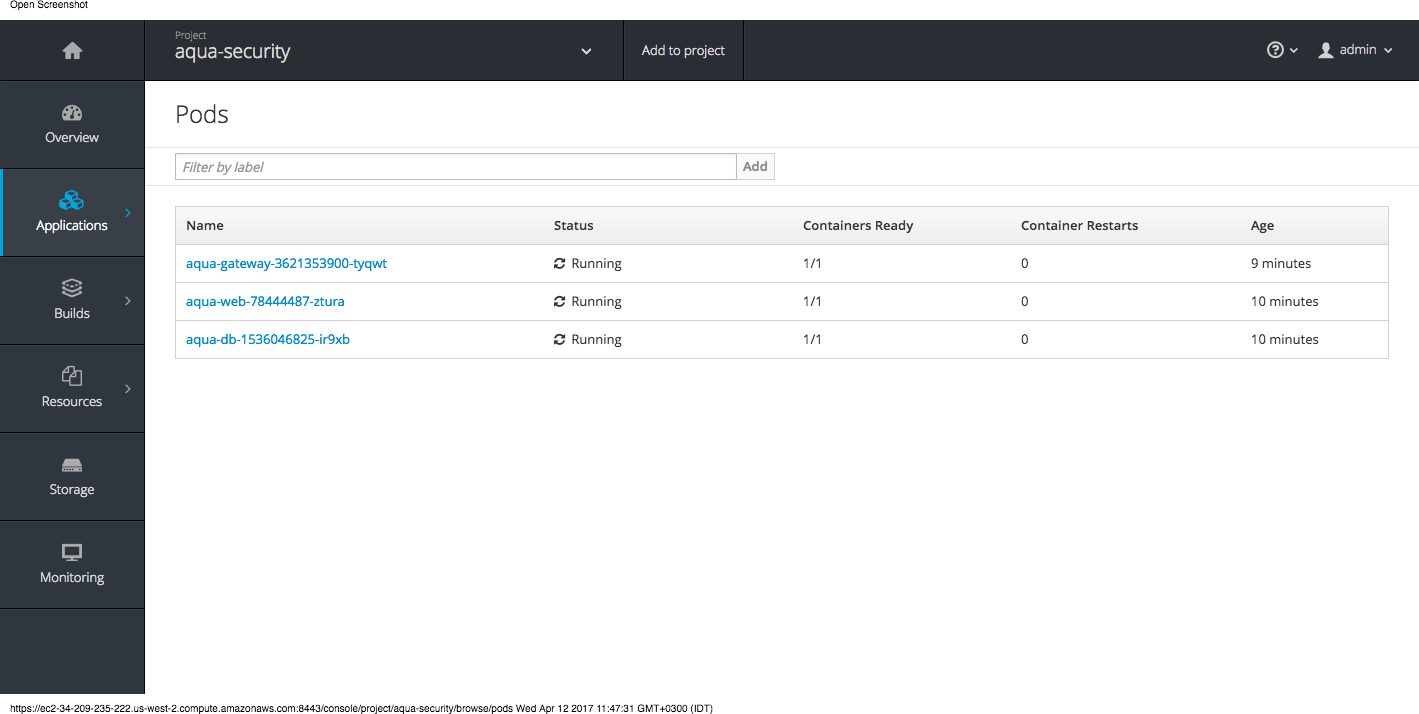
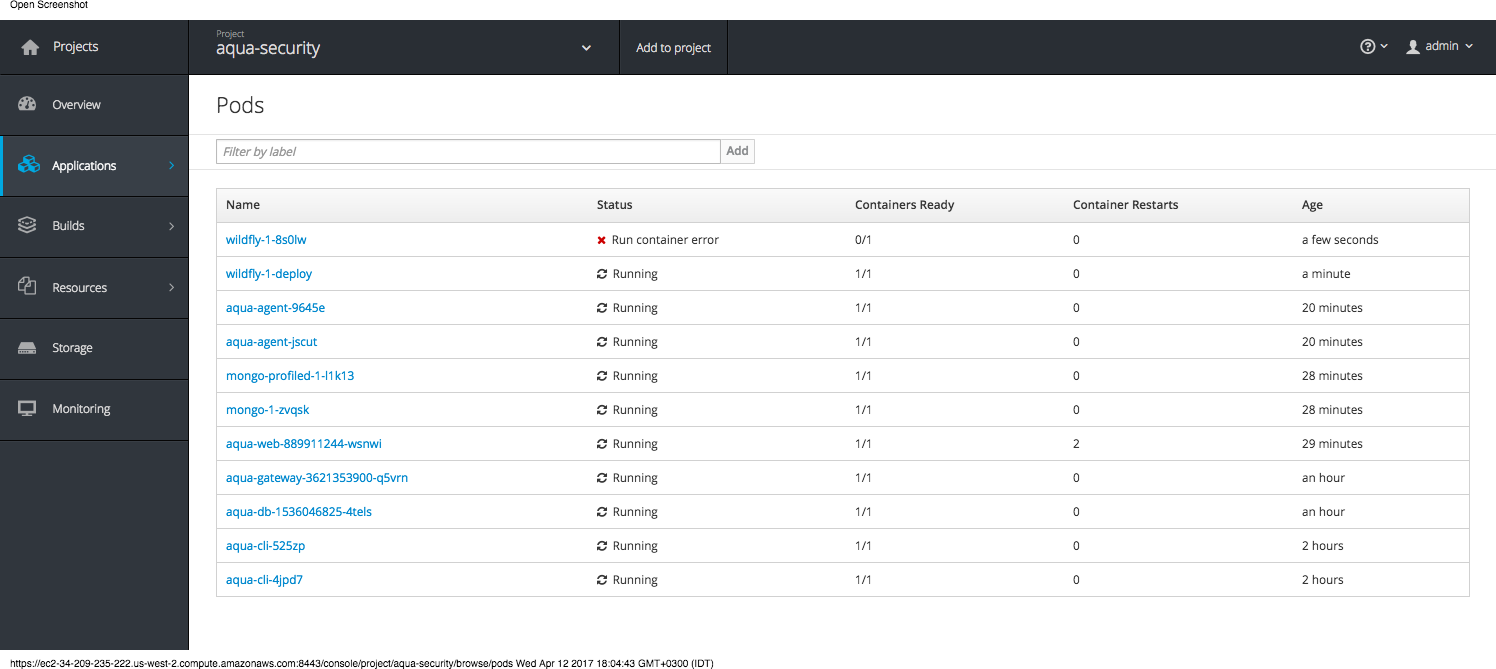
You can then verify that pods are running:
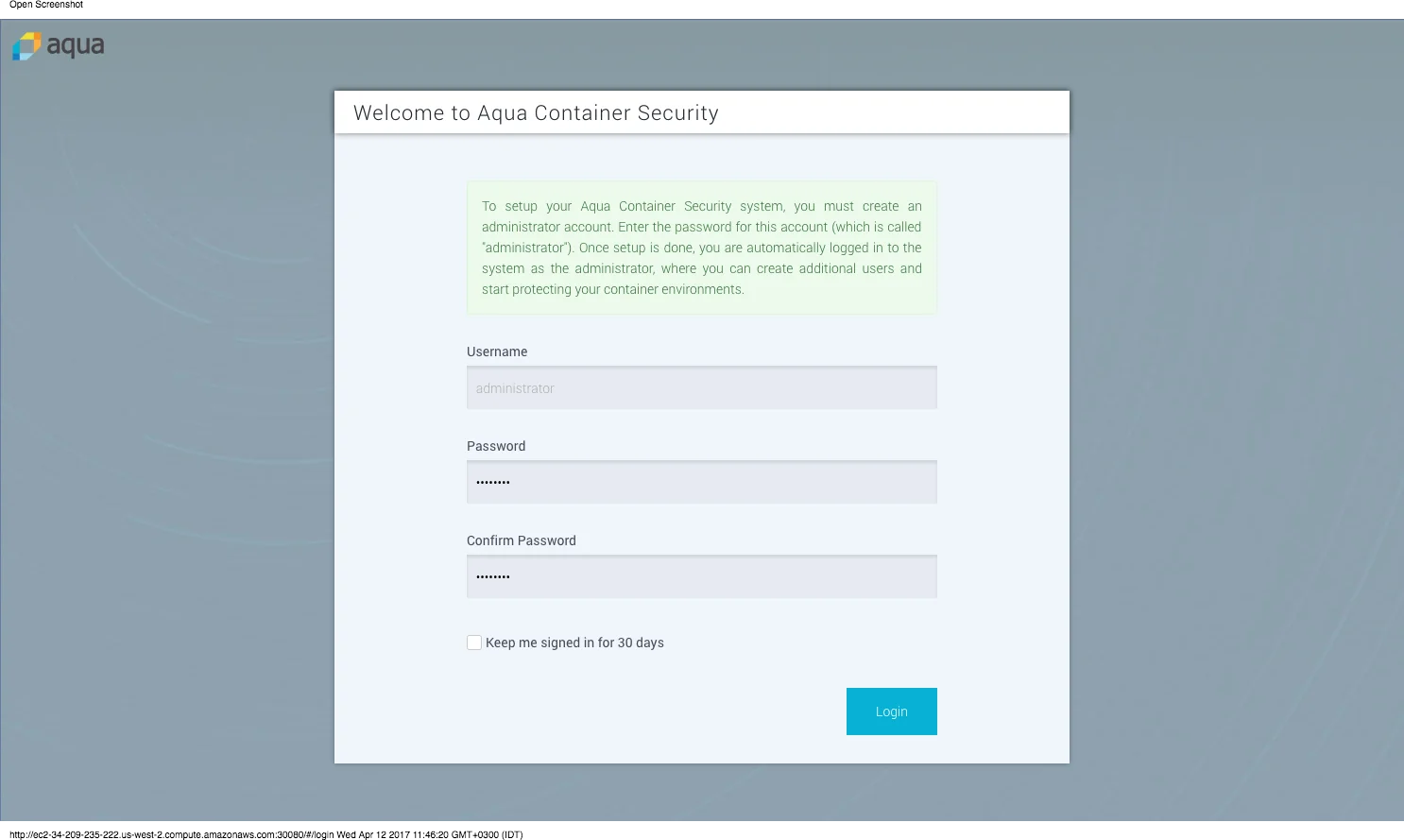
And login to the Aqua Command Center:
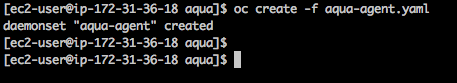
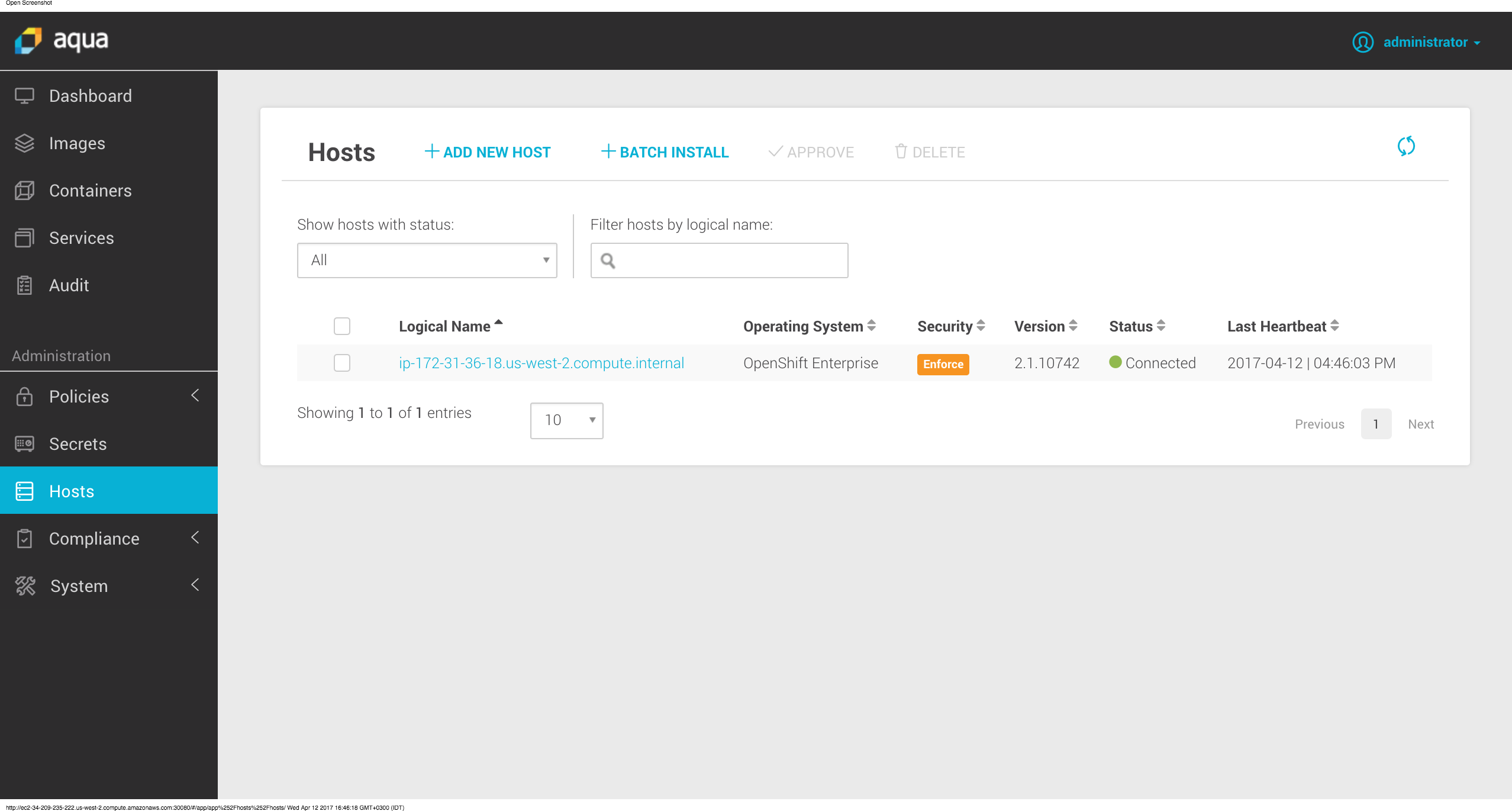
You then deploy the Aqua Enfrocer container through Daemonset – this will ensure that Aqua Enforcer is running on every node in the Openshift cluster:
Container Image Assurance
With Aqua, you can control which images will be allowed run in your Openshift environment by defining image assurance policies. These policies can define the security level that containers running in Openshift environment should have.
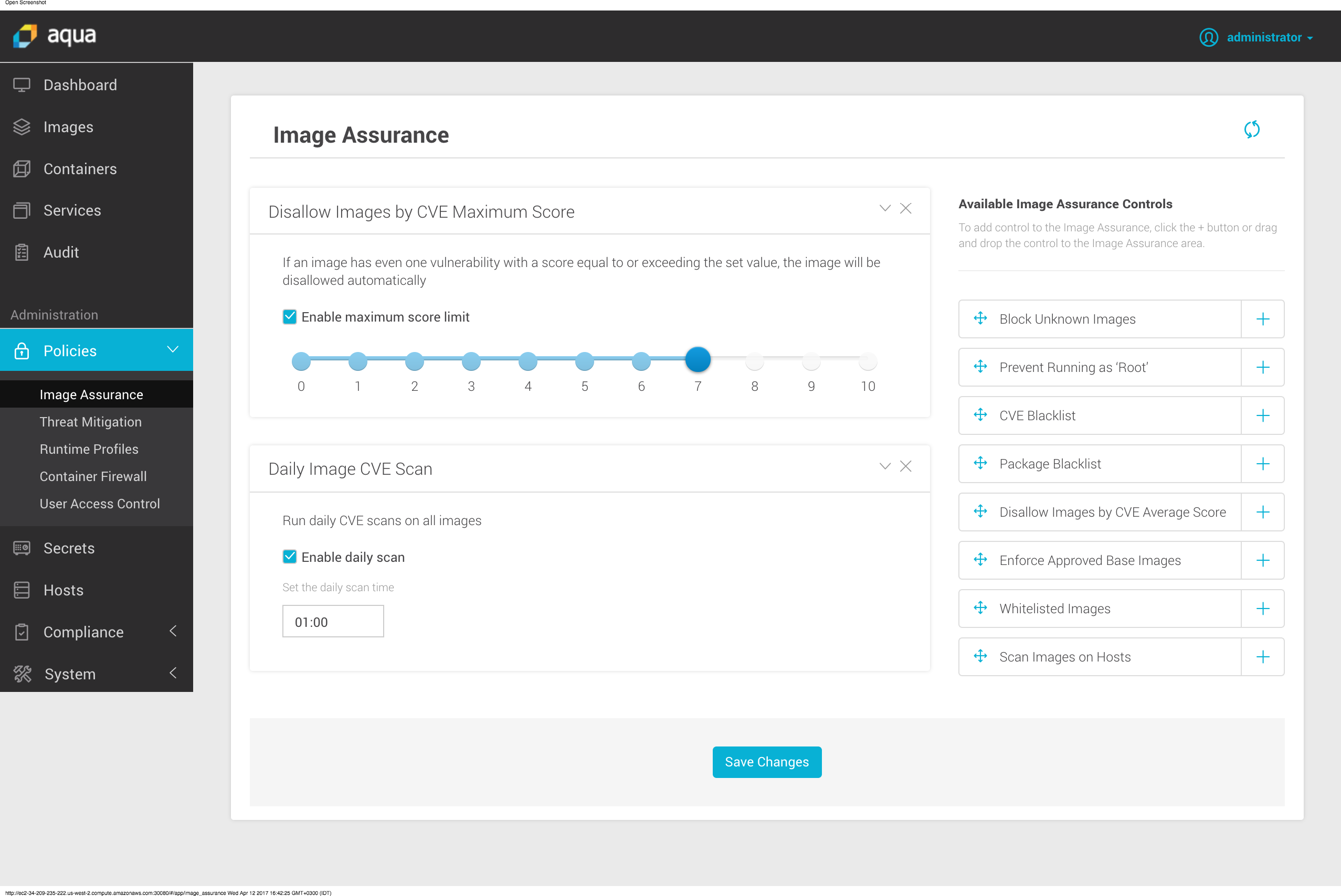
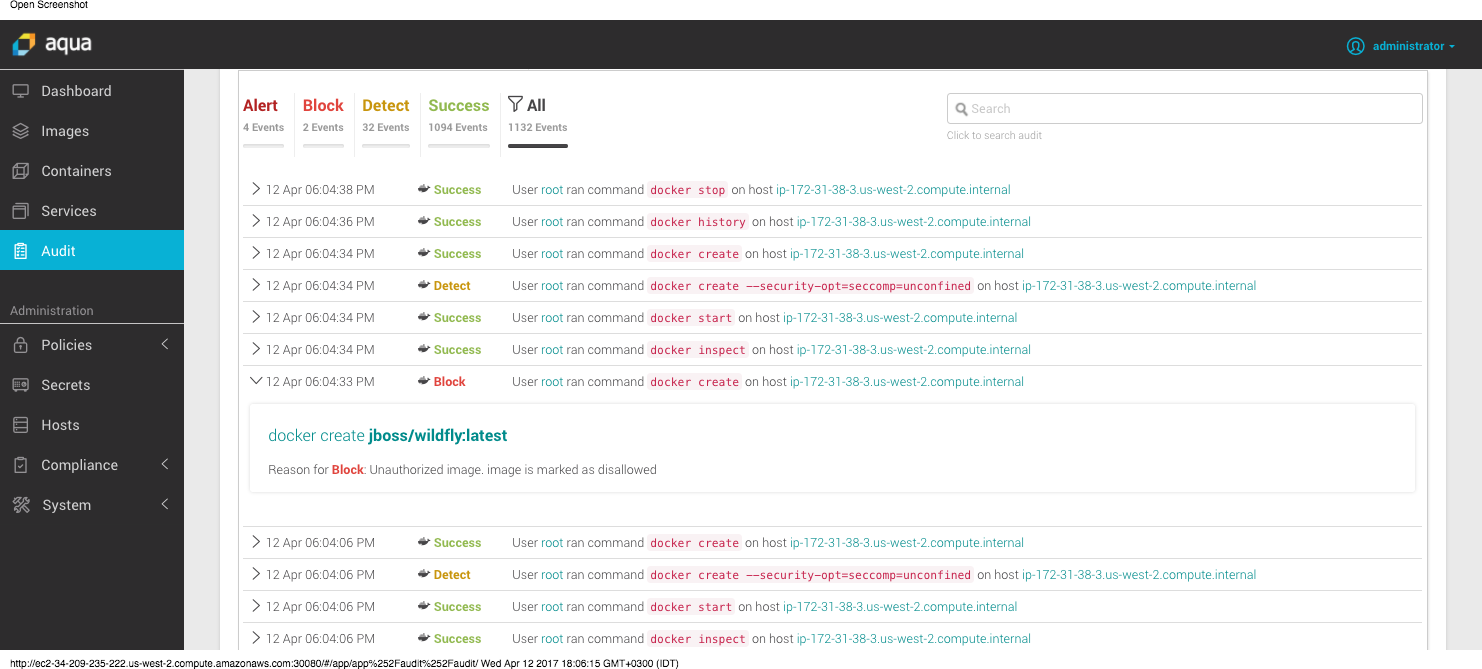
The outcome is that all images in the OpenShift environment will be assessed for security quality, which includes scanning them for known vulnerabilities, insecure configurations, and embedded secrets. If an image does not pass the security assessment then it will be marked as “disallowed” for running, and will not be able to run on the cluster.
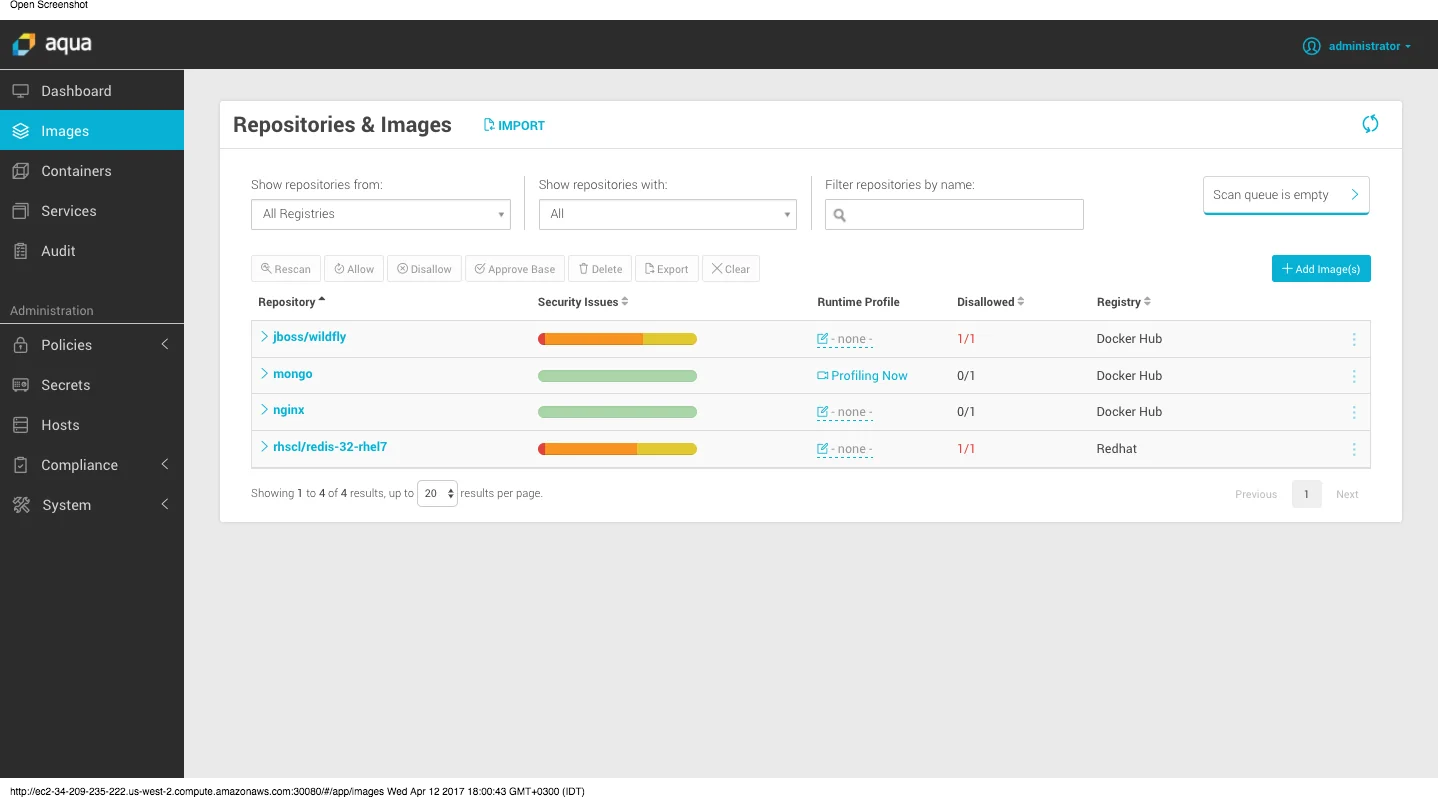
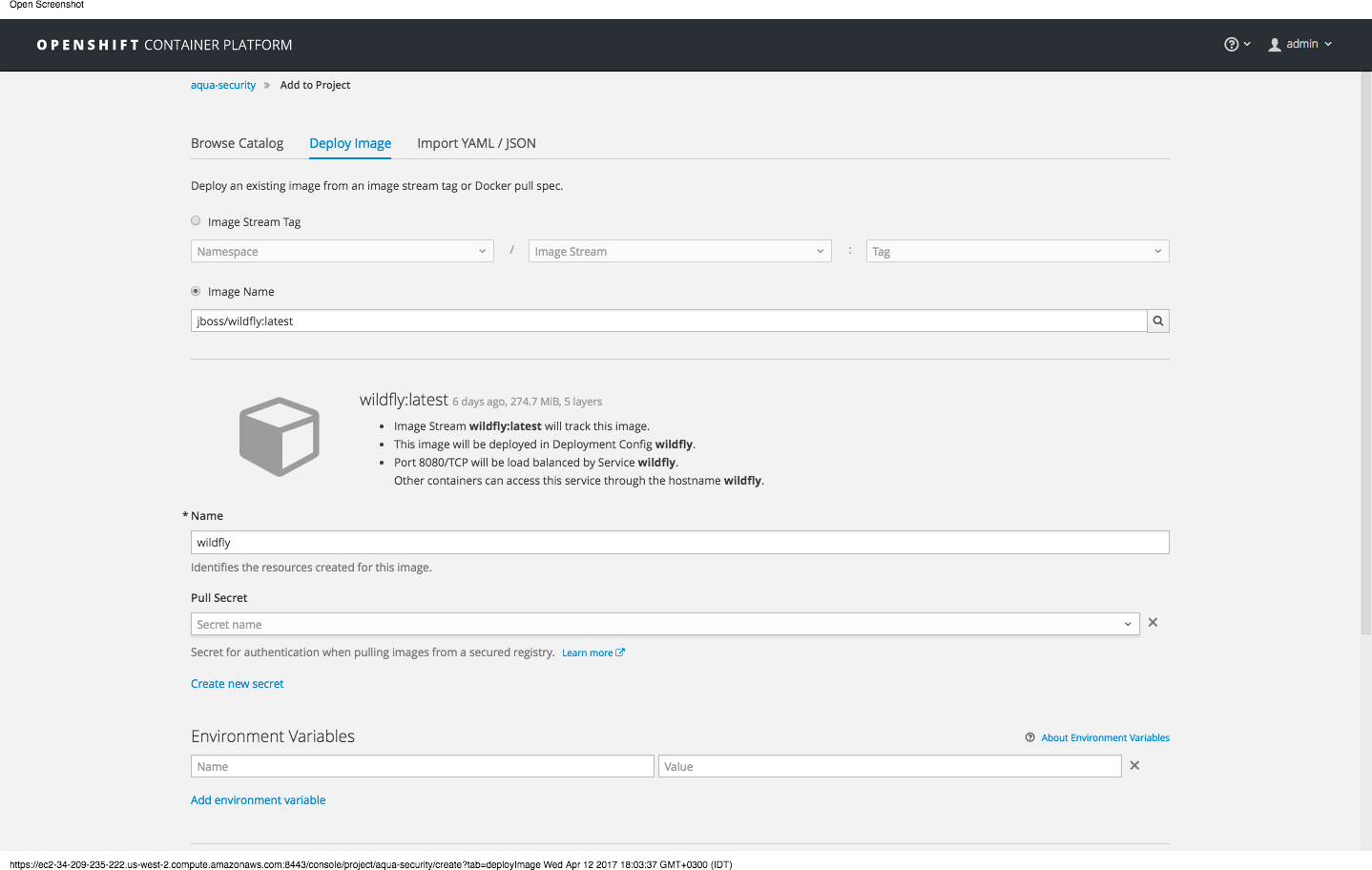
For example, trying to run jboss/wildfly image on the OpenShift cluster will fail as the image vulnerability score is too high.
Runtime Controls
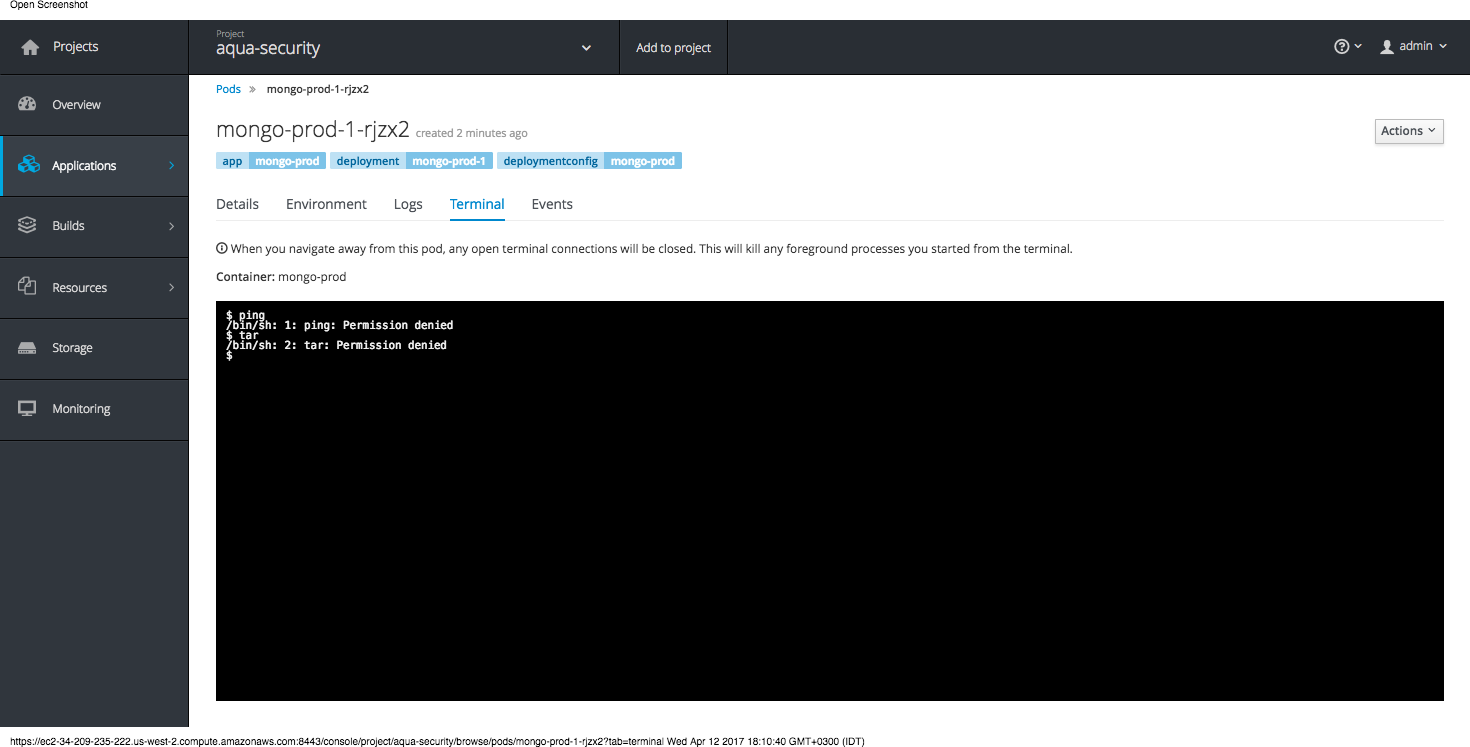
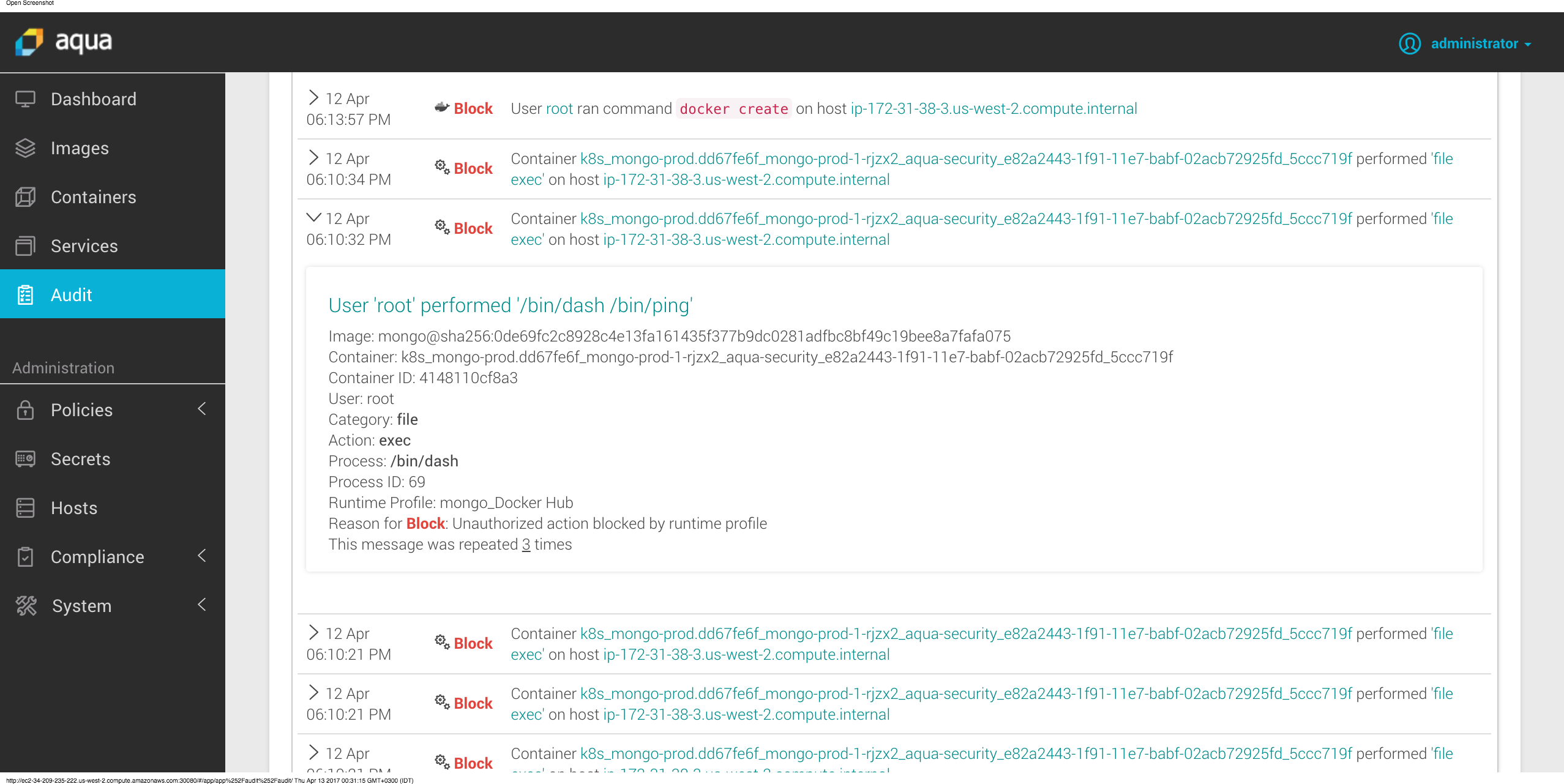
Aqua automatically profiles containers running in an Openshift cluster to limit their abilities to the least needed privileges, based on actual application use. This means that if a container will try elevating privileges through user impersonation, running an unauthorized process or accessing an unauthorized file – the operation that violates the policy would be blocked and reported:
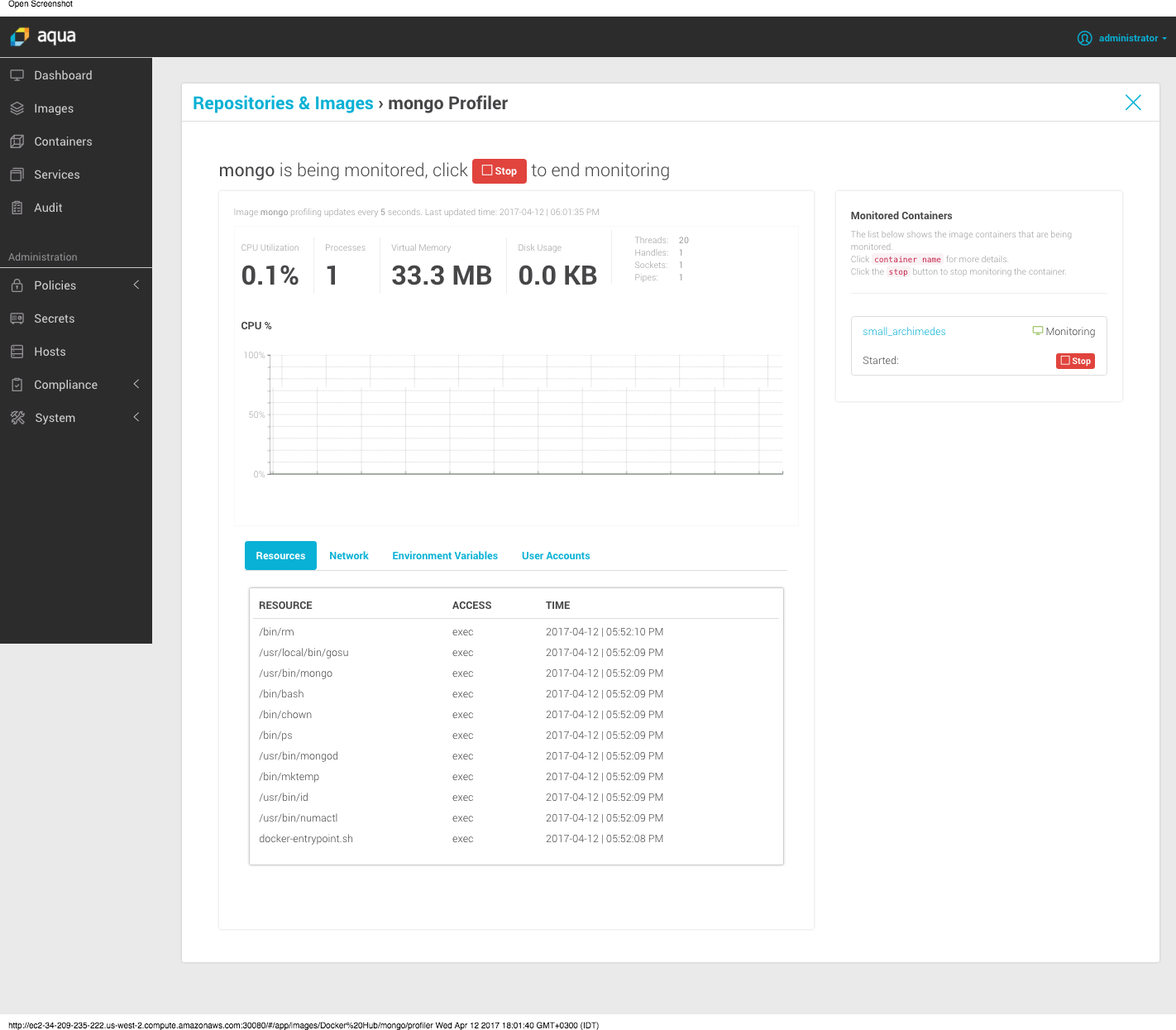
As you can see, if the container tries to run a process that was not allowed under the profile, that actions will be blocked and the event will be logged.
To Learn More
Access our resource center, the Aqua page on OpenShift Hub
