Last month at KubeCon Europe, we released new Kubernetes security scanning for Trivy. It allows you to scan running Kubernetes clusters and resources for misconfigurations directly through the Trivy CLI or by installing the Trivy Kubernetes Operator in a cluster. In this blog, we’ll demonstrate how to use Trivy to scan Kubernetes resources and how to deploy it to your Kubernetes cluster.
When to use Trivy for Kubernetes scanning
As we highlighted in another blog, Trivy is the first unified scanner for cloud native security. Since it now has a whole bunch of different features, it’s important to understand when to use each of them during your deployment life cycle.
Generally, most security scanning for your resources happens before you deploy your workloads. This can include scanning your third-party libraries, container images, Git repositories, and your infrastructure configuration files. On each scan, Trivy will provide you with a list of vulnerabilities and misconfiguration issues. At this stage, you’d want to either use the Trivy CLI on your local machine or integrate Trivy into your CI/CD pipeline.
Once you’ve deployed your workloads to Kubernetes, you want to set up automated, continual resource scanning of your running workloads. In this case, you’d want to use either the Trivy K8s command or the Trivy Operator.
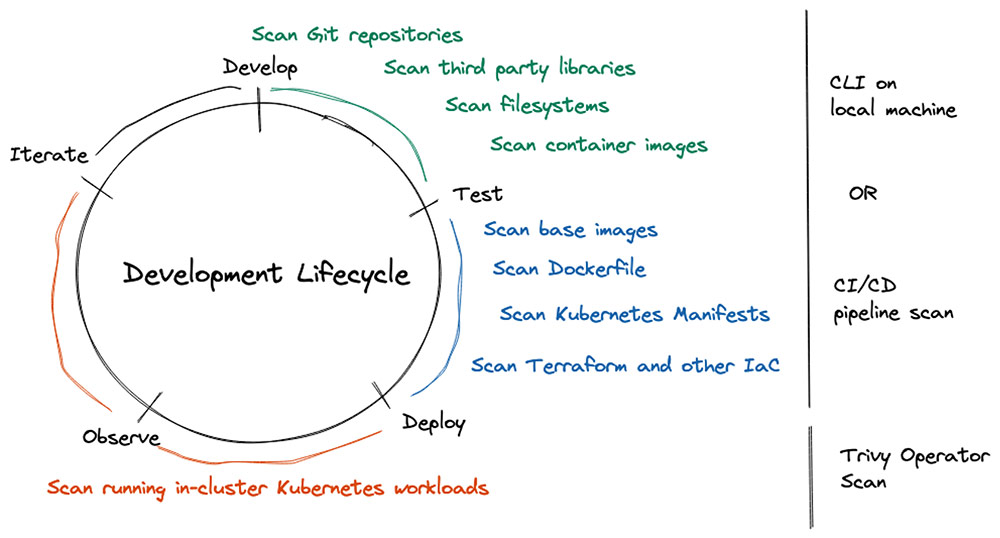
Trivy security scanning at different phases of your development lifecycle
Kubernetes scanning with Trivy
Prerequisites
To test the following commands yourself, make sure that you’re connected to a Kubernetes cluster. A simple kind, Docker-Desktop or MicroK8s cluster will do. In our case, we’ll use a one-node kind cluster.
Pro tip: The output of the commands will be even more interesting if you have some workloads running in your cluster.
Trivy K8s command
Trivy Kubernetes scanning is great to get an overview of all the vulnerabilities and misconfiguration issues or to scan specific workloads that are running in your cluster. You would want to use the Trivy K8s command either on your own local cluster or in your CI/CD pipeline post deployments.
The Trivy K8s command is part of the Trivy CLI:
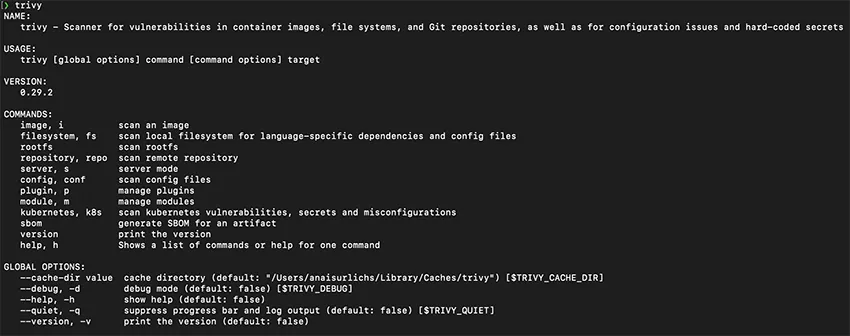
Trivy CLI options
With the following command, we can scan our entire Kubernetes cluster for vulnerabilities and get a summary of the scan:
❯ trivy k8s --report summary cluster
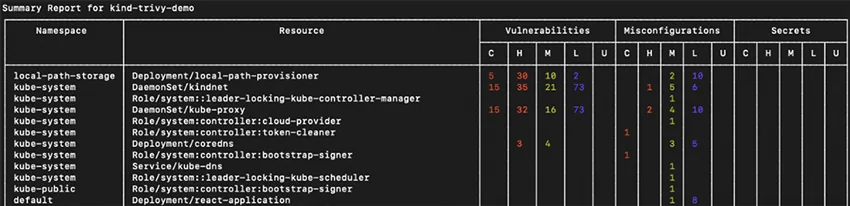
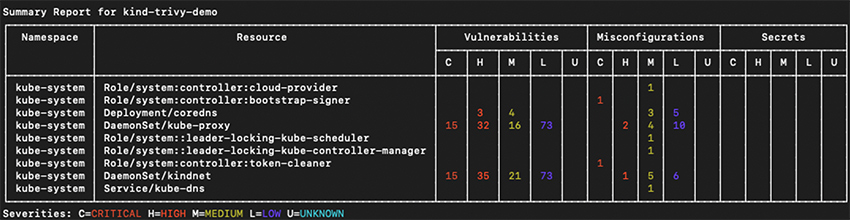
Using Trivy to scan your entire cluster for vulnerability and misconfiguration issues
To get detailed information for all your resources, replace “summary” with “all”:
trivy k8s –-report all cluster
However, we recommend displaying all information only if you scan a specific namespace or resource, because you can get overwhelmed with additional details.
Furthermore, we can specify the namespace that Trivy is supposed to scan to focus on specific resources in the scan result:
❯ trivy k8s --namespace kube-system --report summary all
Again, if you’d like to get additional details, use the “--report all” flag:
trivy k8s -n kube-system --report all all
As with scanning for vulnerabilities, we can also filter in-cluster security issues by the severity of the vulnerabilities:
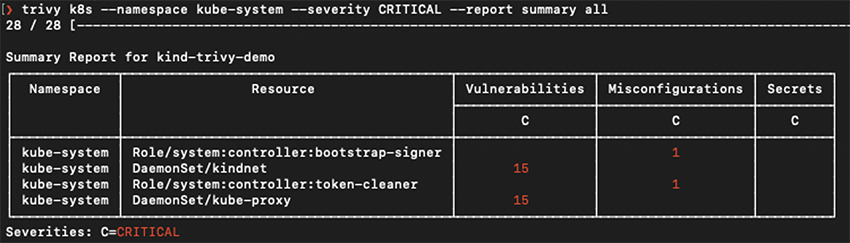
❯ trivy k8s -n kube-system --severity CRITICAL --report summary all
You can use any of the Trivy flags on the Trivy K8s command.
With the Trivy K8s command, you can also scan specific workloads that are running in your cluster, such as our deployment:
trivy k8s --report summary deployment/react-application
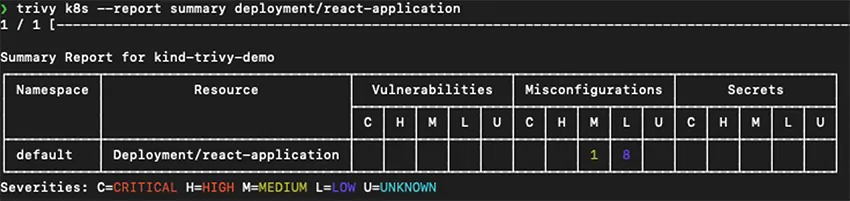
Using Trivy to scan a specific Kubernetes resource for vulnerability and misconfiguration issues
Trivy Operator
The Trivy K8s command is an imperative model to scan resources. We wouldn’t want to scan each resource manually across different environments. The larger the cluster and the more workloads that are running in it, the more error-prone this process can become. With the Trivy Operator, we can automate the scanning process after the deployment.
The Trivy Operator follows the Kubernetes Operator model. Operators automate human actions, and the results of the tasks are saved as custom resource definitions (CRDs) in your cluster.
This has a few benefits:
- Trivy Operator is installed as a CRD in our cluster. As a result, all our resources, including our security scanner and its scan results, are Kubernetes resources. This makes it much easier to integrate the Trivy Operator directly into our existing processes, for example, to connect Trivy with Prometheus, a monitoring system.
- The Trivy Operator will scan your resources automatically every six hours. You can set up automatic alerts in case new critical security issues are discovered.
- The CRDs can be both machine- and human-readable, depending on which applications consume the CRDs. This allows for more versatile applications of the Trivy Operator.
There are several ways that you can install the Trivy Operator in your cluster. In this guide, we’re going to use the Helm installation.
Make sure that you have the Helm CLI installed.
First, add the Aqua Security Helm repository to Helm:
helm repo add aqua https://aquasecurity.github.io/helm-charts/
Next, we can update our Helm repositories. This is a good practice before you start using a Helm chart to ensure that you have access to the latest changes:
helm repo update
Next, we install the Trivy Operator Helm chart in our Kubernetes cluster:
helm install trivy-operator aqua/trivy-operator
--namespace trivy-system
--create-namespace
--set="trivy.ignoreUnfixed=true"
--version v0.0.7
This is going to be the output of the Helm installation:
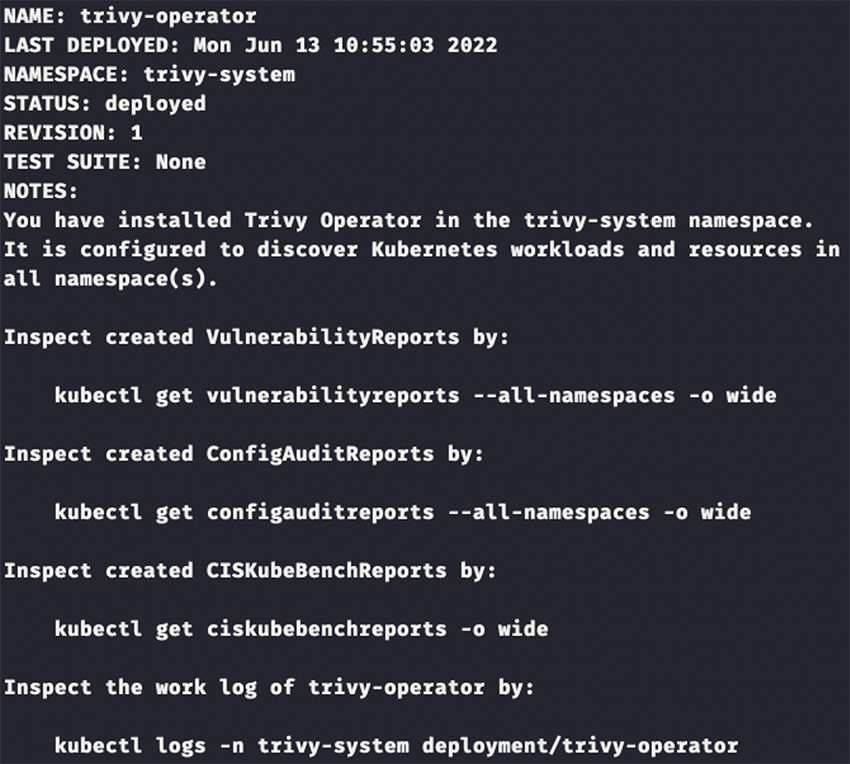
Output after installing the Trivy Operator Helm chart in your Kubernetes cluster
You can make sure that the operator is installed correctly via the following command:
kubectl get deployment -n trivy-system
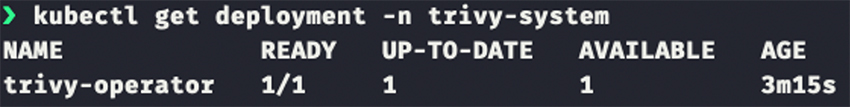
The Trivy Operator successfully installed and running in a Kubernetes cluster
The Trivy Operator successfully installed and running in a Kubernetes cluster
Trivy will start scanning your Kubernetes resources automatically. For instance, you can view vulnerability reports with the following command:
kubectl get vulnerabilityreports --all-namespaces -o wide
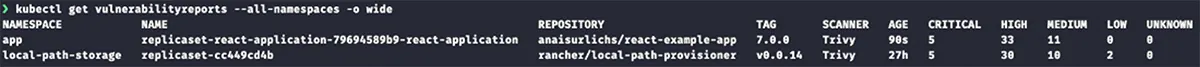
Using kubectl to query for Vulnerabilityreports
And then you can access the details of a security scan:
kubectl describe vulnerabilityreports <name of one of the above reports>
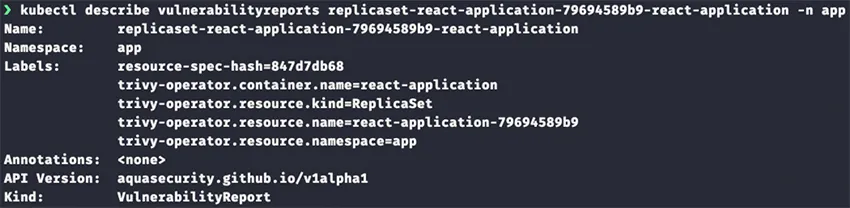
Using kubectl to display the CRD of a specific vulnerability report
The same process can be applied to access Configauditreports:
kubectl get configauditreports --all-namespaces -o wide
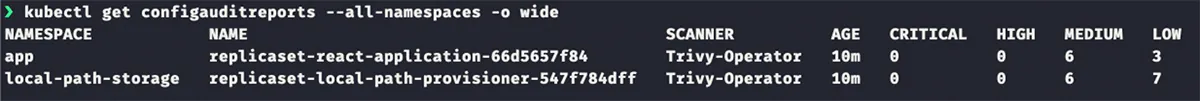
Using kubectl to query for Configauditreports
Summary
In this post, we covered the new Kubernetes security features in Trivy, including the Trivy K8s CLI commands and the Trivy Operator. Go ahead and give them a try yourself!
If you’re curious about the background of Kubernetes scanning in Trivy and how it came about, watch our previous livestream on our Open Source YouTube channel.
Stay tuned for more upcoming features in Trivy, such as additional in-cluster security scans and a web user interface. If there’s anything specific that you’d like to see, reach out on GitHub or Slack.
Make sure to give Trivy a star on GitHub ⭐ and join our community on Slack to share how you’re using Trivy on your Kubernetes clusters.