One of the great security benefits of the move to cloud native development is the increased use of Infrastructure as Code (IaC) to describe computing environments. Once things are described as code, we can shift left and secure our environments before they’re deployed. As a major new feature, the latest version of Trivy, Aqua’s open source project, adds support for IaC security scanning, covering Docker, Kubernetes, and Terraform. In this post, we’ll explain how you can start using it to detect security risks in your code.
What are IaC security tools?
IaC scanning tools can parse commonly used cloud native formats such as Dockerfiles and Kubernetes YAML and then apply a set of rules that encode good security practices, giving the user a view of where they can apply additional hardening to improve their environment’s security.
For example, they can detect such issues as a Docker image designed to run as the root user, a Kubernetes manifest requesting privileged access to a node’s file system or a Terraform script that configures a world-accessible S3 bucket.
IaC scanning tools can be used at multiple stages of the development process, by developers as part of initial authoring or as part of a CI pipeline in a test suite.
Getting started with Trivy IaC security scanning
If you’re already familiar with Trivy as an image vulnerability scanner, you can expect the same ease of use for IaC scanning as well.
The first step to getting started with this feature is to download and install the latest Trivy release. A wide range of supported installation mechanisms and platforms are available on the releases page and of course, remember to validate the provided checksums on your download.releases page and of course, remember to validate the provided checksums on your download!
Once you have installed Trivy, kicking off a config scan is relatively straightforward. For example, to scan a Dockerfile in a directory called Docker, you would just run:
trivy config Docker/
Trivy will then scan that directory for a Dockerfile and analyse it. Here’s a sample Dockerfile with some known issues in it, to use as an example:
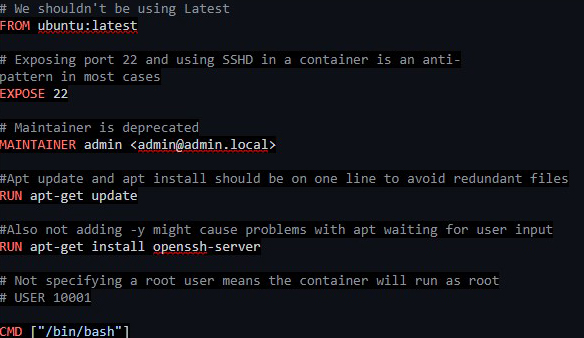
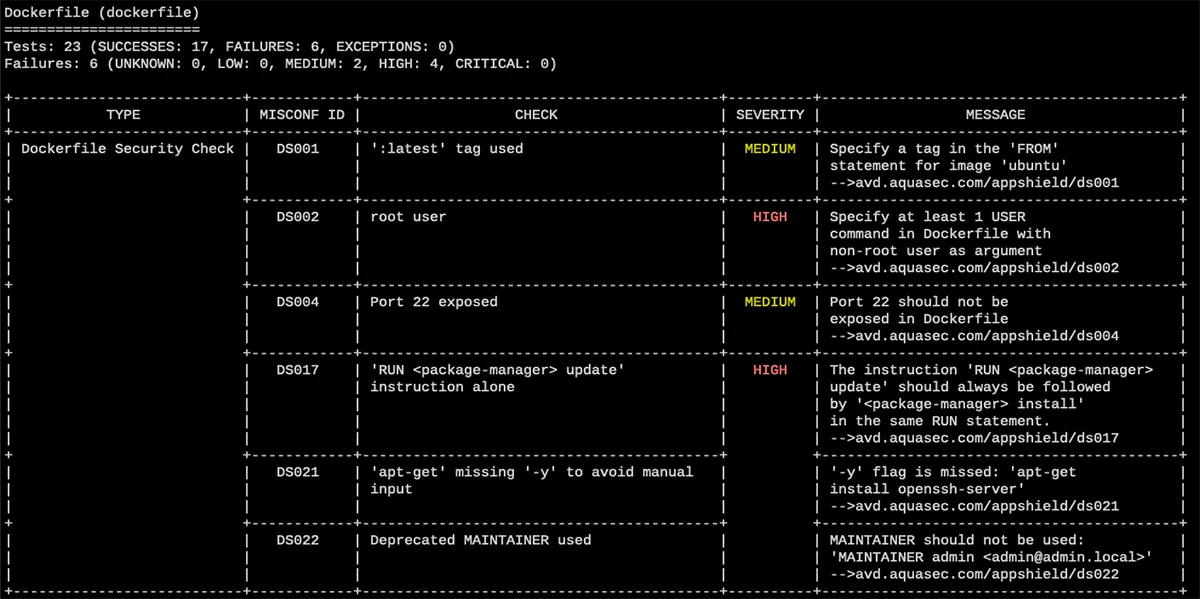
Running against this Dockerfile will give us several findings that flag each of the noted security issues.
Of course, if you’re using Trivy as part of a CI pipeline or other automated process, a text-based output may not work best for you. In that case, you can use the -f option to change the format of the output. So, to get JSON output for your scan you can use:
trivy config -f json Docker/
That will provide output that’s easy to parse and put into other tools.
IaC security scanning rules
The interesting part of any misconfiguration scanner is the collection of rules that define what’s good or bad. With Trivy, the policy database is maintained in a separate Aqua open source project called AppShield and is transparently synchronized to clients, just like the vulnerability database. It also provides a collection of policies described in the popular Rego language (which means they can be used by other scanning tools or admission controllers).
One of the advantages of this approach is that you can use the same policies for both IaC scanning and admission control. That can give you confidence that the same rules are being applied across the application lifecycle, and there is a lower chance of an application failing a security check when it’s deployed to a production environment.
For Terraform scanning, we’re making use of the excellent ruleset from the tfsec project, which recently joined Aqua. There are sets of checks covering the three major cloud providers and, as with AppShield, it’s possible to use the tfsec rulebase in multiple locations, helping to ensure consistent policy application through the development process.
Conclusion
IaC security scanning is an important part of ensuring the security of cloud native applications. It allows for quick identification of possible security issues and opportunities for hardening application artifacts such as Dockerfiles and Kubernetes manifests.