Good news for those of you running container workloads on GCP – we now provide a nice integration with Google’s Cloud Security Command Center. The Cloud SCC provides a centralized, single-pane-of-glass view of all security data for GCP applications, and providing actionable insights. It includes things like access control monitoring, asset inventory, vulnerability assessment data, anomaly detection, etc.
Now, with Aqua, you can also view container security data in Google Cloud SCC, including:
- Inventory of vulnerabilities in container images in Google Container Registry (GCR), and alerts on new vulnerabilities
- Container user security violations, such as privilege escalation attempts
- Attempts to run unapproved images
- Policy violations of container network, process, and host resource usage.
How it Works
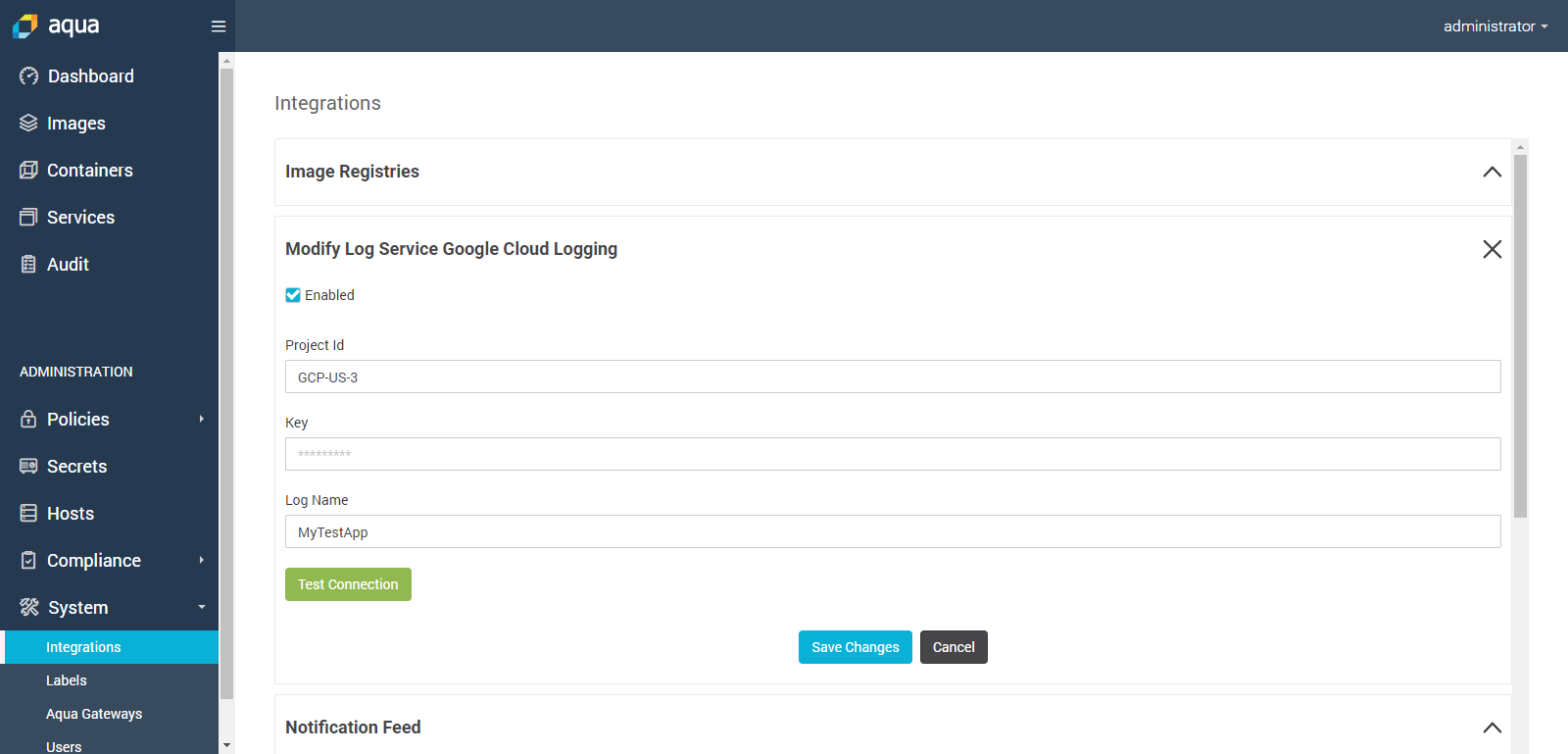
The first step is to set up the integration. This is done very much like our other integrations with SIEM solutions, such as ArcSight and Splunk, with a dedicated connector configuration:
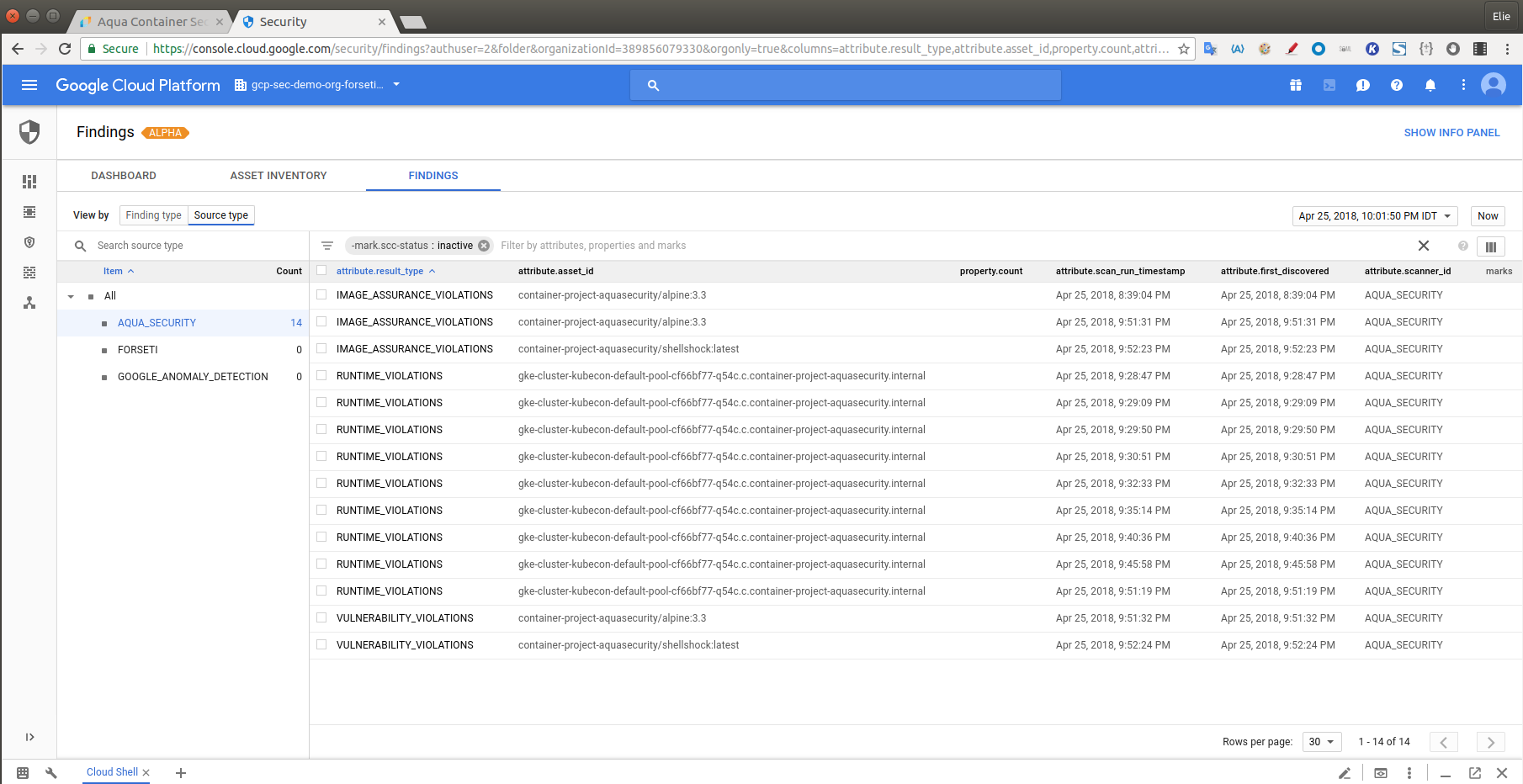
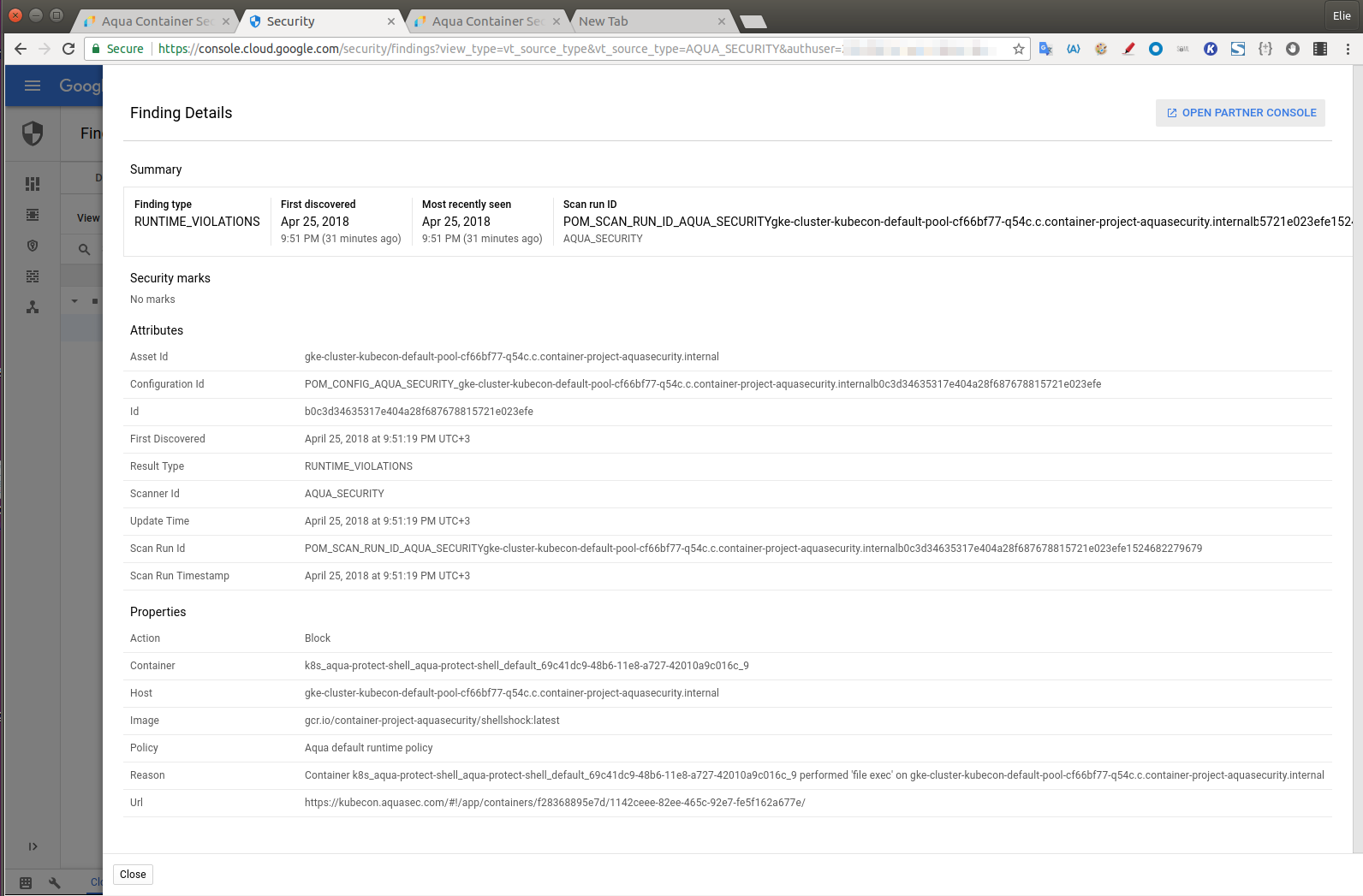
Once this is set up, you’re ready to go – the data from Aqua is mapped to Cloud SCC and will appear in the FINDINGS screen under the Source Type=AQUA_SECURITY. In the example below you can see various types of results including vulnerabilities found in image scans, runtime violations, and image assurance violations (when an image did not meet the policy to be approved for deployment).
Let’s drill down into a runtime policy violation. First, let’s see what it looks like in the Aqua command center:
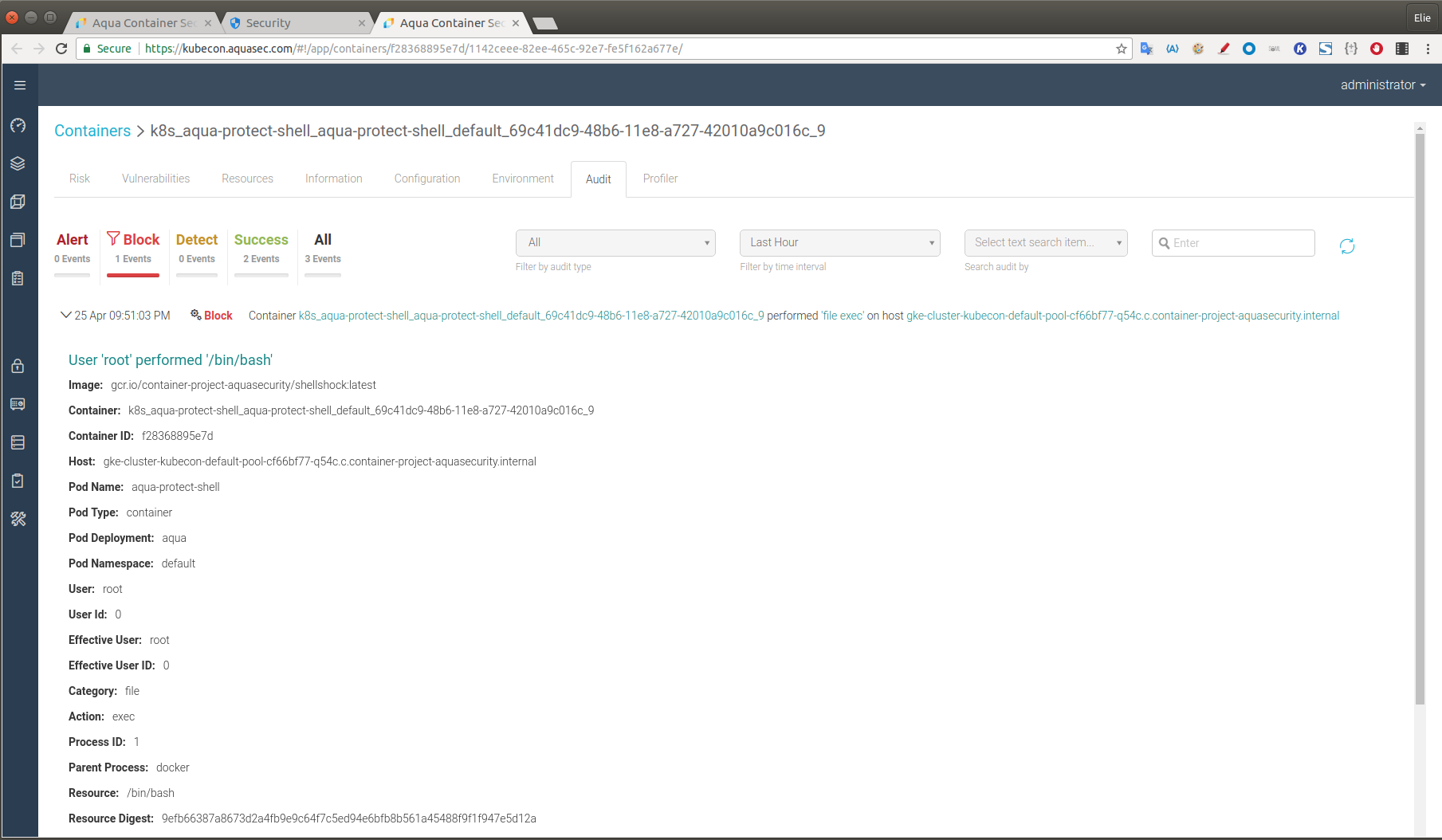
What we see is a blocked attempt to access the bin/bash library, which is open to the vulnerability known as Shellshock, allowing an attacker to attach malicious code to a Bash shell script environment variable.
And here’s that same information as it appears in the Google Cloud SCC:
Of course the benefit of having this information in a tool like Google’s Cloud SCC is that it aggregates and correlates data from a multitude of sources including other 3rd party security vendors, as well as Google’s own services such as Google’s Compute Engine, Cloud storage, and App Engine.
This is yet another step in our ongoing efforts to secure the development and application delivery on the Google Cloud Platform.
