The Payment Card Industry Data Security Standard (PCI DSS) is a well-known compliance framework for any organization handling payment card data. However, translating the PCI DSS requirements into the world of containers and Kubernetes can be overwhelming. In this post, we break down how containerized applications impact PCI DSS compliance and how to meet its requirements in a cloud native environment.
What is the PCI DSS?
Introduced in 2004, the PCI DSS is an information security standard for organizations that process, store, or transmit credit card data from major credit providers. It was created with the combined effort of five principal credit card organizations to increase control around cardholder personal data and thus reduce data theft and fraud.
The PCI DSS specifies 12 requirements for compliance that are organized into six broader goals:
1. Build and maintain a secure network
- Install and maintain a firewall configuration to protect cardholder data
- Do not use vendor-supplied defaults for system passwords and other security parameters
2. Protect cardholder data
- Protect stored cardholder data.
- Encrypt transmission of cardholder data over open, public networks
3. Maintain a vulnerability management program
- Protect all systems against malware and regularly update anti-virus software or programs
- Develop and maintain secure systems and applications
4. Implement strong access control measures
- Restrict access to cardholder data by business need to know
- Identify and authenticate access to system components
- Restrict physical access to cardholder data
5. Regularly monitor and test networks
- Track and monitor all access to network resources and cardholder data
- Regularly test security systems and processes
6. Maintain an information security policy
- Maintain a policy that addresses information security for all personnel
For any organization to process, store or transmit any cardholder data, the PCI DSS requirements must be complied with. If you choose to use information provided by VISA or MasterCard, then you also need to be formally validated. In the event of a security breach, if you were not PCI DSS compliant at the time of breach, you will be subject to additional penalties.
An in-depth explanation of each of the PCI DSS requirements is provided in our guide Supporting PCI DSS Compliance for Cloud Native Environments.
The challenge of meeting the PCI DSS requirements in the cloud
So, while the PCI DSS itself is nothing new, the rapid speed of cloud native development means that effectively addressing the requirements in a cloud native environment is not an easy task.
Cloud native environments are characterized by elastic infrastructure and highly dynamic and ephemeral workloads deployed across multiple environments, with no permanence of location or traditional network segmentation. Additionally, the distributed-layer architectures of cloud environments add complexity and require a change in how access, privileges, and networking are governed, monitored, and audited.
Thus, understanding and meeting PCI compliance for cloud native applications can pose a significant challenge. Traditional security tools lack the ability to track changes and provide context in such environments and will not ensure compliance as they have done in traditional environments.
Key areas where cloud native environments impact PCI compliance include network security, vulnerability management, user access control and segregation of duties, threat analysis and mitigation, and data protection, real-time visibility, and event audit trails.
How Aqua helps address PCI DSS compliance
Aqua can help address many PCI DSS requirements for applications that span public cloud services, VMs, containers, and serverless functions. Aqua achieves this through the following:
- Cloud account compliance overview
Aqua CSPM offers compliance reports to match your cloud infrastructure scan results to industry standards and compliance controls
- Vulnerability assessment
Aqua provides in-depth vulnerability assessment for container images, preventing vulnerabilities from getting into applications before deployment.
- Policy-based security
Aqua provides out-of-the-box assurance and enforcement policies that you can configure across the build, workload, and infrastructure.
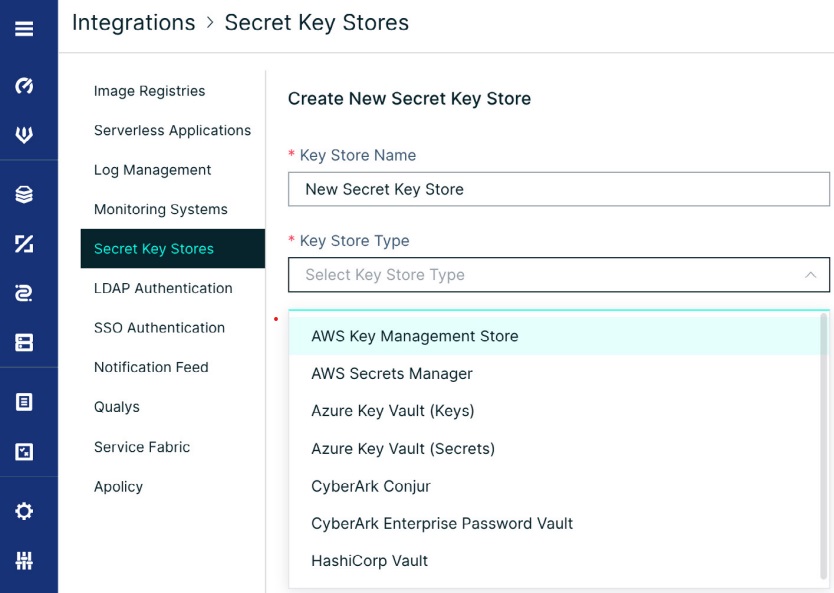
- Secrets management
Aqua provides central management and secure distribution of secrets and cryptographic keys into running containers
- Separation of duties and access control
Aqua’s multi-tenant, role-based access control (RBAC) capability supports the segregation of duties between different applications to limit access by assignments.
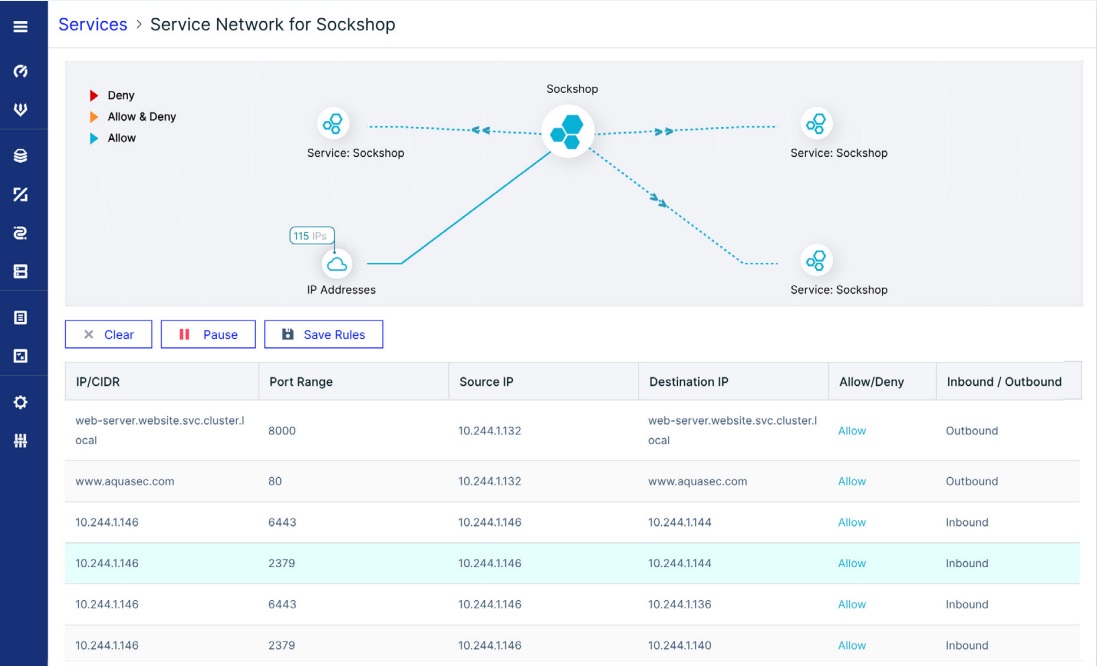
- Identity-based segmentation
Aqua provides a network firewall that prevents unauthorized network connections and nano-segmentation of the network to observe the relationship between workloads to monitor and secure all network connections.
- Full event logging
Aqua provides a granular audit trail of several kinds of events: both regular and those indicating security exposures. - Real-time visibility with detection and response
Aqua provides comprehensive visibility across the entire cloud native lifecycle from build, to infrastructure, to runtime. Our eBPF based visibility engine sits at the kernel level and captures data from your entire cloud native environment.To detect unknown attacks at runtime, Aqua constantly updates a database of behavioral indicators based on intel from Team Nautilus, Aqua’s research team gathered by analyzing real-world attacks in cloud native environments. - Anti-malware in build and runtime
Aqua provides anti-malware in the build and runtime stage to protect against known malware, and our cloud native detection and response capabilities protect against any unknown malware.
Conclusion
It can be challenging to address concerns unique to cloud native applications in PCI-regulated environments. But with the right solutions in place, PCI compliance doesn’t have to be a major hurdle. For a detailed breakdown of how Aqua can help address each of the PCI DSS requirements, download our compliance guide Achieving PCI-DSS Compliance for Containers.
