Today, Aqua announced the addition of a new, industry-leading detection and response capability to its Cloud Native Application Protection Platform (CNAPP), called Cloud Native Detection and Response (CNDR). CNDR uses real-time behavioral indicators from Aqua’s cyber research team, Nautilus, to identify zero-day attacks from low-level eBPF events surfaced by Aqua’s open source project Tracee. Combined with Aqua’s cloud workload protection platform (CWPP) controls, CNDR is the first solution that can detect and respond to attacks in runtime with minimal disruption to production.
CNDR provides key detection as part of Aqua’s broader CWPP controls
Gartner defines CWPP as a combination of scanning and runtime protection for cloud workloads.
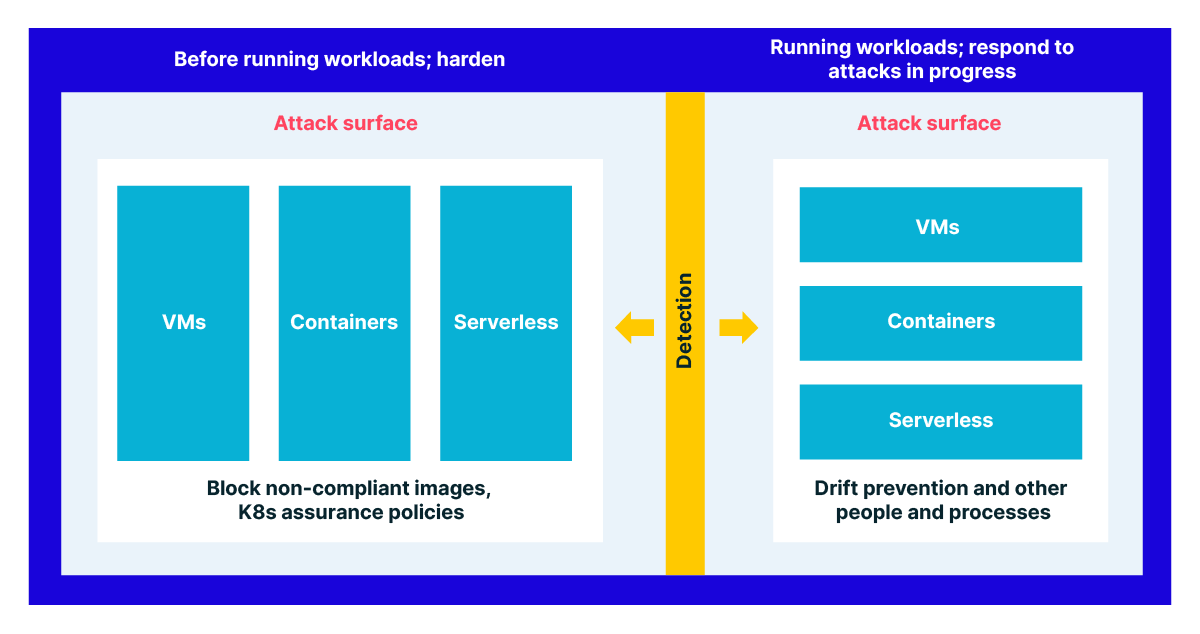
Aqua’s CWPP capabilities involve a robust set of runtime controls for layered VM, container, and serverless workload protection. These controls act as layers for a defense-in-depth strategy to harden workloads before they are run, and then to respond quickly and in real time to attacks in progress in the production environment.
Some runtime controls act as an acceptance gate for a workload, defining what can and can’t run. Micro-segmentation policies determine acceptable traffic between nodes, clusters, and hosts, while Kubernetes assurance policies dictate the Kubernetes configurations that must be present (or that cannot be present) for a workload to be allowed to run.
Other runtime controls respond in real time to stop attacks in progress. For example, drift prevention maintains the immutability of containers in runtime; any behavior that was not intended as part of the behavior of a container in runtime will be prevented. Drift prevention takes advantage of the immutable properties of containers to stop the bad behavior without the necessity of knowing what’s causing it. Another example of a real-time response is vShield, which will prevent the ability to exploit any vulnerabilities that cannot be fixed.
It’s important to note that any CWPP—but especially those that protect container, Kubernetes, and serverless workloads—should provide protection while maintaining uptime and minimizing disruption in production.
CNDR adds a critical layer of detection
Teams that can respond in real time to attacks in progress, mitigate exploits, and set preventative hardening controls in runtime are doing well by their overall security posture. Detection brings in another layer of key information that can be used in a feedback loop along with these other controls to make them more effective as part of a larger goal around risk management.
The five functions of NIST, which are the highest level of abstraction for NIST guidelines, put detection squarely between hardening and response capabilities.
To summarize, the protect function generally refers to hardening capabilities that would contain the impact of a potential incident. In a cloud native environment, this would include the shift-left capabilities of a CWPP solution, as well as some of the preventative, hardening runtime policies.
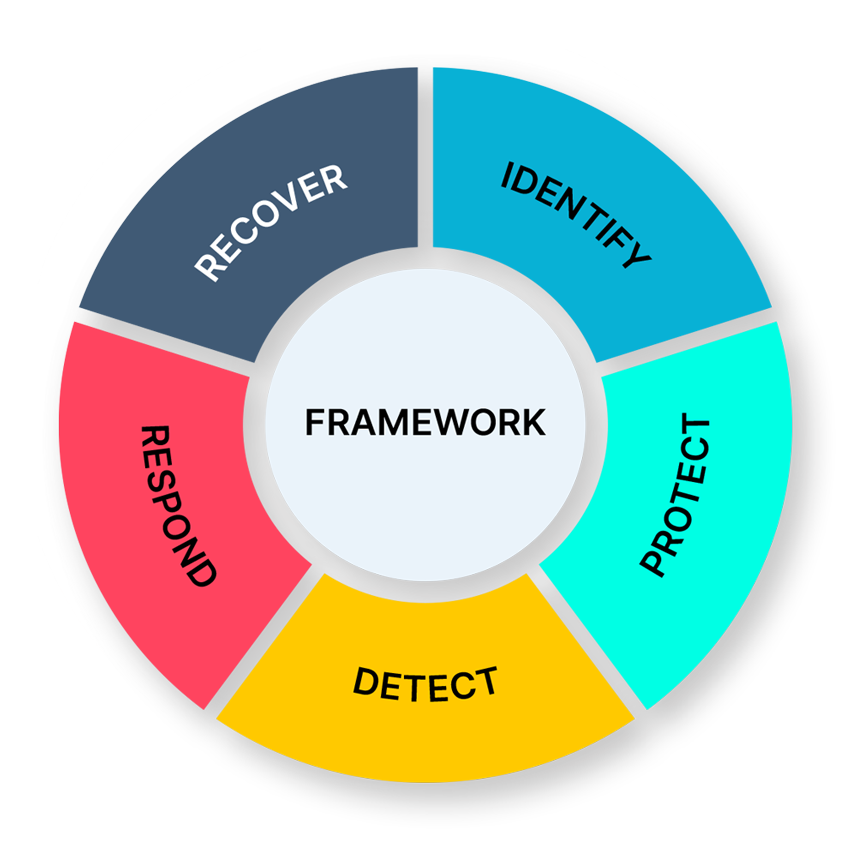
The respond function refers to active mitigation. A cloud native security equivalent would be a feature like drift prevention, which can control the behavior of the container without having to know exactly why the container is behaving badly.
The detect function involves rapid identification of security events and their impact, and is important in cloud native security for the same reasons it might be important in another environment:
- Security teams don’t operate in a vacuum. They need to be able to show the details of what’s happening in their environment to auditors, other teams, and customers.
- It’s much easier to attain budget with real-time proof of an attack in progress and the impact to the production environment.
- Detection provides an opportunity to set more effective preventative and hardening controls. See this chart for what that looks like with CNDR and Aqua’s other runtime controls:
- Security teams also react to attacks and security events with people and processes. In this case, they require detailed direction for their response. For example, the database with the customer data is breached; shut it down now.
What should detection and response look like in a cloud native environment?
Detection and response must take into account the specifics of a cloud native environment:
- Detection must include the breadth of workloads for a cloud native environment, including containers, VMs, and functions.
- It must detect the tactics used in attacks that target cloud native environments.
- It must be able to detect both known and unknown attacks in those environments.
- Detection must occur in real time and be minimally disruptive to production.
- The data must be actionable as part of a feedback loop with response mechanisms.
The technology matters when covering cloud native workloads and achieving minimal workload disruption
CNDR uses eBPF technology to achieve workload coverage and minimal disruption. eBPF is a lightweight option to run programs on the Linux kernel. (For more information, see A Deep Dive into eBPF.) It provides a way to run programs on the kernel with less risk of the kernel crashing, compared with the legacy technique of kernel modules. On its own, eBPF is a way to accomplish any number of ends; for example, it is also being used across the board for networking and monitoring capabilities in cloud native environments.
Aqua Tracee is an open source eBPF-based threat detection engine that can identify more than 300 syscalls from the Linux kernel, along with other key events. CNDR is built on Tracee and uses eBPF to gain workload visibility with minimal disruption.
Detecting unknown cloud native threats from eBPF events
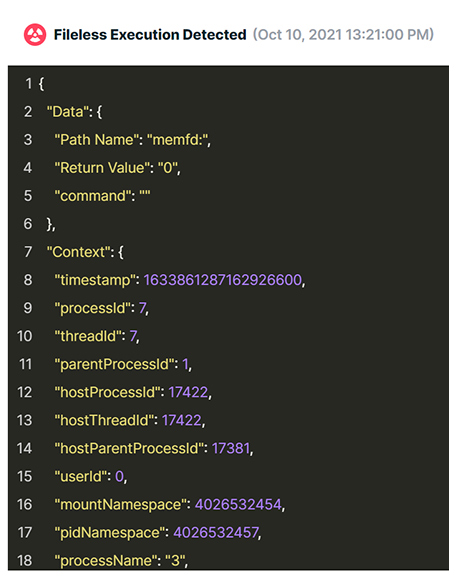
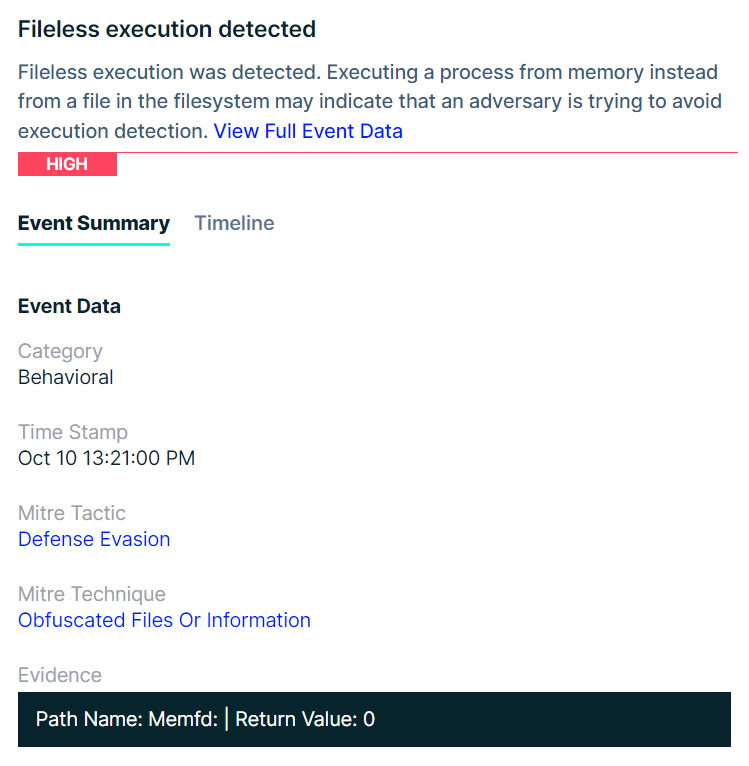
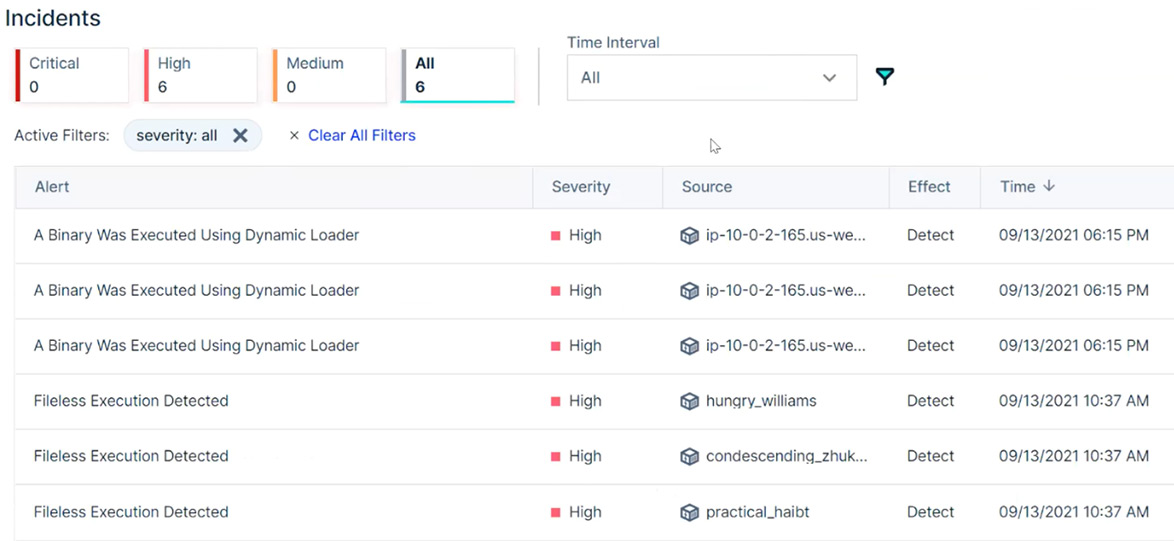
To discover unknown attacks that target cloud environments, CNDR uses behavioral indicators based on intel from Aqua’s cyber research team, Nautilus. These findings are based on intel from attacks in the wild on cloud native environments, including Linux, containers, serverless, and Kubernetes workloads—for example, a rootkit tactic that involves loading a malicious kernel, execution of fileless malware, or reverse shell. This screenshot shows a behavioral indicator of fileless execution.
In addition to behavioral indicators, Aqua’s threat intelligence includes IP and DNS reputation intel and a malware database, giving CNDR and Aqua’s customers access to the most complete threat intelligence feed for cloud native application security.
This is the incident screen that displays the details from both the known and unknown attacks.
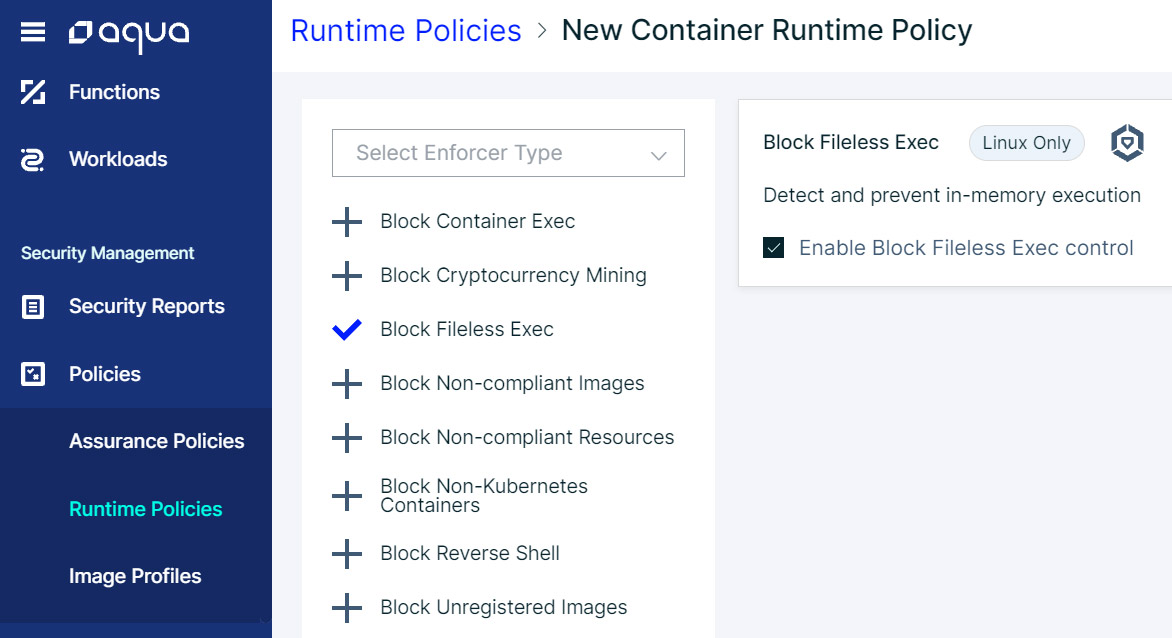
The feedback loop of detection to response is as critical as
detection itself
There is no point in detection without response, or without the ability to set more effective preventative controls. Above, fileless execution was detected as a behavioral indicator by CNDR. Below, we see a preventative runtime policy that can be set specifically to block fileless execution within the container identified by CNDR. This policy can be changed and take effect in real time, without disruption to the workload. CNDR is the only solution in the industry that, combined with Aqua’s other runtime controls, can both detect and respond with minimal disruption in production.
Learn more about CNDR
Talk to Aqua Sales today to try CNDR and see what threats are actively progressing in your environment.
Or get Tracee up and running in your Kubernetes cluster to get an easy view into the common container escapes in your environment.
Read our press release for more: Aqua Security Unveils Industry-First Detection & Response for Zero-Day Attacks in Cloud Native Environments.
