Last month at VMWorld we had the pleasure of being part of a next-generation security session given by VMWare’s SVP of Security Products, Tom Corn.
VMWare is of course no stranger to containers, and already has hybrid platforms running both VMs and containers side by side. The gist of VMWare’s next gen approach is what they call “The Goldilocks Model”, where there’s a layer on the hypervisor that can also access elements of what’s running on Guest VMs to get a manifest of application security privileges. This allows for the ability to exercise ‘least privilege’ in the context of the application, feeding from various sources including, of course, containers.
This approach is very much aligned with Aqua’s own security model, where we use both default and machine-learned container profiles to enforce and tighten the ‘least privilege’ principle in runtime.
We also use a similar approach to VMWare’s in providing application context, by tagging containers to specific applications. This allows for easier, contextual policy management as well as automated nano-segmentation of container network connections.
The Aqua-Goldilocks Integration
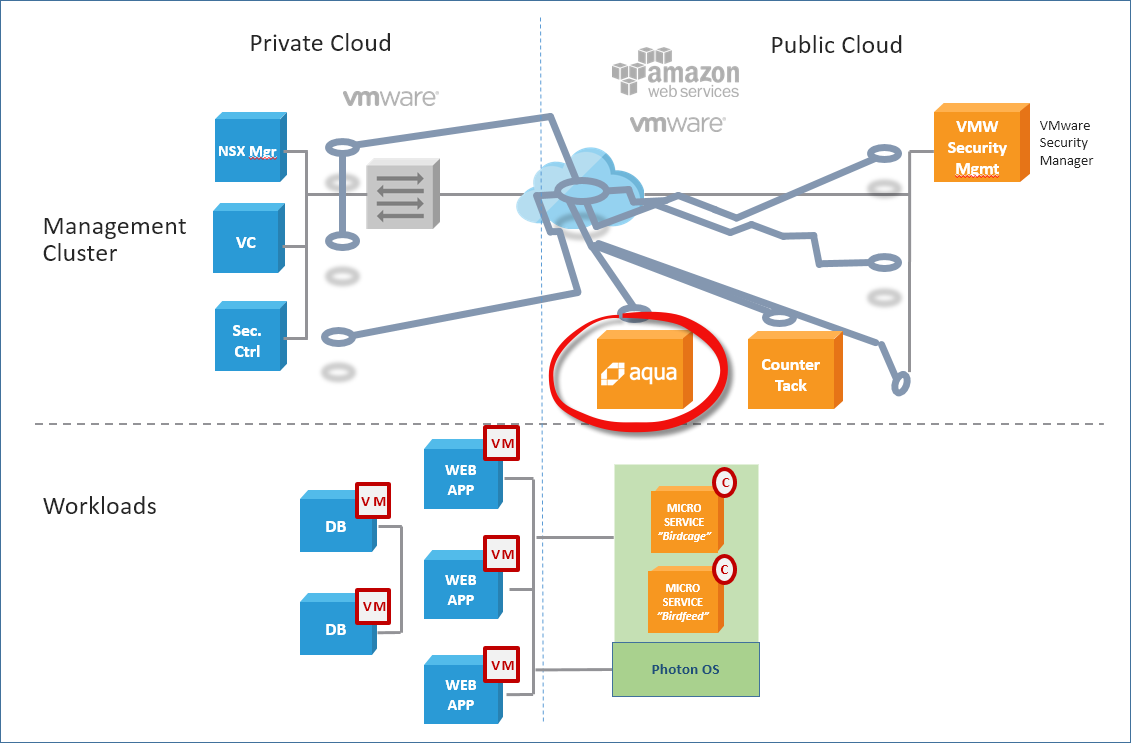
VMWare customers run applications on both VMWare VMs and Docker containers, and require a unified way to secure these environments from a policy management and visibility perspective.
To that end, we created an integration with VMWare’s next generation console. The integration is bi-directional and allows customers to do two things:
- You can use Aqua’s image profiles to set the least privilege manifest for a container and associate it with an application. This is then visible in VMWare’s console that shows a mapping of the “desired state” of the entire application, i.e. its declarative security policy. So if the application has container components, they will show up here.
- Aqua then acts on the policy and detects/prevents unauthorized activity, sending the event information back to the VMWare console.
You can view the full video of the presentation and live demo at the bottom of this blog (set to start at the point where Tom and Chris Corde, Sr. Director of Security Products, show how Aqua is works seamlessly with Goldilocks).
Understanding The Use-Case
In the demo shown by VMWare, they created an actual application that mimics an online mortgage application. Chris is an attacker trying to breaking into the app and reset his mortgage debt.
Goldilocks can integrate with various security solutions, both VMWare’s own as well as 3rd party vendors for endpoint security or container security, demonstrated in the demo.
For example, Chris tries to run an executable from within a container, which would normally be permitted. But under the restrictive Aqua policy, the container can only run specific executables and not the one Chris tries to run.
Consider this demo a glimpse into the not-so-distant future of application and virtual datacenter security, courtesy of VMWare. However, I’d like to note that all Aqua features shown in this demo are available now, and you are welcome to see them for yourself by requesting a demo
