Aqua CNAPP is focused on making the platform more scalable for our customer deployments, which include some of the world’s largest container setups.
Multi-Tenancy Management
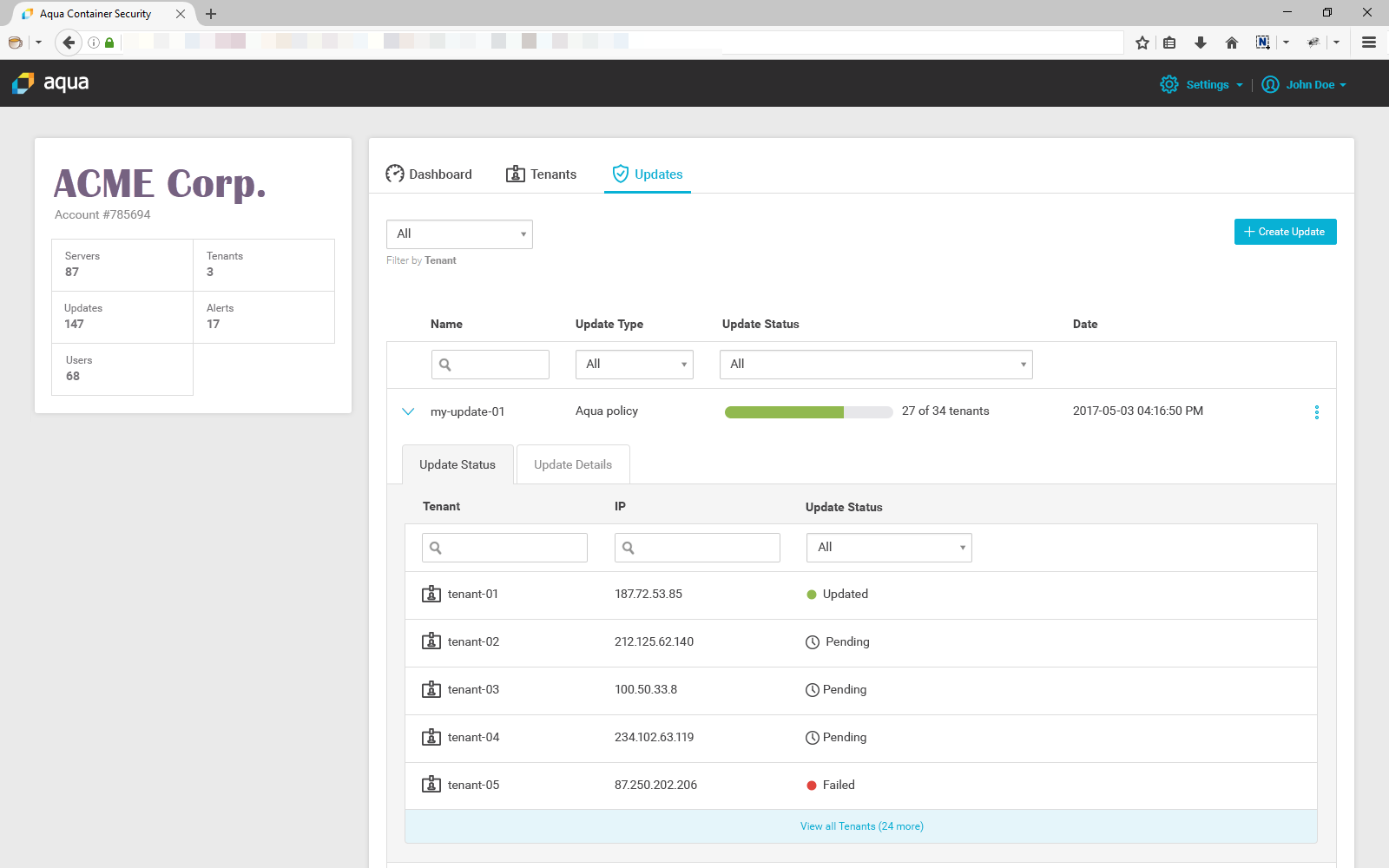
The biggest new addition in Aqua 2.5 is multi-tenancy, which provides a common architecture and UI for managing multiple tenancies, while also delegating some management capabilities to the tenant level.
This new architecture was created to support services providers as well as enterprises that want to create “container-as-a-service” (CaaS) offerings to their external and internal customers. The top-level admin can define allowed base images, image policies, and container runtime policies. Those policies are then bequeathed to tenants, who can then either use them as is, modify them, or define their own policies. At the same time, data and reports from the tenant levels roll up to the top level, allowing to monitor and enforce policies globally.
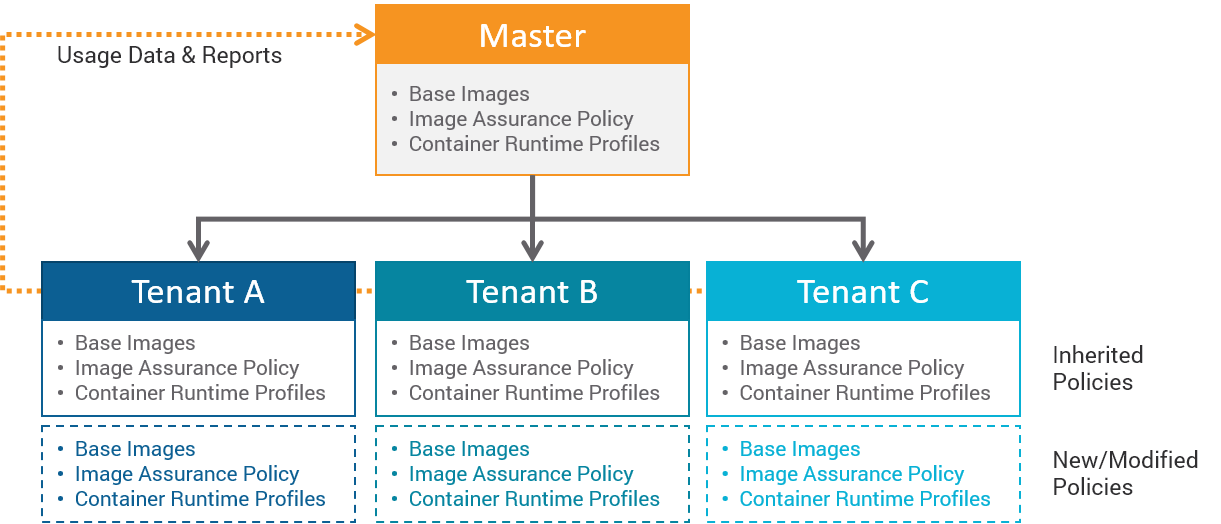
This is a very handy functionality for enterprises that have on the one hand corporate-wide container initiatives, but diverging security requirements for different teams or departments. It allows them to install a single instance of Aqua CSP, and mandate certain policies while leaving room for independent departmental security and compliance policies to be created and managed at the departmental level.
There’s also full data isolation between tenants, so service providers can also use this feature to allow customers to use Aqua within a CaaS environment. In such cases, normally the service provider may offer some default policies to customers, but they are more likely to use their own.
Integrations for Secrets Management
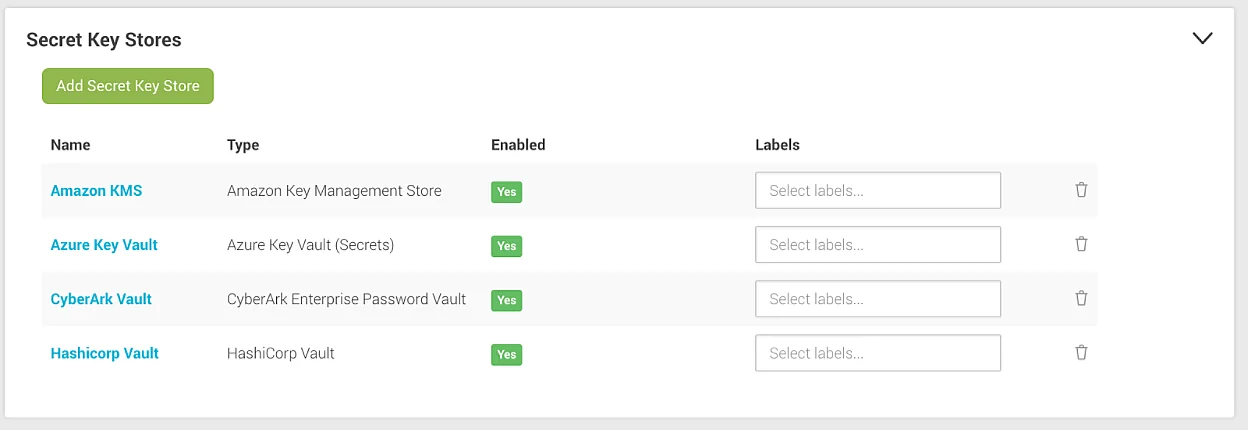
Aqua 2.5 also adds native support for Azure Key Vault and CyberArk Enterprise Password Vault as secrets stores for container secrets. This, in addition to HashiCorp Vault and AWS KMS that are already supported.
These new integrations allow customers to manage secrets centrally using any of these four popular tools, while Aqua ensures that secrets are only made accessible to the right container in runtime, are encrypted in transit, and never persist on disk.
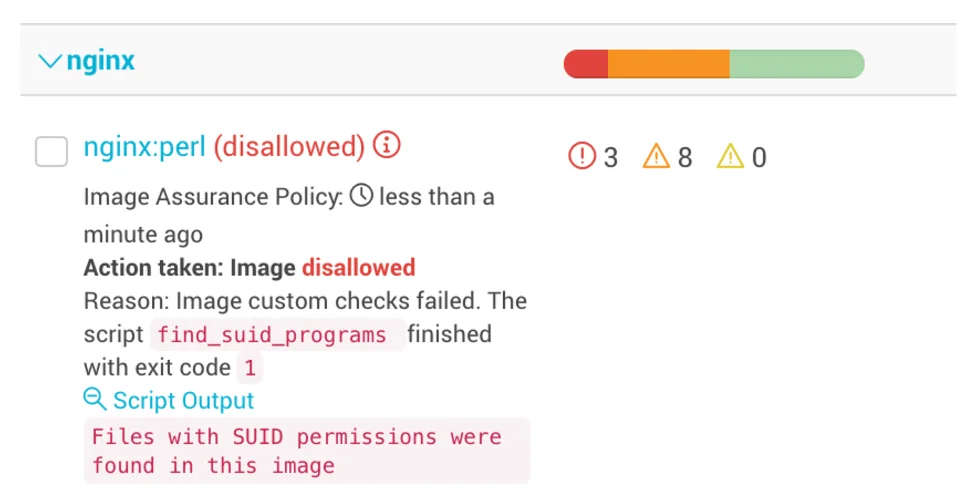
Custom Image Compliance Checks
In Aqua 2.5 you can add your own custom compliance checks into the image assurance process. This means that if you have a 3rd party tool, or a home-grown script that you’ve been using to check anything in the image from OS used to configuration parameters to custom vulnerability scans, Aqua now allows you to do that as part of the automated image assurance process.
Improvements in Machine Learning of Container Profiles
Since Aqua version 1.0 we’ve used machine learning to automatically baseline container behavior for the purpose of wrapping a container in a security envelope that prevents it from performing activities that are not necessary in the application context. One year and dozens of customer deployments later, we’ve been able to fine tune and improve these automated profiles, allowing faster and more accurate results.
Machine learning is not a one-off process, and we expect to improve and deepen this capabilities on a continuous basis. In version 2.5 we’ve implemented new algorithms that leverage the fact that images are built from other images. This allows us to reuse dataset between containers and provide full image profile in few minutes.
As before, profiles can be used to block the offending activity, or to only alert on it. Additionally, the learning process itself as well as applying profiles do not require containers to be restarted or interfere with the operation of running containers in any way.
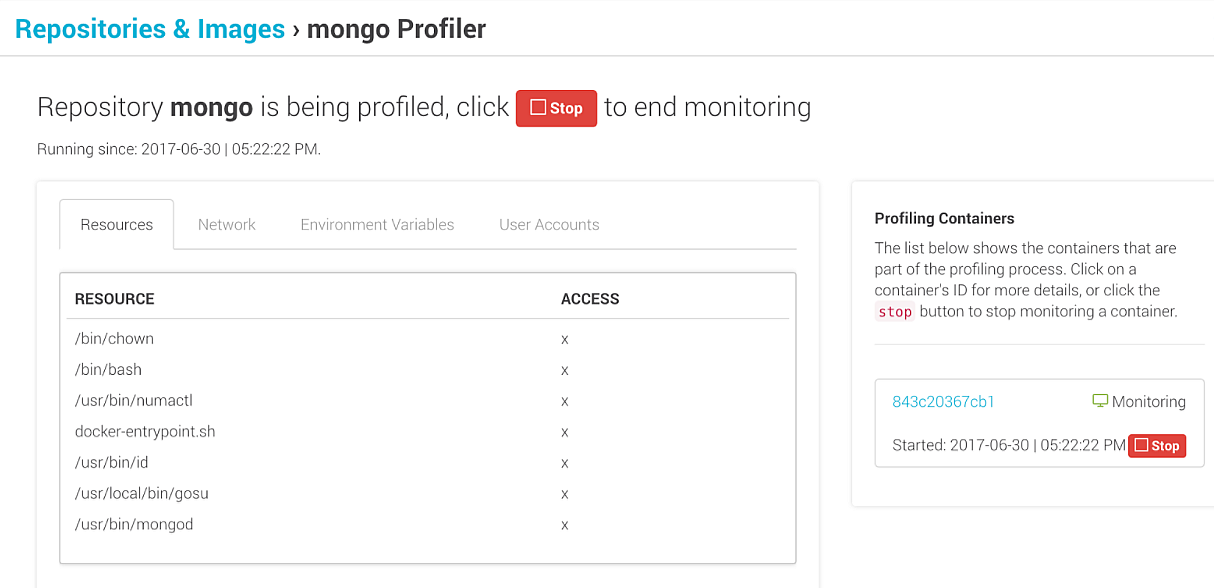
In the screen below, for example, some images already have assigned profiles, while Mongo is being learned.
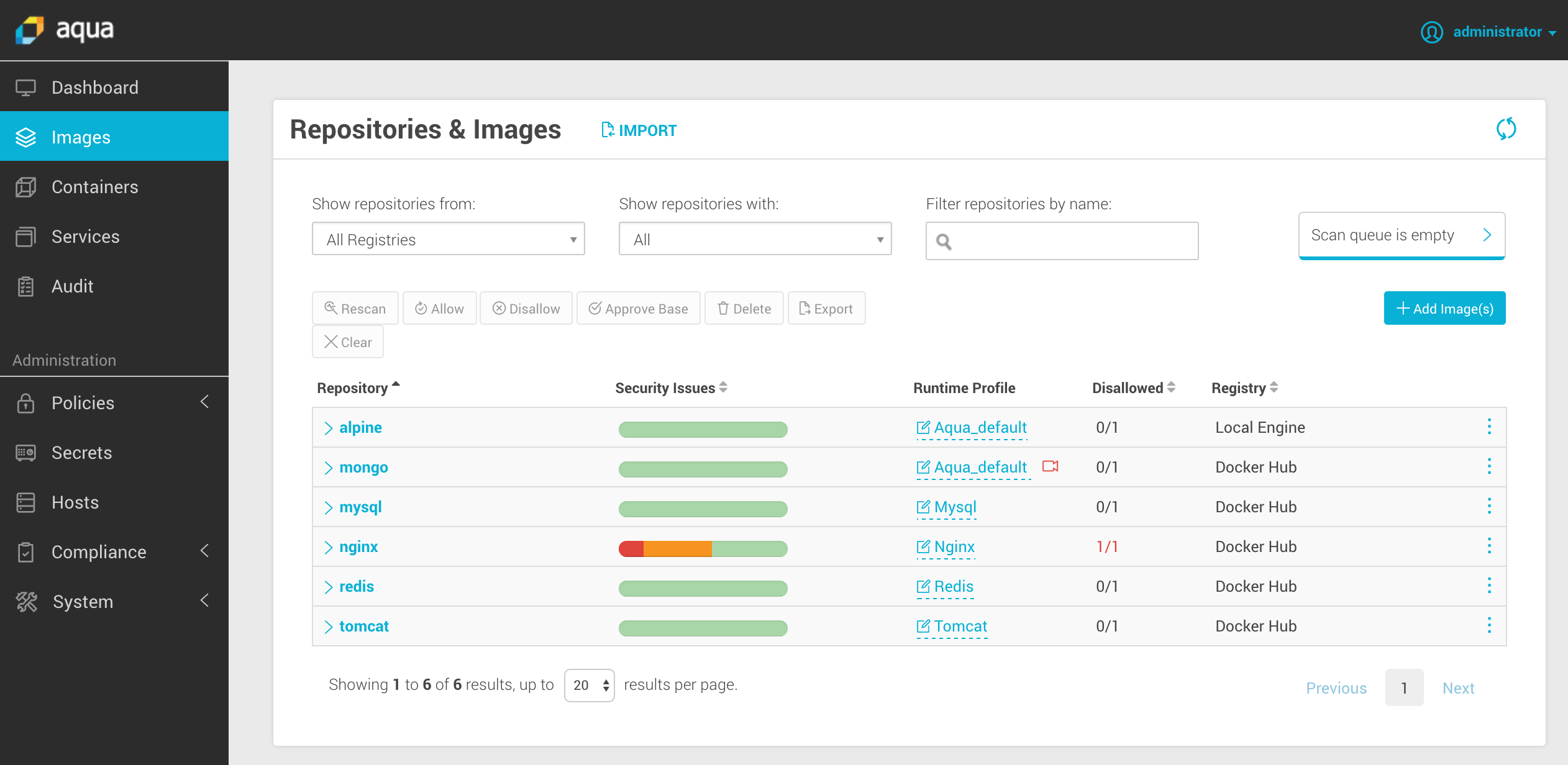
The machine-learned profiles can be viewed and include parameters such as resources accessed, network connections, environment variables and user accounts used.