One of the key challenges in container image scanning is understanding where a vulnerability originated in an image, and who can fix it. Image layers allow us to do that, and Aqua’s scanner now allows us to pinpoint discovered vulnerabilities to a specific layer.
Aqua CSP 4.2 sports many new features, including Aqua Vulnerability Shield and Runtime Security that we already blogged about. Additionally, we now have native integration with Prometheus, the open source monitoring tool, and the Harbor registry, popular in VMware Enterprise PKS environments.
Identifying Vulnerabilities by Layer: Accountability and Remediation
The read/write layers in images are generated during the image build. These layers are located on top of previous layers that are read-only. This layered approach enables developers to track image development, as well as reuse layers for other container images.
Layers give you information about the history of the image build, as well as information about who added the layer. In environments that are open to multiple developers, or shared open source projects, many different contributors might be involved.
Once you scan an image and identify a vulnerability in one of its components, operationally it’s useful to know which layer (or layers) it’s in. This can identify the individual or team who developed the layer, so you know who to go to, whether it’s to understand why this was added, or who can fix it.
When it comes to remediation, you might be able to either update the vulnerable package, or roll back the image to a previous version that preceded it.
Getting scanning results by layer is also an effective way of assessing the risk of a layer before reusing it in other images. For example, when a new package is added to an existing image, you check for any security risks before that layer is duplicated. This process can be automated and scaled according to your needs.
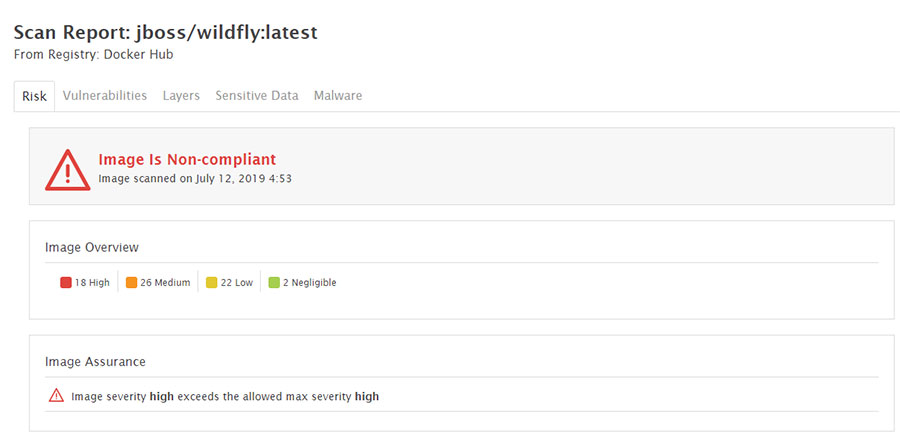
Let’s take a look at how this works, using Aqua’s scanning plugin for Jenkins. We’ve scanned the latest jboss:wildfly image, and we can see many high severity vulnerabilities that were consequently marked as non-compliant by Aqua:
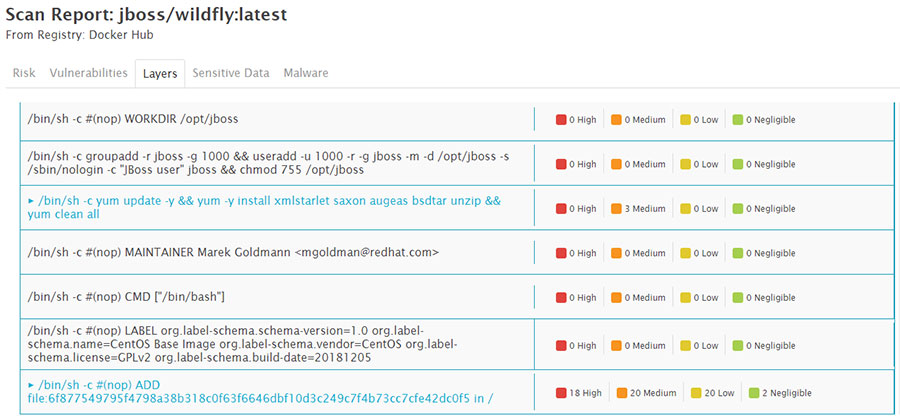
Clicking on the Layers tab will reveal the list of layers in the image, and it’s very easy to see that all of the layers are clean but one:
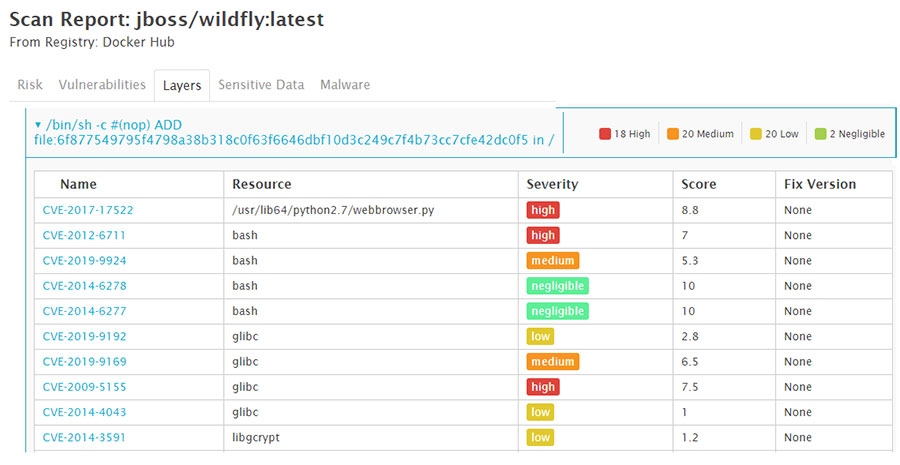
Expanding that layer shows the detailed CVE information and makes it easy to isolate the high severity vulnerabilities:
So while it’s sufficient to know which package or resource a vulnerability was found for us to be able to identify a fix, operationally, it’s useful to understand which layer it came from, since it gives us the option of understanding who added the layer, potentially rolling it back, and certainly avoiding the duplication of this layer across multiple images.
Native Prometheus Integration
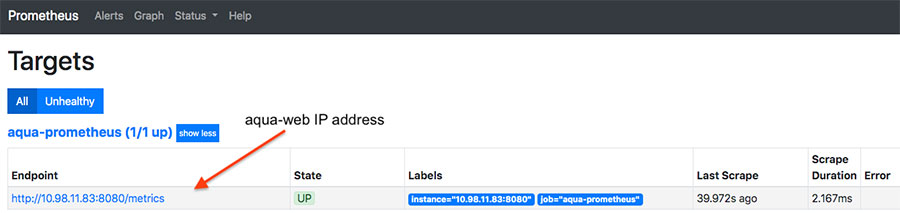
Prometheus is an open-source system monitoring and alerting solution, now natively supported in Aqua CSP 4.2. Prometheus is a poll-based system, which means it periodically looks for metrics exporters like Aqua (as shown below) and makes an HTTP request to them. It then stores that information in its time-series database and sends alerts as needed. Configuring and starting Prometheus with standard exporters, such as Aqua, is a straightforward process.
After your data is shared with Prometheus, you can use Grafana to get a visual representation of your metrics in real-time. Grafana, an open source tool, can export and import dashboards via JSON files. The example below is a visual representation of Aqua metrics and a Kubernetes dashboard using Grafana’s platform.

Since Prometheus is hugely popular in DevOps and cloud native environments, we’re hoping this integration will make the use of Aqua easier to monitor for performance and uptime.
Bringing You to a Safe Harbor
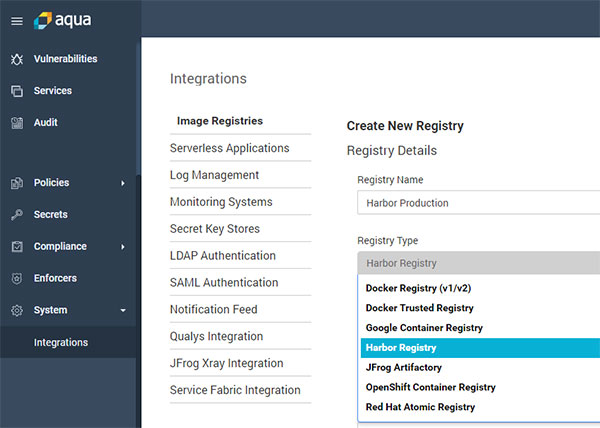
Aqua now provides native integration with the Harbor image registry. Harbor is an open source registry that stores, signs, distributes, and scans container images for vulnerabilities, and is used as part of the VMware Enterprise PKS environment. The integration can be configured in an Aqua Console with a few easy steps. Part of Aqua’s commitment is to support all popular components of the cloud native ecosystem, and Harbor now joins a long list of registries that includes Docker Hub and DTR, OpenShift/Quay, Jfrog Articfactory, Sonatype Nexus, and all of the major cloud-based registries.
Continuous Innovation
With every major release, Aqua adds several key innovations as well as deeper functionality, ease-of-use improvements, and wider interoperability with other tools. Watch this space for additional updates about our recent release.
