Hola!
We’ve just returned to Tel Aviv after a fantastic few days in Barcelona at DockerCon 2015, where the place was buzzing with container enthusiasts. Over 1500 Developers, Devops and Sysadmins flocked to the CCIB convention center to learn about what’s new in the Docker container world.
From our booth in the startup pavilion, we had the opportunity to meet lots of Developers who are either contemplating or already using containers for development and are excited about the possibility of using containers in the production stage and beyond. As we predicted, the conference was also great opportunity to meet with the increasing number of startups and tech veterans in the ecosystem, developing solutions for container management, monitoring and storage. To name just a few; DCHQ orchestrates a complete container management environment, from development to deployment; DataDog monitors container and host activity and ClusterHQ provides solutions for distributed persistent storage for containers. The numerous startups and packed conference halls were definitely a sign that the container industry is on the rise.
 In the picture, Scalock Team: Amir Jerbi, Rani Osnat, Dror Davidoff
In the picture, Scalock Team: Amir Jerbi, Rani Osnat, Dror DavidoffThe Security Buzz
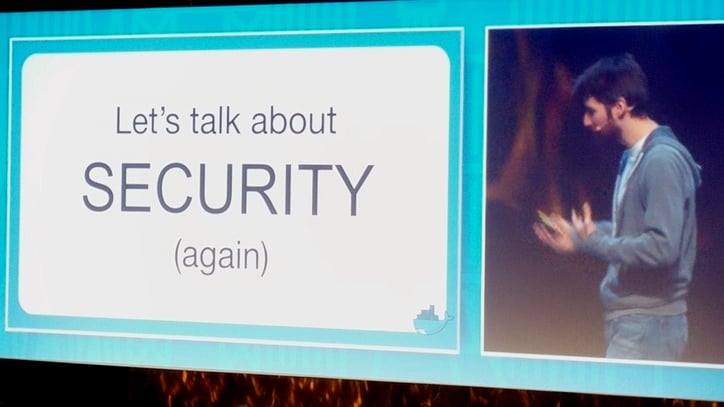
Container security was certainly the hot topic throughout the event. Docker used the conference as an opportunity to present 3 new security tools and features for its containers;
- Support for the new Yubico hardware key for signing Docker images
- User namespace and seccomp support in Docker experimental branch.
- Image scanning as part of Docker Trusted Registry, enabling Docker to scan images and assess vulnerabilities related to outdated code libraries.
Docker founder and CTO, Solomon Hykes, highlighted the importance of container security during his keynote address, which is all too often seen as an afterthought rather than a necessity. “Security needs to be baked in from the start,” he explained. “You need to think about security from the beginning.”
Developers and system administrators can now use YubiKey to sign images as they are pushed to Docker registry. YubiKey is plugged into the USB port of their laptop or workstation to sign the Docker image with their unique identifier. The key ensures that only the intended and designated hands have created or modified the image. Instilling two-factor identification requires the device to recognize the user's fingerprint before they are given access. This makes it extremely difficult for someone to abduct Docker images in transit or spoof it to deliver malware to the intended recipient.
The next security improvement will enable operations managers to assign specific privileges by user group to each container. In the past, each running container had root access to the host (a root on the container is a root on the host). This decision to further control the container privileges on the host will make containers harder to infiltrate.
The final addition to the security suite is ‘image scanning’ that will allow Docker to scan image codes for the correct release number to assess vulnerabilities. If known vulnerabilities are detected, the downloader and supplier will be notified.
So are we now onto safe Docker containers?
The introduction of these features is great news for Docker users and certainly a step in the direction towards container security. The new Yubikey integration is a long overdue feature that will greatly improve the trust we have in images delivered over the wire. Similarly, the vulnerability scanner will ensure image codes are up to date. User namespace and seccomp support will allow more granular controls for container permissions.
Unfortunately, these new additions are still not entirely sufficient to prevent or contain security breaches. Comprehensive container security requires a continuous control and monitoring processes - not a once off. Complete security solutions, such as Scalock, need to be deployed to ensure security throughout the container lifecycle - from development and staging to production. More importantly, container security requires constantly overseeing control points and monitoring containerized application in run-time, in order to alert users to any vulnerabilities and prevent unauthorized usage. Only with these features, can containers effectively move into the production stage and continue to ‘do what they do best’ in a fast, flexible and scalable way.
DockerCon 2016, we’ll be there
The two jam packed days of meetings, presentations, pitching and of course, our party bus sightseeing tour, made for a really great event. Without doubt, the container industry is bursting with innovation and it was a privilege to be able to witness and share in this excitement. Don’t forget to check out our Twitter and LinkedIn pages for more exciting pictures and updates from last week.
We are already counting down the days until DockerCon 2016 in Seattle and we look forward to seeing you all there!


