If you’re running workloads on Kubernetes, one of the toughest things to understand is where you have security gaps. Yes, there are CIS benchmarks and configurations to tweak, but they are generalized and won’t highlight the risks in workloads that are actually running in your clusters. The Aqua Risk Explorer’s dynamic display of workloads and risk assessment scoring provides this information instantly to help DevSecOps teams identify the most vulnerable deployments and nodes, and prioritize security remediation based on risk.
When securing large production environments, DevSecOps teams will often face a seemingly endless stream of information concerning security risks – vulnerabilities, malware, sensitive data, misconfigured privileges, suspicious network connections and more. This torrent of information can easily overwhelm even those who are familiar with Kubernetes and container-based applications.
Aqua Risk Explorer was created to provide visualization and easy prioritization of risks in Kubernetes-based environments, taking into account that those risks might stem from multiple sources, vulnerabilities, and threats.
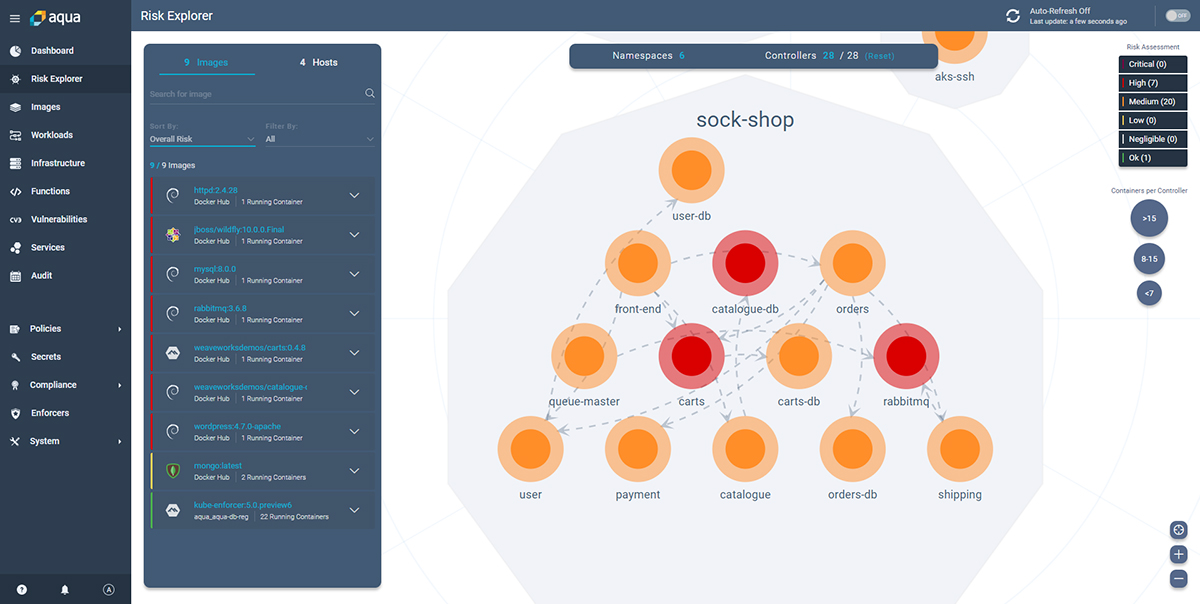
As soon as you deploy Aqua in a Kubernetes environment, it will discover and display your running K8s workloads, and immediately provide an assessment of your clusters.
A Dynamic Map of Risk in Kubernetes Clusters
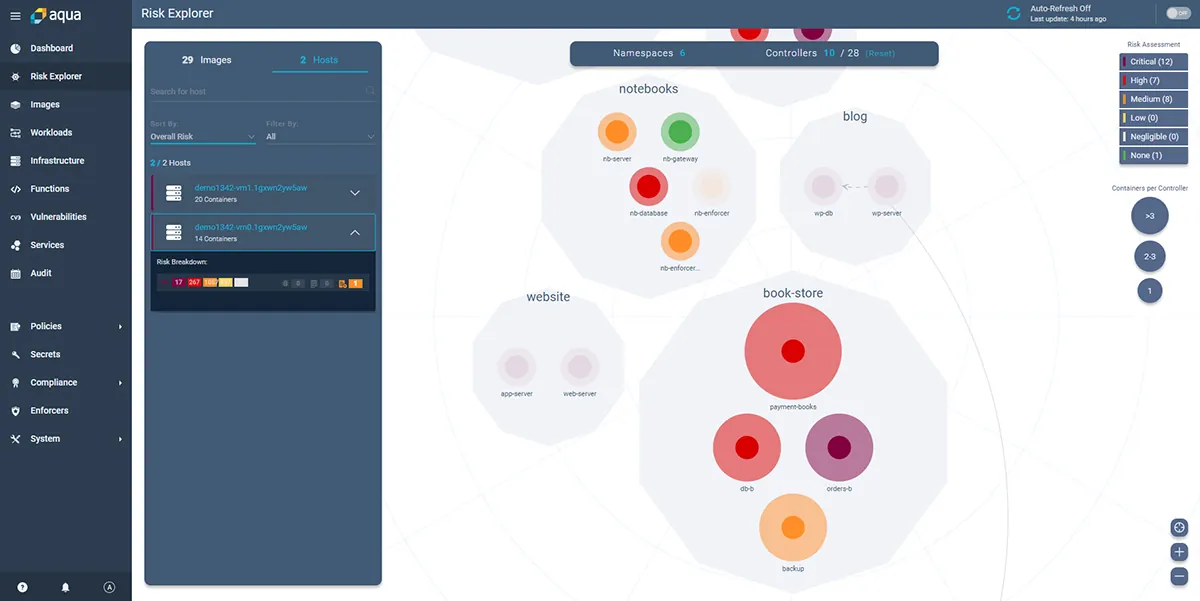
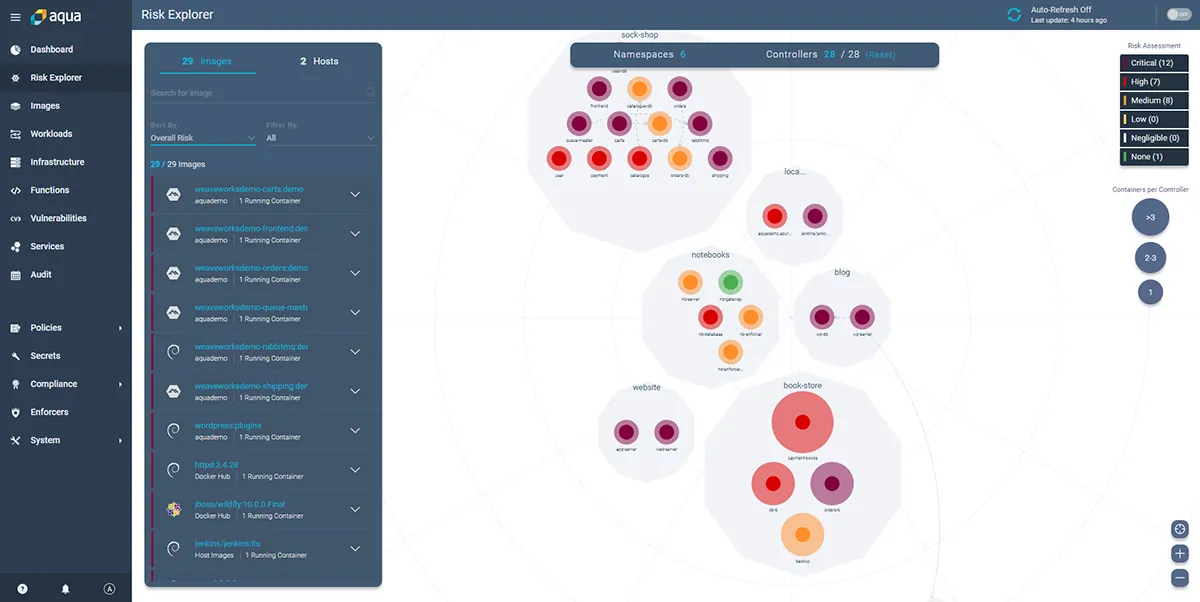
Aqua Risk Explorer is a dynamic map of Kubernetes clusters that are actively running in an environment, along with their associated security risk scores. It displays namespaces, deployments, nodes (hosts), containers and the images they came from, as well as network connections between and within namespaces, and their calculated risk scores. This is a logical and not a physical view of the elements of a Kubernetes cluster – so any given object might in reality be replicated multiple times. The reason for this is that visualizing a physical cluster would make it very difficult to understand what’s happening in large clusters, and most of the risk factors would be identical in replicated nodes/pods anyway.
How is The Risk Level Calculated?
Kubernetes Deployments are categorized based on their risk assessment scores, from low risk to critical. You can filter the highlighted object by severity to only focus on a specific risk level.
For each deployment, the Risk Explorer displays the images used to run the containers and their associated risks. Drilling down further, the actual running containers and their risk scores are displayed.
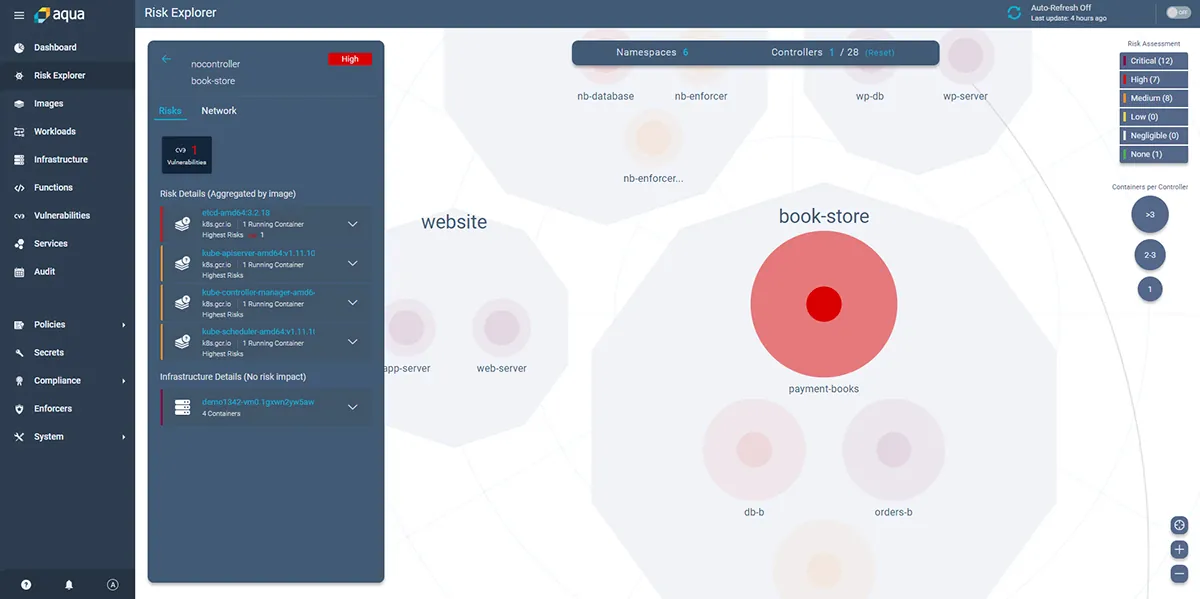
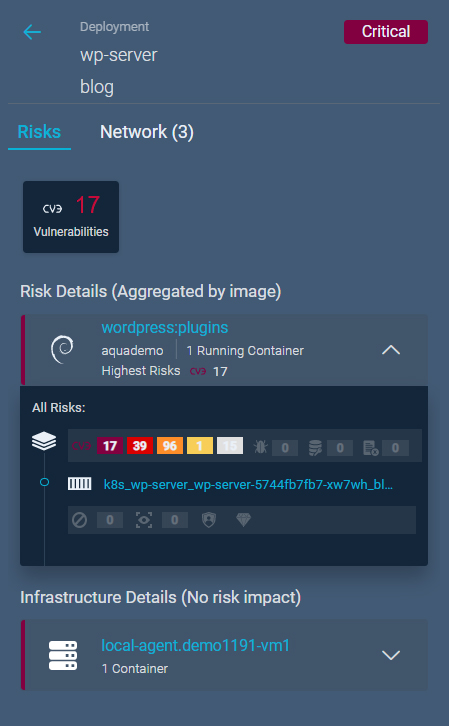
The calculated risk assessment score is an aggregation of evaluations of various objects. To drill down further, select the deployment, and the drill down pane displays the details of the risks associated with the selected workloads. It is possible to view the images that have running containers in this deployment, their security posture, and the security status of the running workloads:
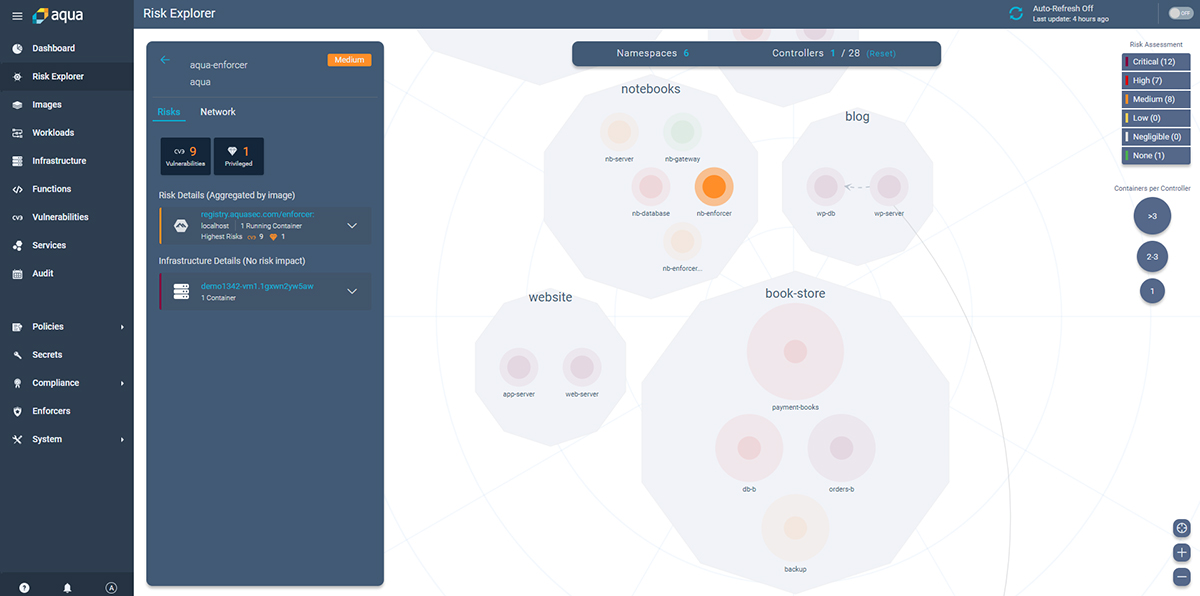
The drill-down pane shows detailed information about each risk, which includes risks that come from vulnerabilities, exposed secrets, bad configuration, malware, at the container as well as the node (host) level:
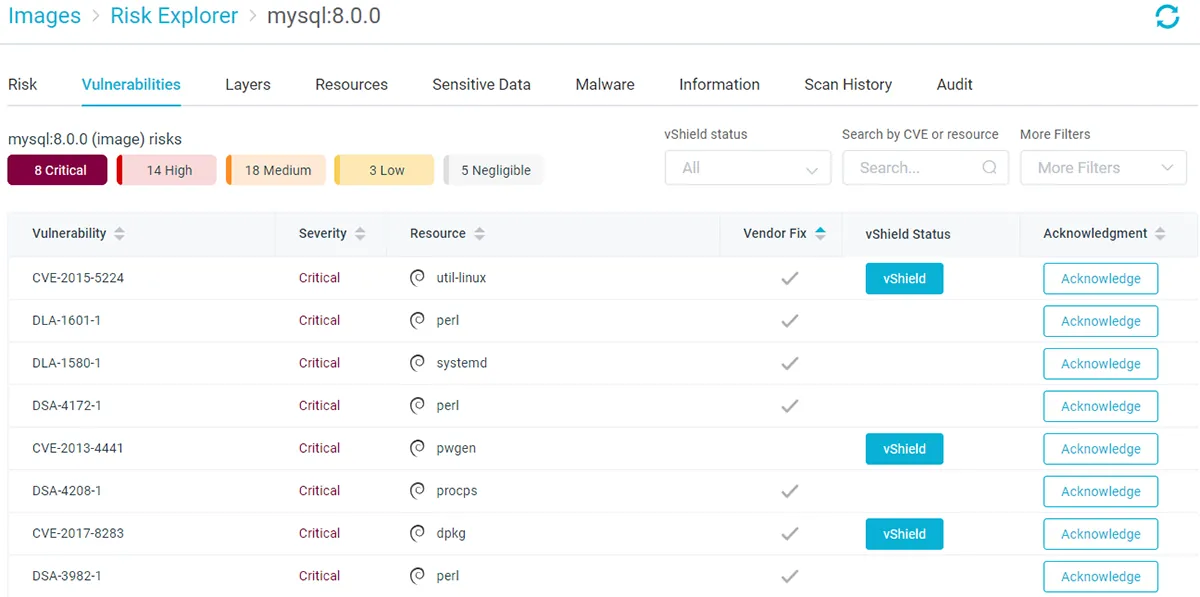
Clicking on a risk item in the drill down pane will open the relevant screen in Aqua Console with additional information concerning the risks as well as remediation recommendations:
Risk Explorer also displays an overview of the hosts running in the cluster, their risk assessment score and the deployments that are running on them.
What About Network Connections?
Risk Explorer maps the network connections for each deployment and shows the connections as inbound/outbound arrows. Selecting a deployment that connects with other deployments, or with entities outside of the cluster, displays the details in the drill down pane:
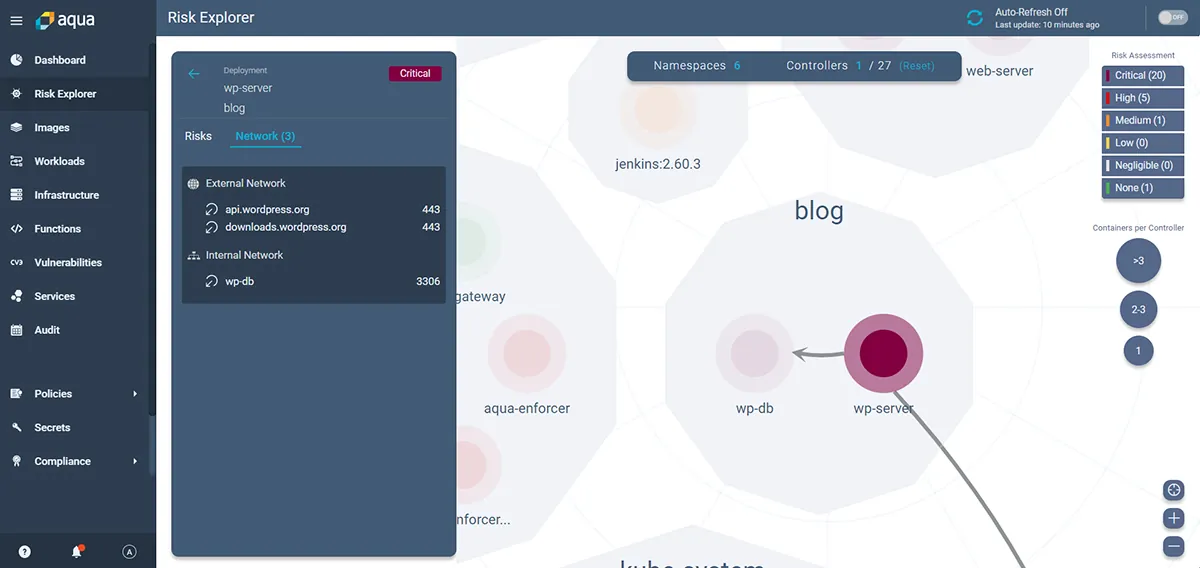
The network menu displays a snapshot of all network connections, their sources and destinations, making it easy to identify potential entry points to the environment.
Summary
Aqua Risk Explorer can help DevSecOps teams prioritize and focus their mitigation efforts on the most important issues in their Kubernetes environments.
For regulated industries that comply with and adhere to governmental and industry regulations, such as the Payment Card Industry Data Security Standard (PCI-DSS), Risk Explorer helps comply with chapters 6 and 10 of the PCI-DSS requirements that require the display of a visual map of vulnerabilities in running deployments, as well as all inbound and outbound network connections.
As organizations gradually move to larger-scale deployments of Kubernetes, it has become essential to get continuous real-time visibility into the shifting risk landscape they might present. Risk Explorer’s Kubernetes-native capabilities make that easier than ever.