A few weeks ago we released Aqua MicroScanner, a free vulnerability scanner that you can embed into the dockerfile and automate scanning during image build.
A few hundred users later and with feedback we received from the community, we’re now happy to release a native Jenkins plug-in for MicroScanner.
How it Works
For a quick walk-through, this 3 minute video shows a demo of the MicroScanner Jenkins plugin. Additional info available below and on the plugin’s Github page.
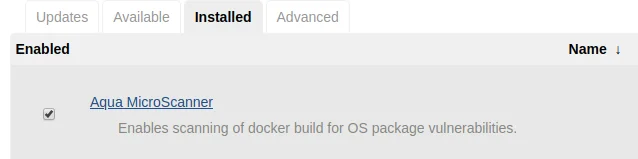
To use the plugin, you need to get an activation token for MicroScanner. Once that’s done, you can install and configure the plugin, and enter your token to activate.
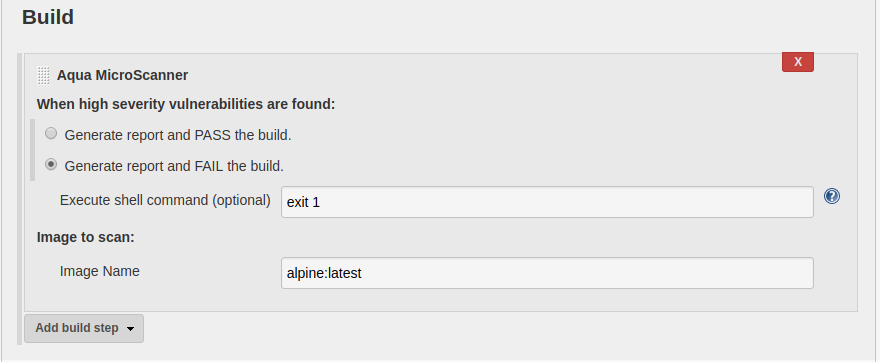
You can now use MicroScanner as a step in your build. For freestyle builds, you add a build step for Aqua MicroScanner. You can choose whether high severity vulnerabilities found in your image will fail or pass the build:
For pipeline jobs, you can insert MicroScanner into the build step script, like so:

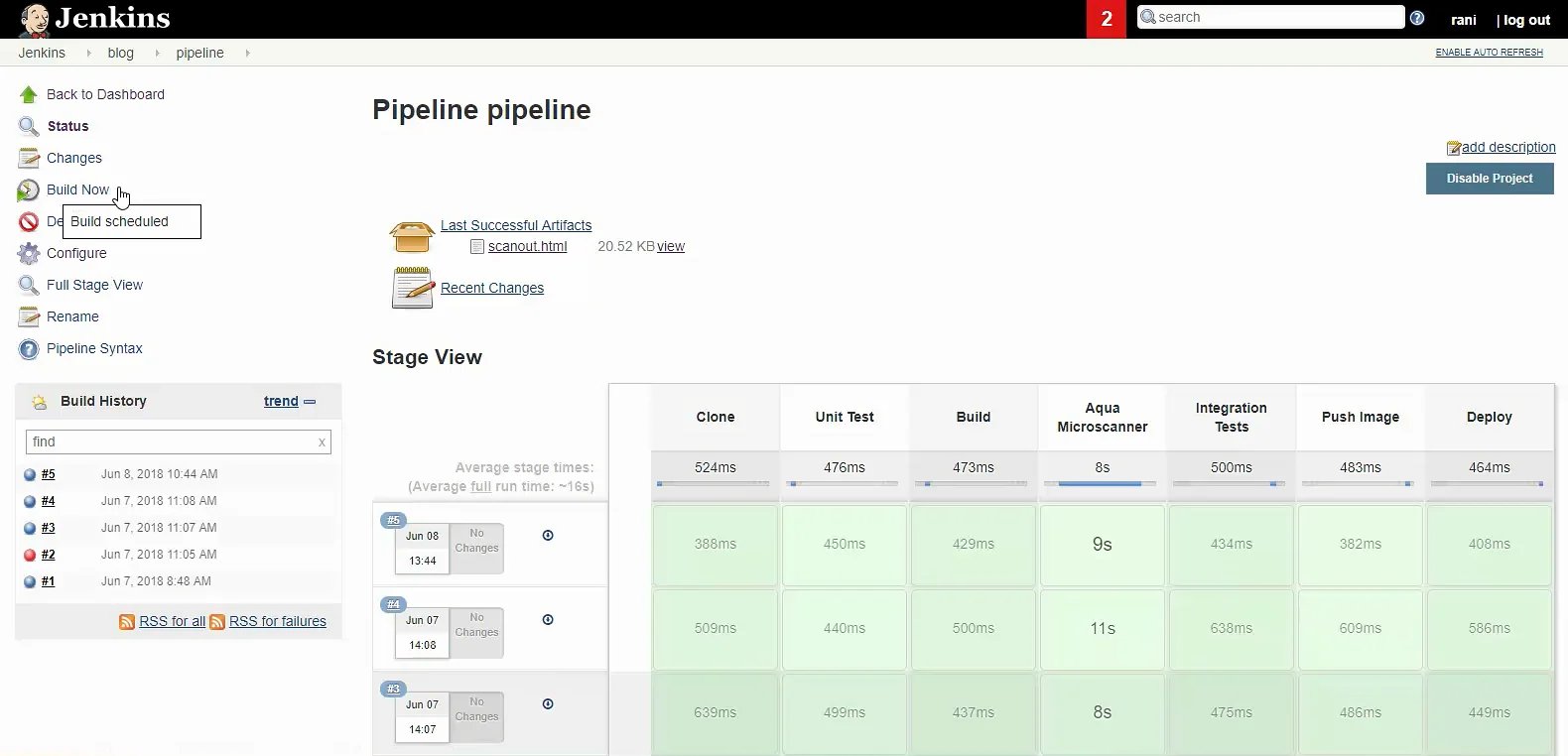
Upon running the pipeline job, the Aqua MicroScanner is now a stage in your automated build:
MicroScanner Output
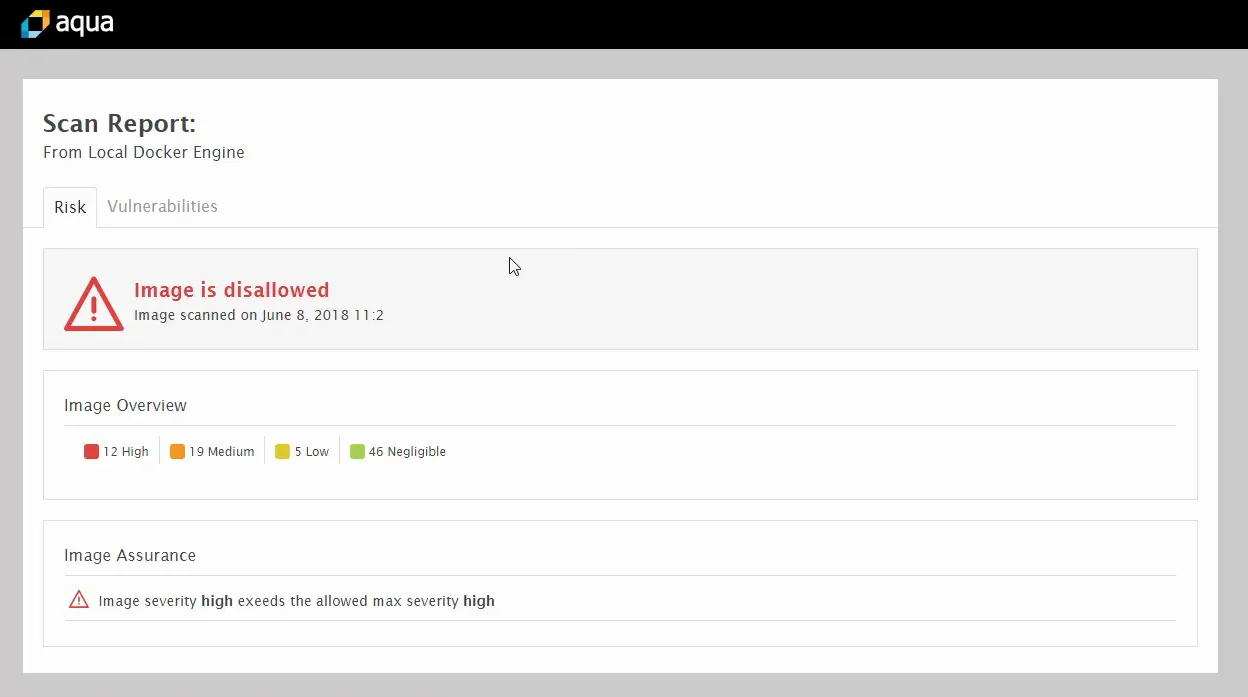
In addition to optionally failing your build, MicroScanner provides a report on the vulnerabilities found during your image build. If you configure HTML support in Jenkins, those can be nicely formatted HTML pages.
The scan report gives you a high-level overview of the number and severity of vulnerabilities that were found:
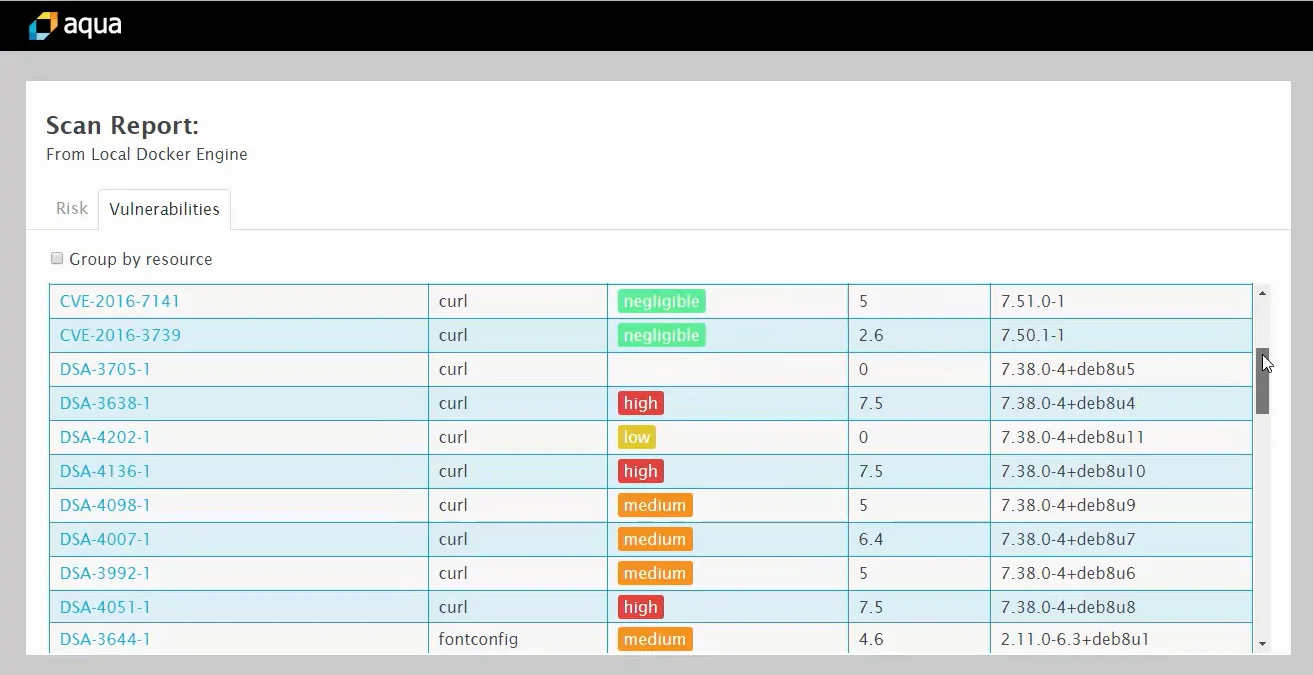
Clicking the Vulnerabilities tab will display a detailed report of all vulnerabilities. Note that this may contain not only CVEs but also vendor-published vulnerabilities that may not yet (or not at all) be listed as CVEs:
No More Excuses
We’ve made MicroScanner very easy to use, and the Jenkins plugin makes it even easier to use and automate. There’s really no excuse for building images that include risky known vulnerabilities when it’s so easy to avoid them at no cost. So make this an integral part of your build process – starting today!