Aqua Trivy: Vulnerability and Misconfiguration Scanning
Shift left using Aqua Trivy, the fastest way for DevOps and security teams to get started with vulnerability and infrastructure as code (IaC) scanning.
Start NowQuickly add vulnerability and IaC scanning capabilities
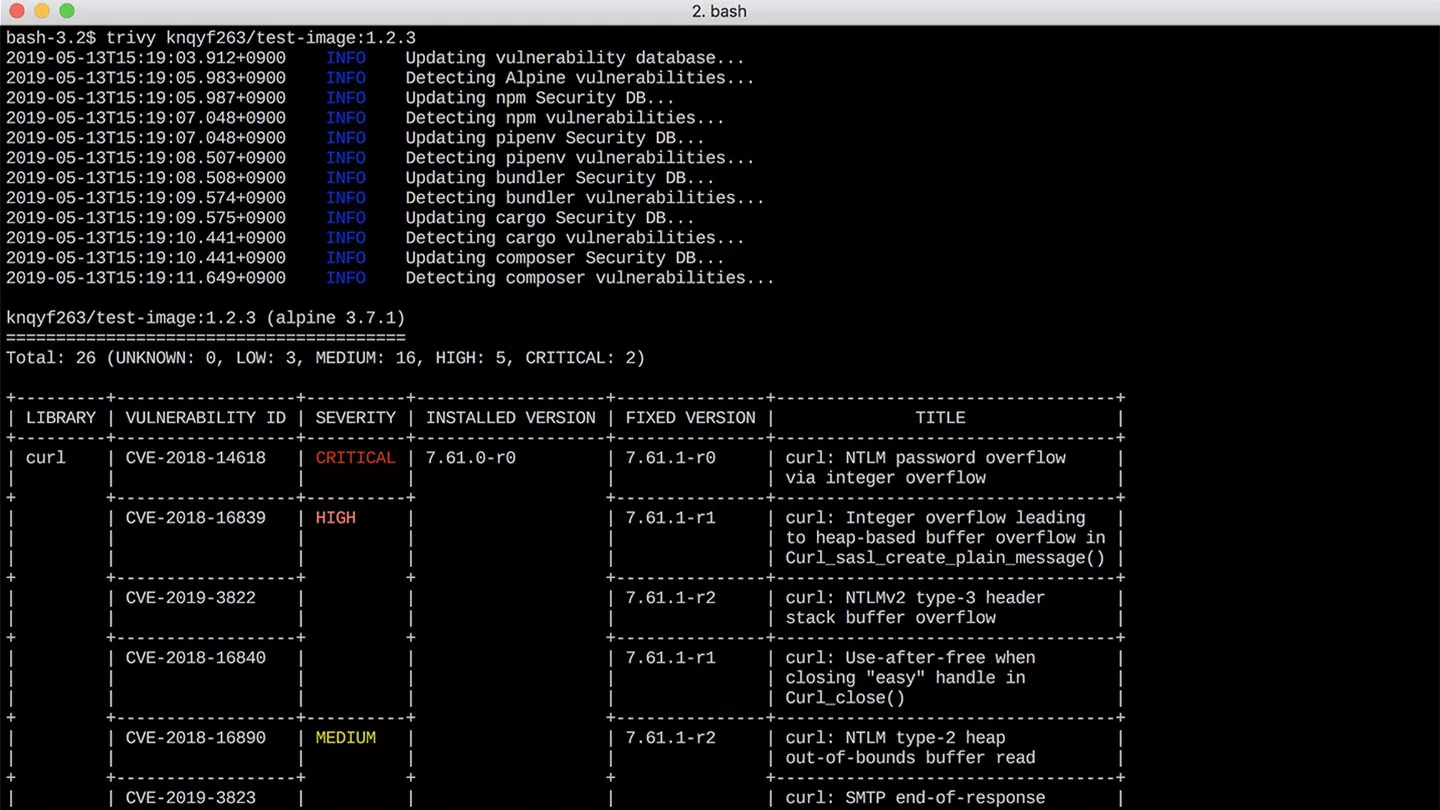
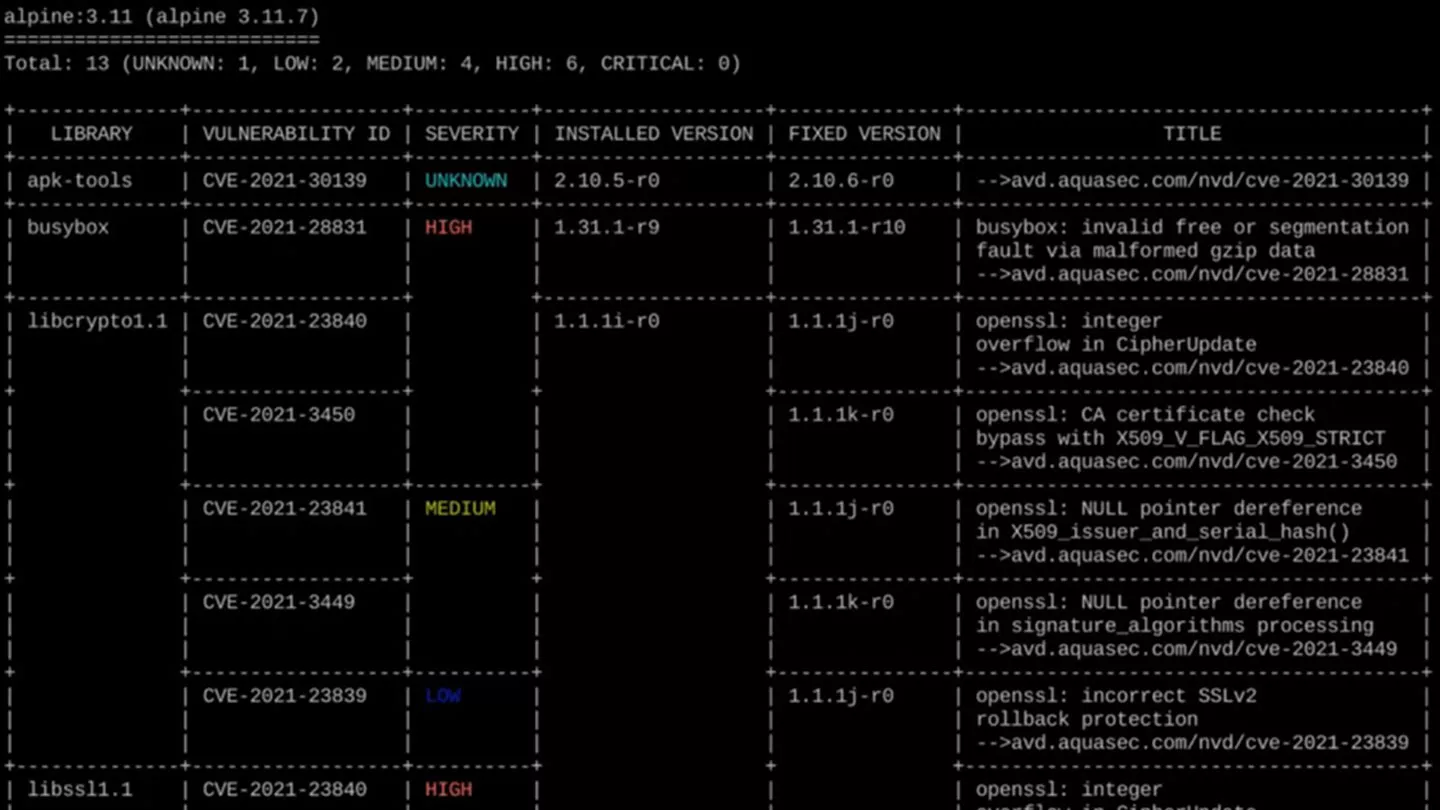
Deployment and integration into the CI/CD pipeline is as simple as installing the binary and specifying a target. Aqua Trivy has a compact database, with auto-update capabilities that do not require middleware or database dependencies. Scanning takes seconds, and critical CVEs can be filtered directly in the command line.
Ecosystem compatibility
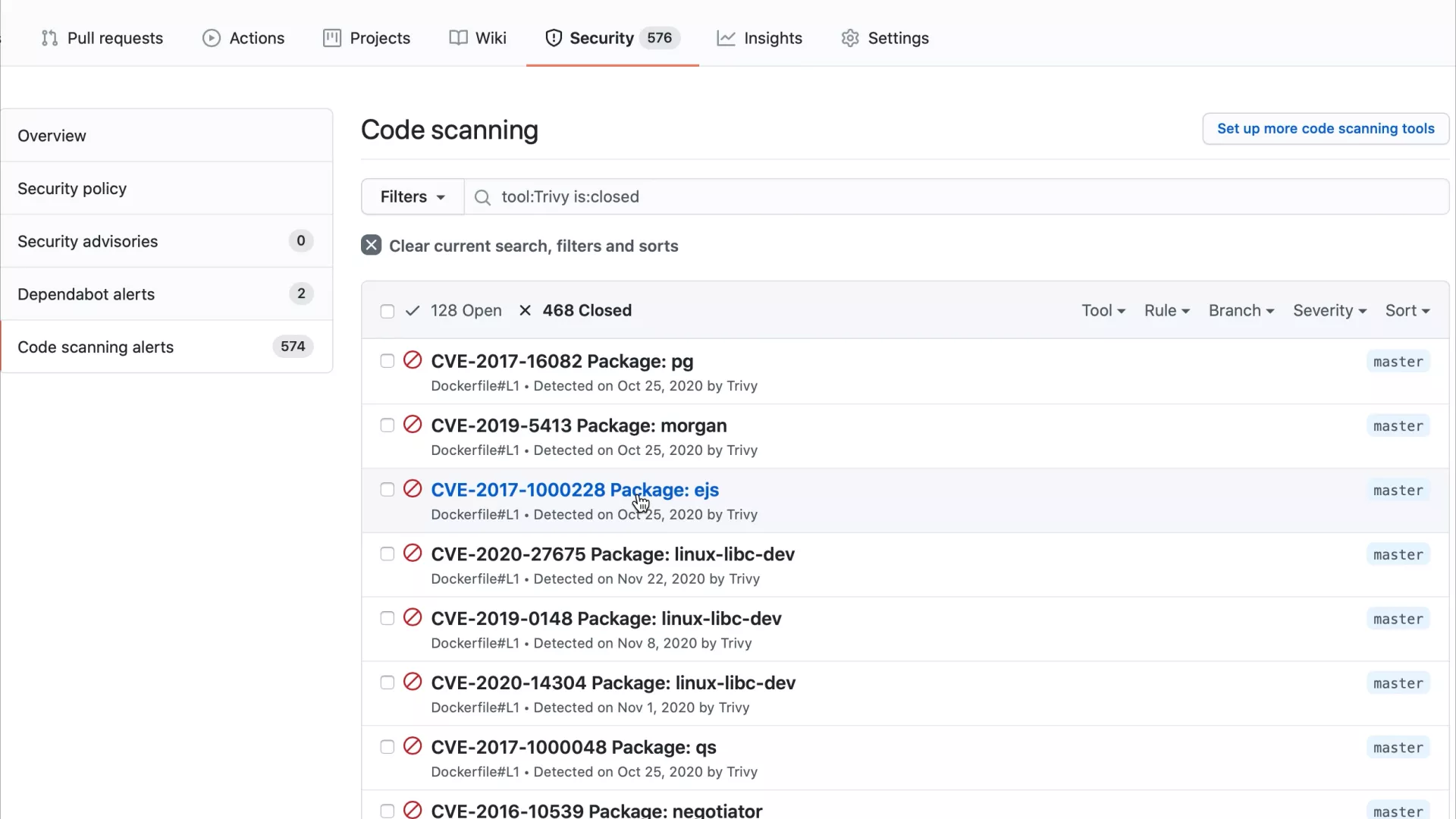
View results directly in the GitHub UI via the GitHub Action or in your favorite Kubernetes dashboard using Aqua Starboard. Export results to external user interfaces in various formats, such as JUnit XML, SARIF, and AWS Security Finding Format (ASFF). Use a Helm chart to install Aqua Trivy into a Kubernetes cluster, or scan images in Harbor with the plug-in adapter.
Broad & accurate coverage
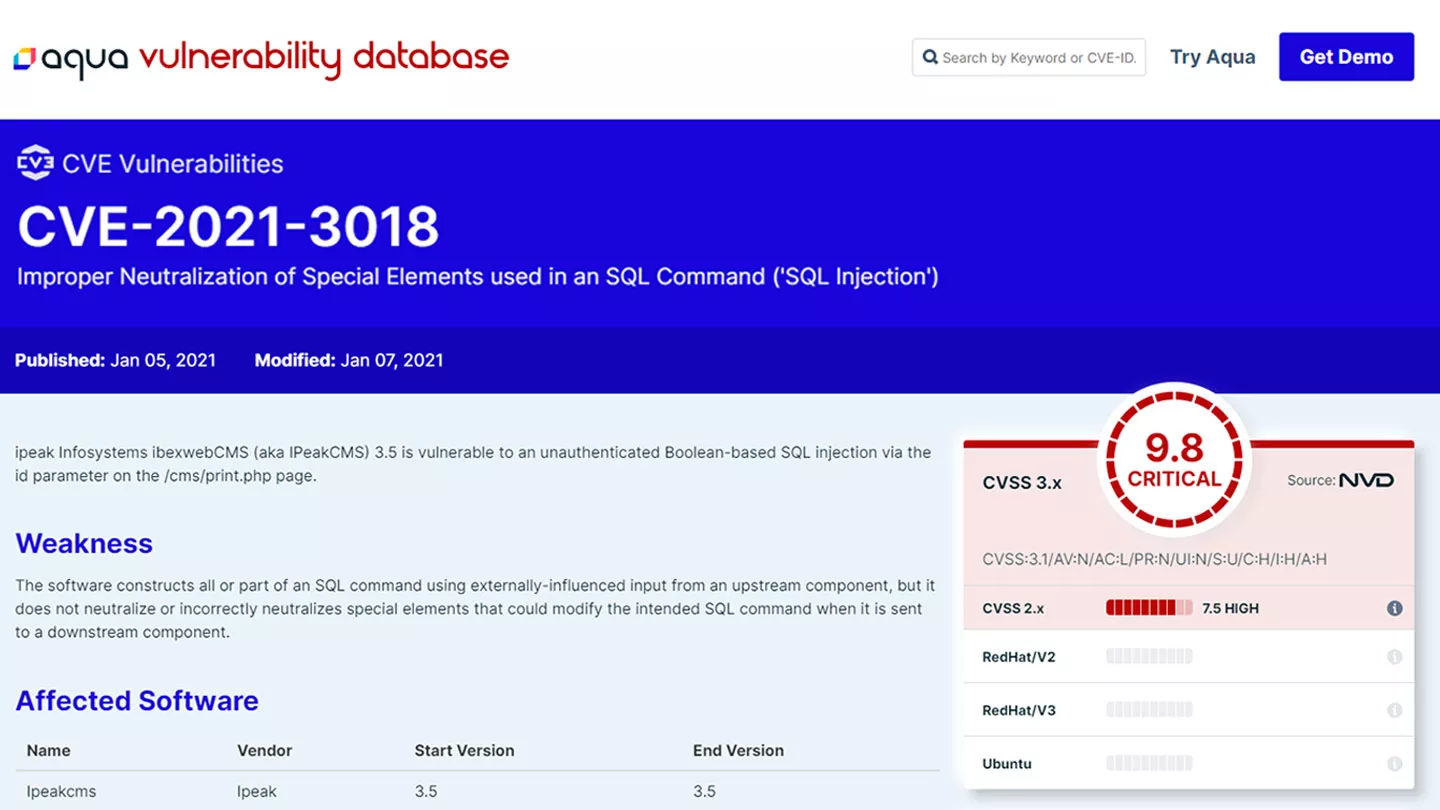
Gain comprehensive visibility across operating system packages and programming language packages, with detailed vulnerability information available at the Aqua Vulnerability Database. See results for fixed and unfixed vulnerabilities, and achieve low false positives for historically difficult operating systems such as Alpine Linux and RHEL/CentOS.
Environment versatility
Scan for private and public registries, local filesystems, and container formats such as tar archives, Podman and Git repositories. Achieve functionality for a variety of execution environments, such as Linux, macOS, FreeBSD, and OpenBSD, with the option to support air-gapped environments as well as distroless images.
Open source scanner