IT spend on public cloud will more than double by 2023 (IDC) and hybrid multi-clouds will soon be the more common environment for enterprises. The benefits of using cloud infrastructure including the ability to scale, ease of use and speed of application delivery are too attractive to ignore, however, the complexity of managing and administering these environments leaves organizations exposed to significant security risks.
Weaknesses such as servers unintentionally open to the public, unencrypted datastores, as well as missing or weak authentication are being exploited by attackers on a regular basis, as exemplified in the Capital One breach earlier this year.
The Need for Cloud Security Posture Management (CSPM)
At Aqua, we protect the largest cloud native workloads in the world. But if the infrastructure is not properly configured and continually monitored, the applications and organizations are at risk. For IaaS and PaaS environments, security posture management is the layer required for continual visibility, remediation and compliance. CSPM makes sure enterprises are using the cloud securely and continuously monitors and alerts on any identified risks – either accounts out of compliance or exposed to vulnerabilities.
Many customers are monitoring accounts with ad hoc methods, such as custom scripts based on best practices but there are too many services for this to really scale across teams and to effectively monitor the ever-growing set of cloud services. Cloud account administrators now need to act with a security and compliance mindset. Custom approaches are at best, inconsistent, with limited visibility into what is really happening across all of the available cloud services.
Introducing CloudSploit
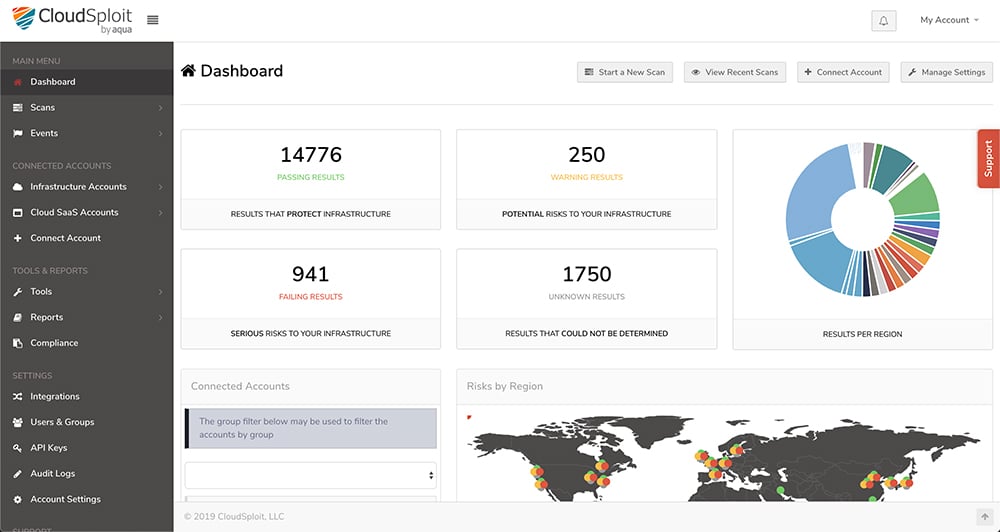
CloudSploit by Aqua continually monitors, and automatically detects security configuration issues in public clouds including AWS, Azure, Oracle, and Github. It examines user roles and privileges, certificates & MFA, specific service configurations, data encryption, networking, auditing features, usage trends and also conducts anomaly detection. As it monitors your environment, it provides alerts for remediation and reports for regulatory compliance as it benchmarks against CIS standards.
CloudSploit by Aqua is available both as open source and with expanded features for the enterprise. Customers can be up and running in minutes, monitoring their clouds. Users find CloudSploit easy to use with scans that are fast and to-the-point. Results are provided in line with best practices, and account-level overviews make it easy to see relative risk levels, and trends over time. CloudSploit’s API approach allows the creation of custom accounts and allows for integration into broader reporting systems for security or CISO dashboards.
Protection for Cloud VMs
Today, we are also announcing significant new capabilities for the Aqua Cloud-Native Security Platform (CSP), deepening protection for virtual machines. Aqua’s VM security solution is deployed as an Agent on either Windows and Linux OS. It can be delivered using different automation tools, such as Cloud Init, Terraform, Chef and Puppet. The solution provides features that are needed to secure hosts running on public or private clouds, including: file integrity monitoring, vulnerability and malware scanning, host hardening checks (based on CIS), network discovery and micro-segmentation to hosts for full visibility of infrastructure and application threats.
Organizations can now protect their cloud native workloads from a single control plane for improved visibility and efficient remediation.
For more information on our expanded offer for Cloud VMs, Read our recent blog post Cloud VM Security with Aqua CSP
The addition of CloudSploit and VM Security expands Aqua’s protection of cloud-native environments. Aqua’s customers can more effectively manage risk and protect against threats for their multi-cloud environments across the full application stack, spanning infrastructure, application workloads and code.



