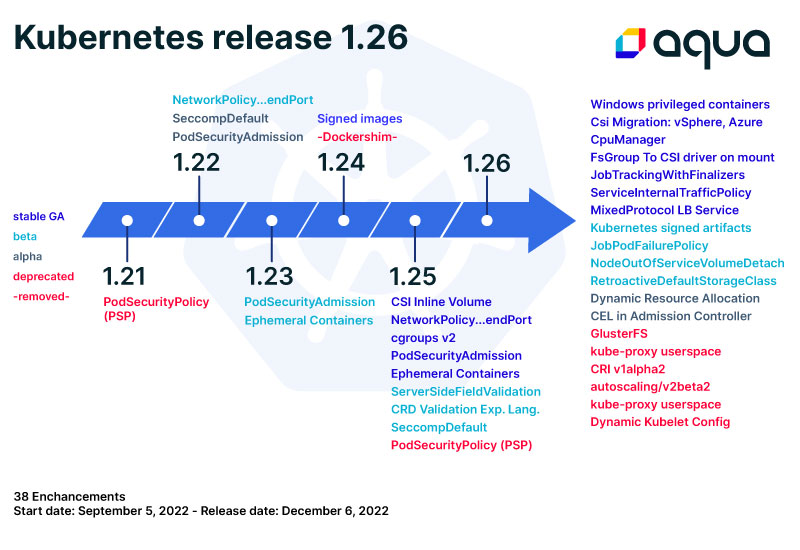
Kubernetes Version 1.26 was released with 37 new enhancements including 11 Stable, 10 Beta, 16 Alpha, and 12 features deprecated or removed. In this blog, we will highlight its most notable features and show how using Trivy will help you find deprecated Kubernetes resources.
registry.k8s.io, Generally Available
The container image registry has changed from k8s.gcr.io to registry.k8s.io to reduce costs and improve availability using multiple Cloud Providers and Regions. You can read more details at the Kubernetes Blog.
Support for Windows Privileged Containers, Generally Available
WindowsHostProcessContainers support containers’ ability to run as one of the supported Windows service accounts. Support for this feature in Windows nodes will now graduate to stable and will be enabled by default. Windows privileged container supports hostProcess and networking. See KEP-1981.
LoadBalancer Validation, Generally Available
The MixedProtocolLBService feature, load balancers with mixed protocol types, enables the creation of a LoadBalancer Service that has different port definitions with different protocols. See KEP-1435.
Service Internal Traffic Policy, Generally Available
Also introduced is a new field spec.internalTrafficPolicy in service that will allow clusterIP routing to be node local. The new internalTrafficPolicy field has two options: Cluster (default) and Local. Before 1.26, Kubernetes services randomly distributed incoming requests to all endpoints in the whole cluster. If the request did not find the endpoint in a node, it would keep bouncing around until it hit the endpoint on another node. With this release, Kubernetes services will use the node-local mechanism to route incoming requests only to an endpoint within same node if it exists or, otherwise, drop the request. This is done through the introduction of the new spec internalTrafficPolicy. See KEP-2086.
Pod FSGroup to CSI Driver on Mount, Generally Available
The DelegateFSGroupToCSIDriver feature allows Kubernetes to supply the pod’s fsGroup to the CSI driver during attach or mount time of the volumes, avoiding the Kubelet from changing the permissions of volumes. See KEP-2317.
Kubernetes Signing Artifacts, in Beta
The Kubernetes release process signs all binary artifacts (tarballs, SPDX files, standalone binaries) by using cosign’s keyless signing. With this step, the release process improves security related to the software supply chain. See KEP-3031.
Dynamic Resource Allocation, in Alpha
The DynamicResourceAllocation feature allows for request and share resources between pods and containers inside a pod. It is a generalization of the persistent volumes API for generic resources. Third-party resource drivers are responsible for tracking and allocating resources. See KEP-3063.
Common Expression Language (CEL) in Admission Controllers, in Alpha
The ValidatingAdmissionPolicy feature implements the CEL validation for incoming requests using the Common Expression Language to declare validation rules of a policy. Admission webhooks can be burdensome and complex to develop. This enhancement avoids much of the complexity of admissionwebhooks by embedding CEL expressions into Kubernetes resources instead of calling out to a remote webhook binary. See KEP-3488.
Pod stats from CRI, in Alpha
The feature PodAndContainerStatsFromCRI configure the kubelet to gather container and pod stats from the CRI container runtime rather than gathering them from cAdvisor. The metrics are related to the node, volume, pod, and container level by the kubelet. See KEP-2371.
Health SLI metrics, in Alpha
The ComponentSLIs feature improves the ability to consume Service Level Indicator (SLI) metrics for each Kubernetes component binary. This metric endpoint is exposed on the serving HTTPS port of each component at the path /metrics/slis. With SLI metrics enabled, each Kubernetes component exposes two metrics, a gauge and a counter. See KEP-3466.
Container Runtime Interface (CRI) v1alpha2, Now Removed
In the previous version 1.25, runtime.v1alpha2.RuntimeService was deprecated and in this release this feature has been removed. This affects the kubelet and the container runtime that were needed to support the CRI v1. Containerd 1.5 will be EOL on January 28, 2023, since it is not supported by Kubernetes 1.26. User would need to upgrade to Containerd 1.6 before upgrading to 1.26. See CRI v1alpha2, sig/node, PR.
Kube-Proxy from the User Space, Now Removed
The kube-proxy in the user space has been removed from the Kubernetes core. The sig/network has been tracking this removal since the deprecation of the flag options for the kube-proxy mode in the 1.23 release. In this release, it is no longer supported on either Linux or Windows. Users should now use iptables or ipvs on Linux or kernelspace on Windows. See kube-proxy userspace, sig/network, PR.
Check for Deprecated Kubernetes Resources with Trivy
Trivy helps you to find vulnerabilities, misconfigurations, secrets, SBOMs in containers, Kubernetes, code repositories, clouds, and more. By using Trivy for misconfigurations in your manifests or Trivy Operator for your cluster, you will get information related to deprecated Kubernetes resources.
Release Features 1.26
37 Enhancements, Start date: Mon 5th Sep 2022, Release date: Thurs 8th Dec 2022
Stable, GA
- registry.k8s.io blog: registry.k8s.io: Faster, Cheaper and Generally Available (GA)
- Windows privileged containers, sig/windows, KEP-1981
- LoadBalancer validation, MixedProtocolLBService, sig/network, KEP-1435
- CSI Migration: cSphere, Azure, sig/storage
- CPUManager, sig/node, KEP-3570
- fsGroup To CSI driver on mount, sig/storage, KEP-2317
- JobTrackingWithFinalizers, KEP-2307
- ServiceInternalTrafficPolicy, sig/network, KEP-2086
Beta
- Kubernetes signed artifacts, sig/release, KEP-3031
- JobPodFailurePolicy KEP-3329
- NodeOutOfServiceVolumeDetach, Non-graceful node shutdown, sig/node, KEP-2268
- RetroactiveDefaultStorageClass, sig/storage, KEP-3333
Alpha
- Health SLI (Service Level Indicators) metrics, sig/instrumentation, KEP-3466
- Pod Stats from CRI, cAdvisor-less, CRI-full Container, sig/node, KEP-2371
- Dynamic Resource Allocation, sig/node, KEP-3063
- CEL in Admission Controller, sig/api-machinery, KEP-3488
- Provision Volumes from data source E.g. snapshots, sig/storage, KEP-3294
